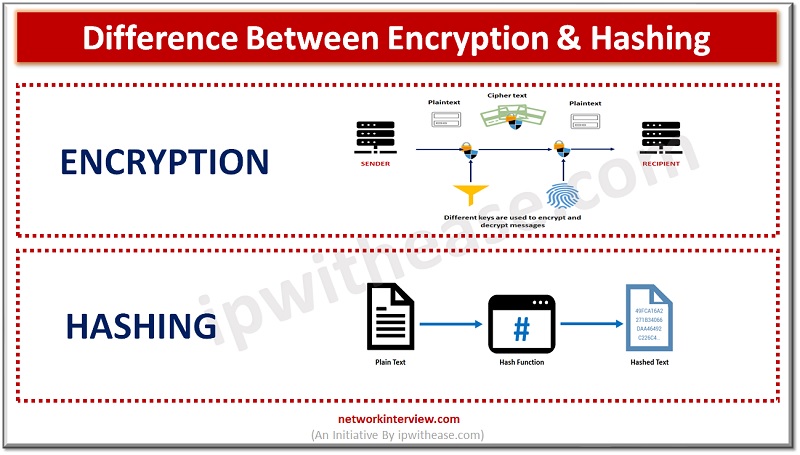
In the realm of data security, hashing and encryption are commonly employed to protect information from unauthorized access. While both methods have distinct processes and advantages, they are occasionally mistakenly used interchangeably. This blog will delve into the definitions of …
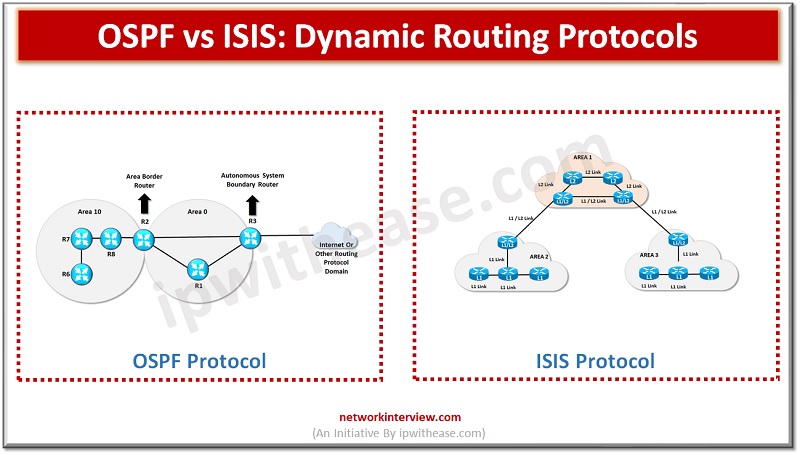
Computer communication networks are growing at a rapid pace, they are based on technology which provides the technical infrastructure, whereas routing protocols are used for transmission of data packets across the Internet. Routing protocols specify how routers communicate with each …
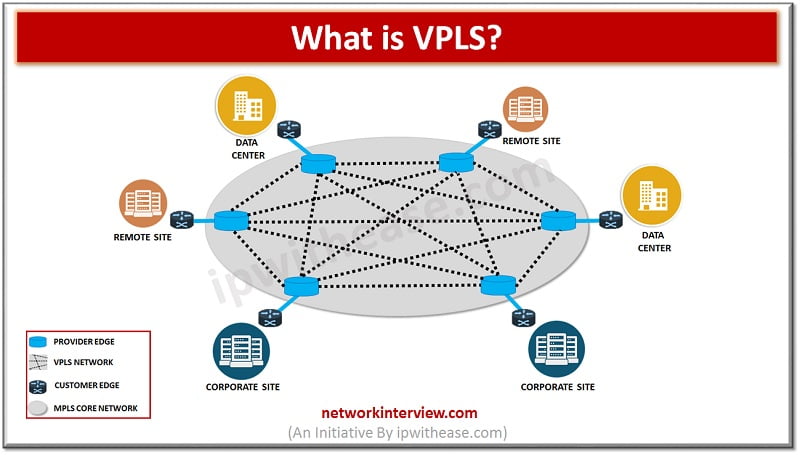
Introduction to VPLS As we have already discussed MPLS in detail in our previous article, so here I will focus on VPLS first and then the differences between the two. VPLS i.e. Virtual Private LAN Service. It is a service that …
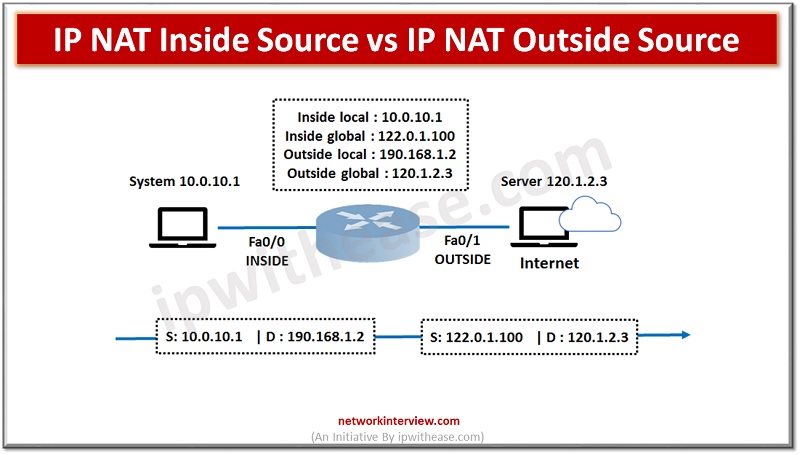
In order to access the Internet, we need one public IP address; however, we can use Private IP address in private networks. The Network address translation (NAT) allows multiple devices to access the Internet with a single public IP address. …
When it comes to software testing, there are two main approaches – manual testing and automated testing. Each one has its own advantages and disadvantages, and it can be difficult to decide which approach is best for your needs. In …
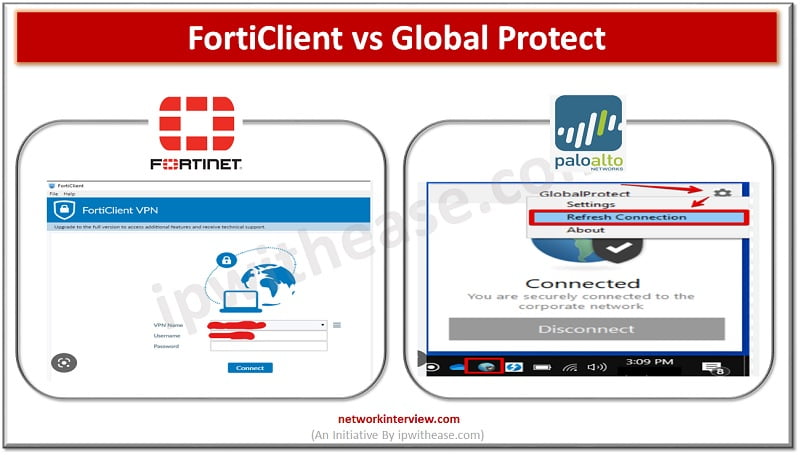
What is FortiClient? FortiClient is an app to provides UTM features like web filtering, giving web security and content-based filtering. FortiClient app is installed in the user’s system and tracks the traffic based on policy. The web application firewall offers malware …
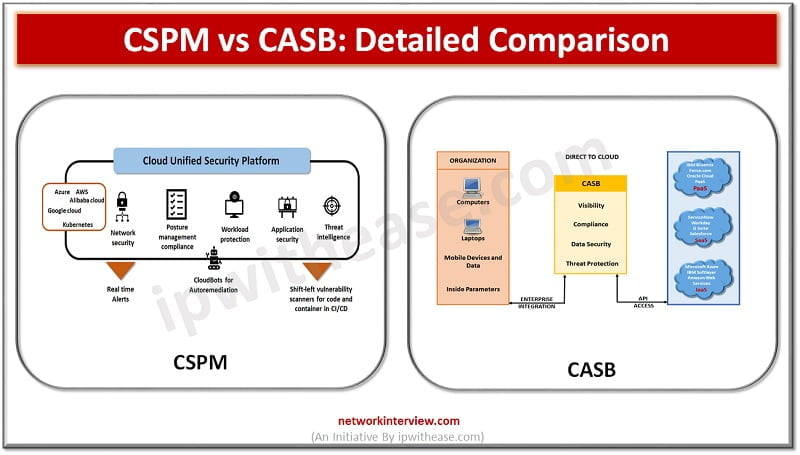
Enterprises are moving their workloads on cloud infrastructure. Gartner forecasts that globally public cloud spending will increase by 18.4% in 2021 to a total of $304.9 billion. As organizations shift IT spend more and more on cloud services, they are …
A common question arises in the mind of IT focals related to Cloud access security broker (CASB) service products such as we already have a web proxy firewall then how is this different? Is CASB a replacement for web proxy/ …
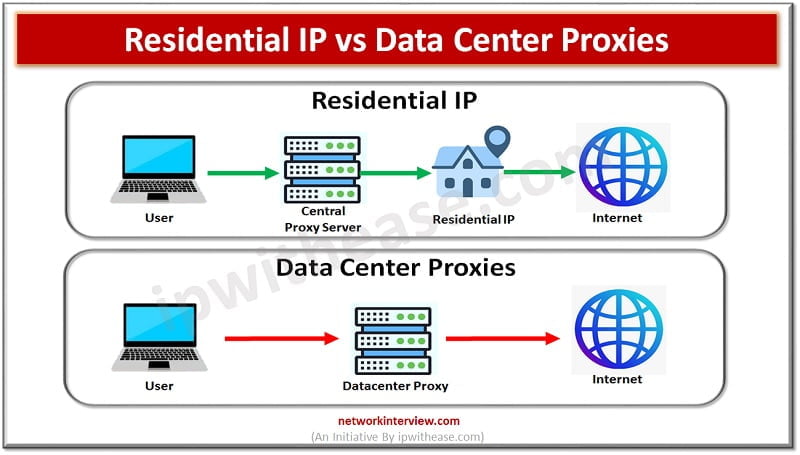
Today, a lot of people use proxy servers to access their accounts, so they may alter their IP addresses and stay out of trouble. The same cannot be said for all IP addresses. There are two types of IP proxies …
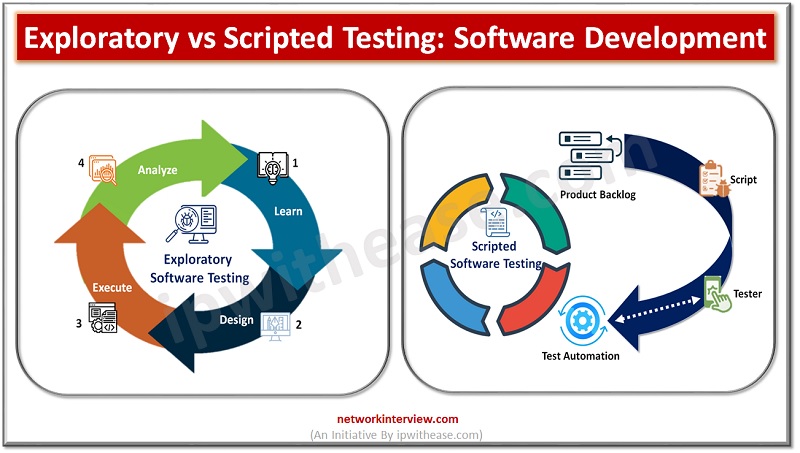
Software testing is a critical component of the software development process. When it comes to software testing, there are two main types: exploratory and scripted testing. Both testing methods have their merits and can be used in different scenarios depending …
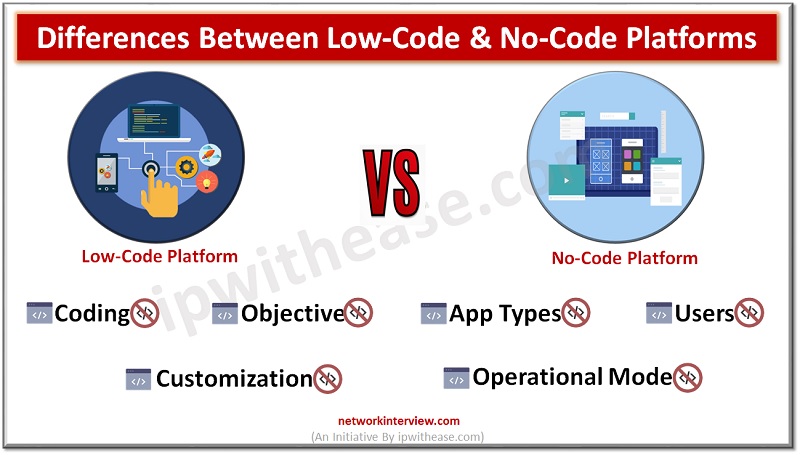
Low-code vs No-code No-code and low-code software are both ways of building apps with limited coding experience. But they each have their own advantages and disadvantages. Choosing the right one for your team and project can help you create an …
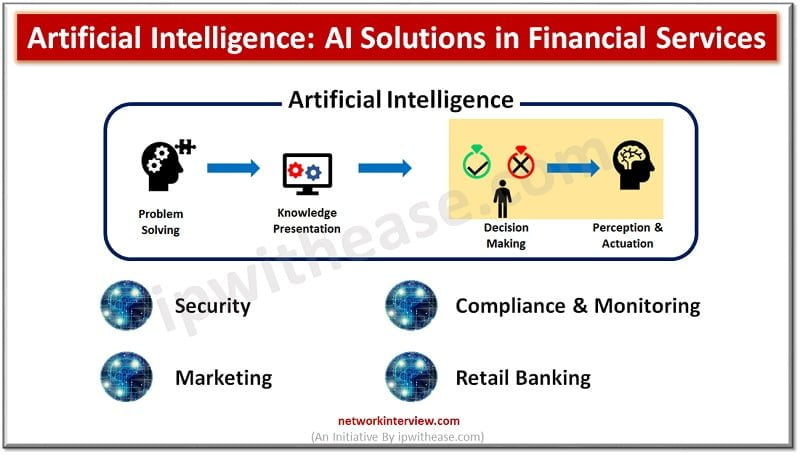
Financial institutions have faced significant challenges in terms of fraud detection, wealth management, investment advice, customer analytics, and so on. These challenges are difficult for human experts to deal with and require an overhauled approach that utilizes artificial intelligence. Artificial …
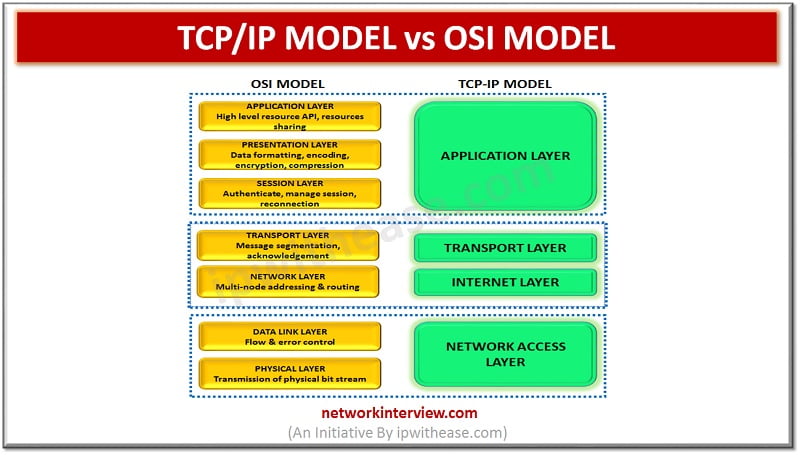
Whenever networks are implemented and different devices try to communicate over the network. Some of the other reference models are being referred to which is a standard specification or framework to provide standardization on how implementation, connectivity, communication will happen. …
Though it’s been a while since cloud technology was introduced into our world still there is much confusion surrounding Network Security and Cloud Security. If you are one of those who can’t find the difference between these two terms: Network …
Are you planning to get a career as a Web Creator? Then you will be confused between the Web Designer and Web Developer. As there is still a lot of confusion surrounding these job roles. Both of them help to …
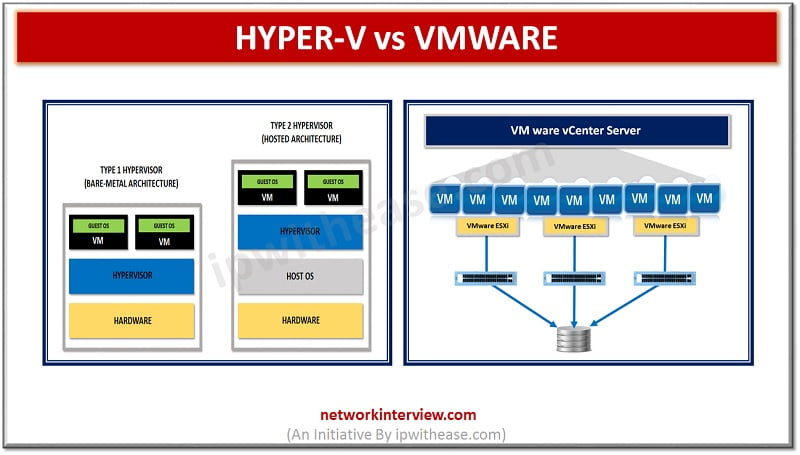
Hyper V vs VMware In computing, virtualization refers to the act of engendering a virtual version of one thing, as well as virtual constituent platforms, storage contrivances, and electronic network resources. On a very broad level, there are 3 styles …
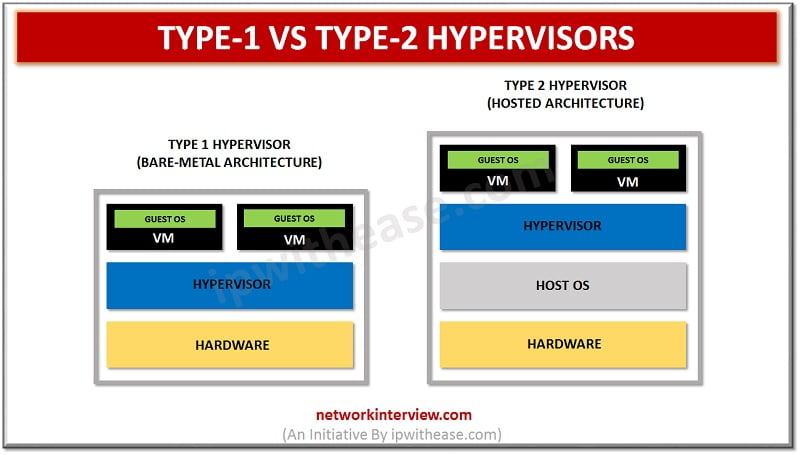
Type-1 vs Type-2 Hypervisors Server virtualization is perhaps the sultriest point in the IT world today. It has been around for a long time, and its ubiquity continues developing, particularly in big business environments. What makes virtualization conceivable in hypervisors? …
XEN vs KVM Talking about the virtualization concept, hypervisors technology is quite a well-known concept. A hypervisor is used by a person who would wish to merge the server space or run a number of other independent machines with the …
Xen and ESXi are unique form of type-1 hypervisors that are specially built for deploying and serving the virtual computers. There can be various kinds of similarities between the two, but here our aim is to bifurcate both of them …
Every new technology or software invented goes under this question “Is it secure?” That’s how security is always considered an important feature in the digital era. But do we understand them clearly? Over time security is classified further into cloud …
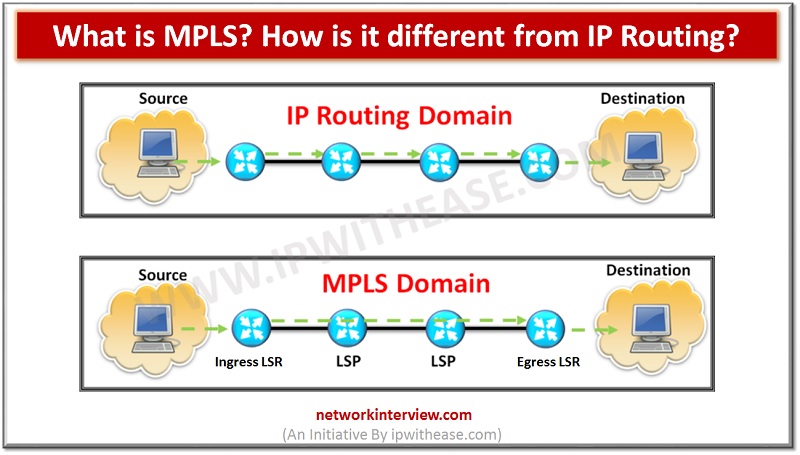
Introduction to MPLS MPLS i.e. Multi Protocol Label Switching (MPLS). It is a technique that is used for the routing of network packets. It is called a Multiprotocol as it supports multiple protocols like Internet Protocol (IP), Asynchronous Transport Mode …
In the hosting web sector, there is a lot of confusion regarding the technological differences between cloud hosting and VPS hosting. Most people misinterpret the fundamental distinction between the two due to the lack of understanding of the key distinctions …
Have you ever bought a Samsung Phone which has a different processor than your friends? Yes, the Samsung Mobiles uses two processors for all their models. The mobiles with Exynos processors are sold in Asian and European countries whereas the …
Hey guys, here is another neck-to-neck comparison. Recently Snapdragon and Kirin have announced their new model which has created waves among tech enthusiasts. You can’t decide the winner until they are released, but so far who is the winner? If …
Hybrid Cloud vs Multi Cloud In recent years, with mushroom growth in Cloud technologies, a change has been observed w.r.t where the application Workload and data is hosted. A large number enterprises have started moving their data, applications and related …
When selecting a smartphone or tablet one of the important features to check is the Processor. To be correct they are not processors in the technical circle, it’s called System on a Chip (SOC). The Snapdragon and MediaTek are the …
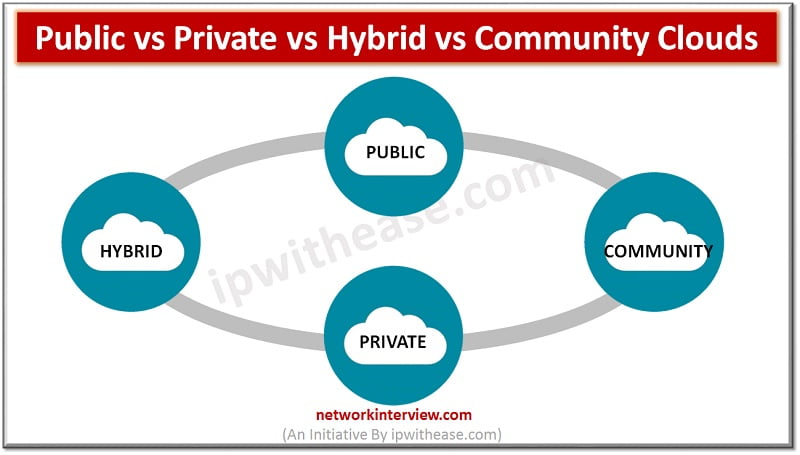
Types of Cloud: All size of businesses receive prominent advantages from cloud computing. When part or all of the computer resources of a company are moved to the cloud, then the decision of most suitable cloud services is also included …
Telco Cloud vs IT Cloud Cloud computing has opened a breath for enterprise and telecom related opportunities to hosting applications and services. While market talk is that somewhere in near future IT Cloud and Telco Cloud will merge to form …
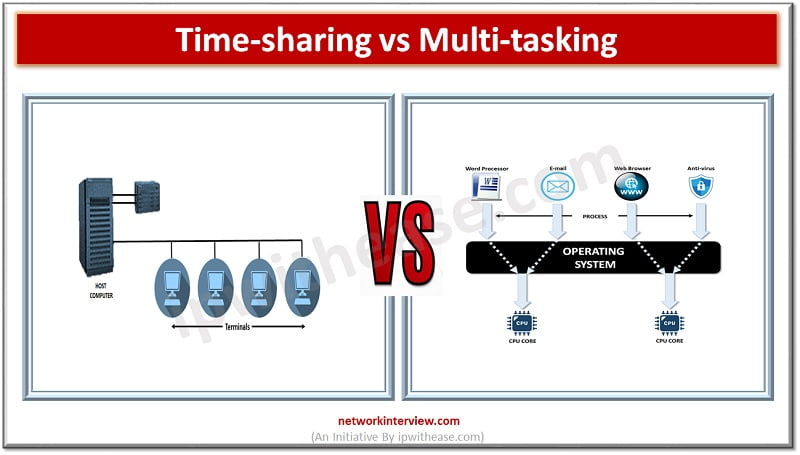
As a modern computer user, you may not know that multi-tasking and time-sharing operating systems are two different things. Though they both are similar and dependent on each other, there are some differences between them. Wait, are you saying they …
Introduction to Pre-sale & Post-sale Specialization of sales engineers should be in technology and scientifically advanced products. With the help of technical skills, they explain the advantages of the products or services to the potential customers and also tell how …
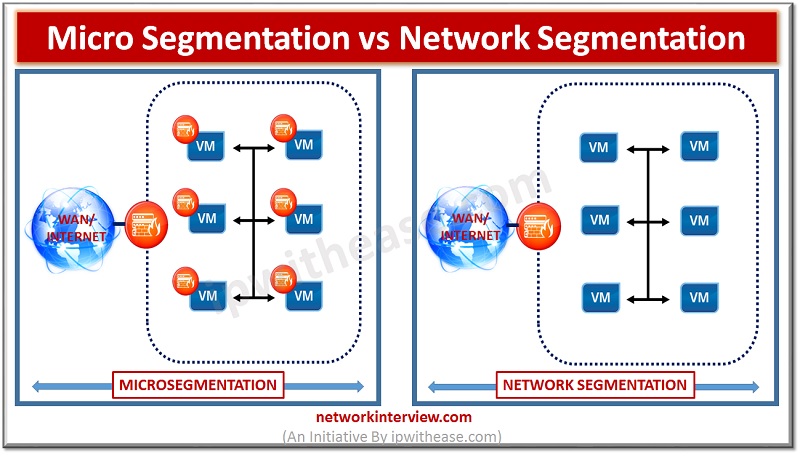
Micro segmentation vs Network Segmentation Over many years, Perimeter security has been considered the key to presenting a robust and secured network ecosystem . This was considered a suitable methodology when the network attacks were not so advanced and North-South …
Cloud Engineer vs DevOps Engineer Cloud has changed the way how we do Business. Cost savings have led the IT assets, especially compute Infrastructure migration to Cloud. Accompanied by this move, there have been buffet of new roles which have …
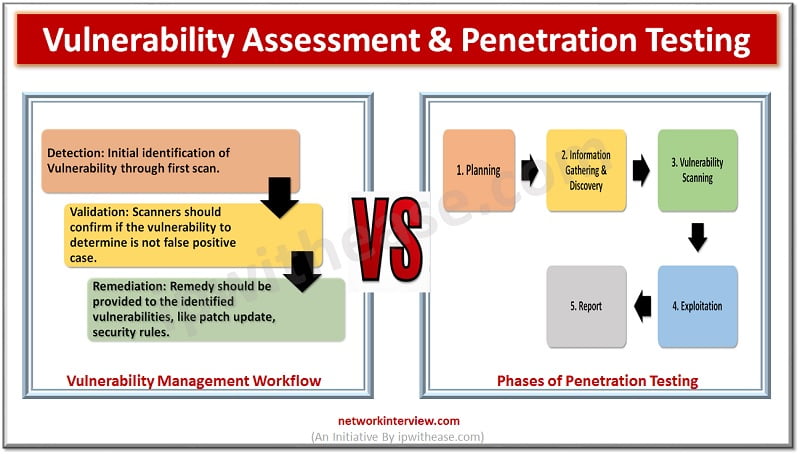
Introduction Vulnerability assessment is the way to identify weakness in the system. Vulnerability itself means “Weakness” and Vulnerability assessment means how to find weakness in a system and create a report accordingly. On the other hand, Penetration testing is used …
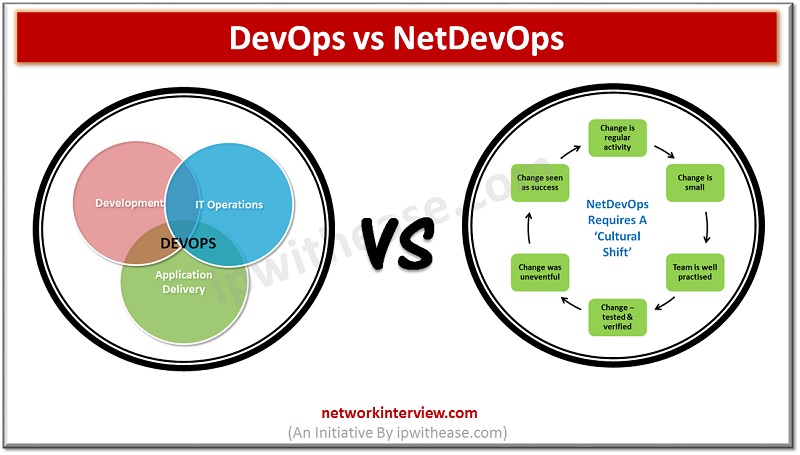
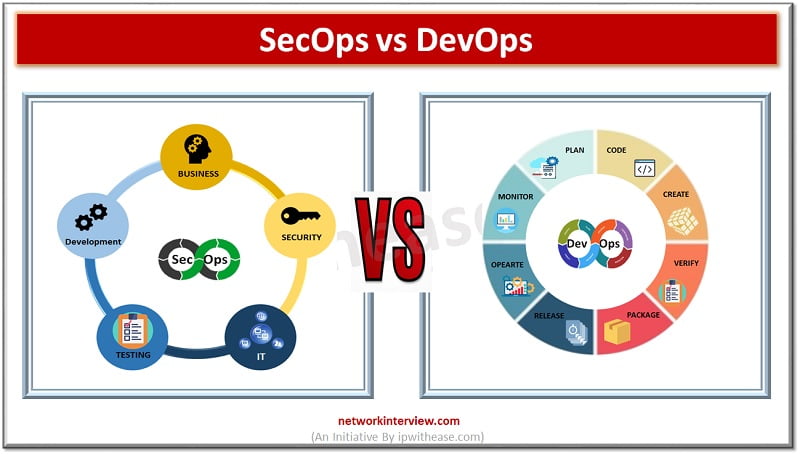
Introduction With the growing advancement in technology there is an increasing need for collaboration and Agility. Software developments require a constant collaboration between programmers and system administrators in the software development process to develop apps which are efficient, secure and …
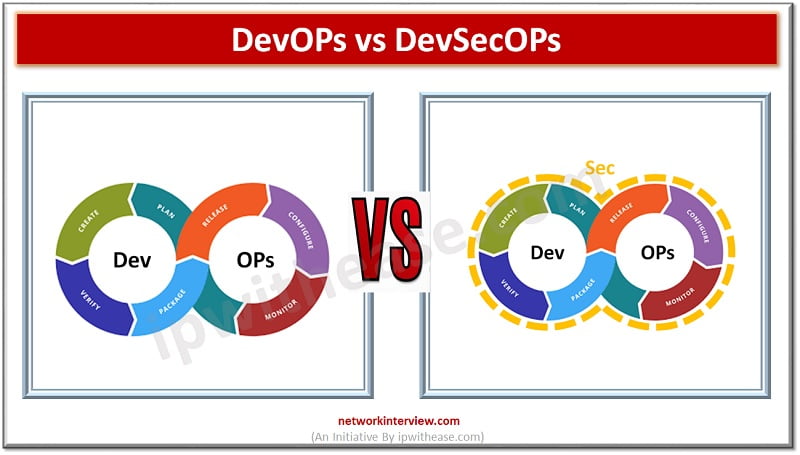
Software development and operations teams are always striving to establish a consistent environment for development globally. The products are brought from hands of developers to customers however the existence of silos between development, QA and operations teams always create conflicting …
Infrastructure as a code is one of the greatest changes brought by DevOps in recent times. Complicated provisioning, deployment and release of cloud infrastructure processes which required following complicated steps where cloud resources were created manually is a thing of …
Introduction to Agile Methodologies Most organizations are adopting agile methodology to enable better collaboration between customer and the IT. With Agile the power of teamwork is unleashed. Agile is an iterative approach which concentrates on a continuous delivery framework. The …
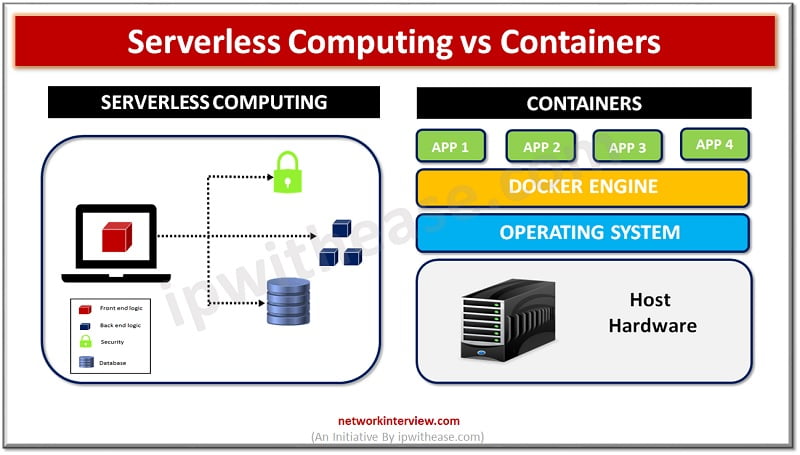
Introduction In the era of enterprise computing organizations are seeking ways to develop, deploy and manage applications in a more efficient , fast and scalable manner. Traditionally applications are tightly linked to servers and the operating systems which executed their …
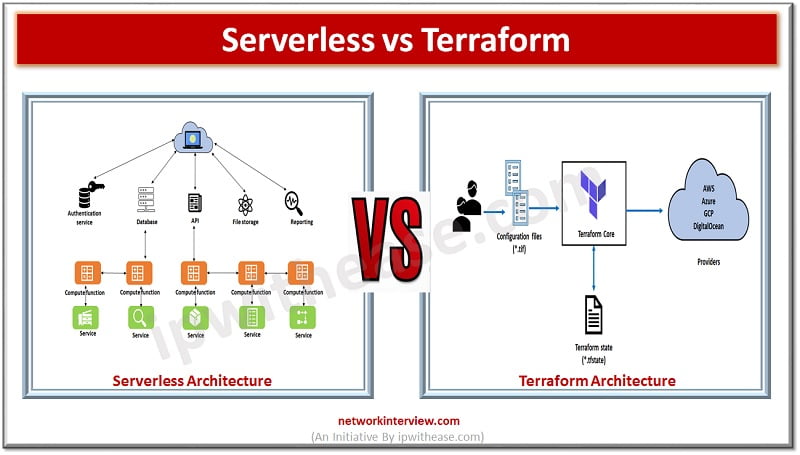
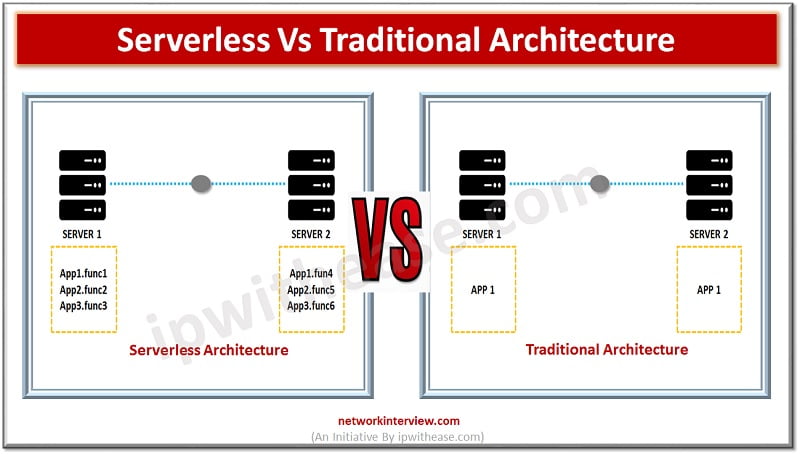
Introduction to Serverless Architecture Over the years organizations have invested money in buying costly servers. The traditional architecture requires large IT staff for maintaining data centres, training and hiring skilled personnel, tracking obsolete hardware and replacing it which would bring …
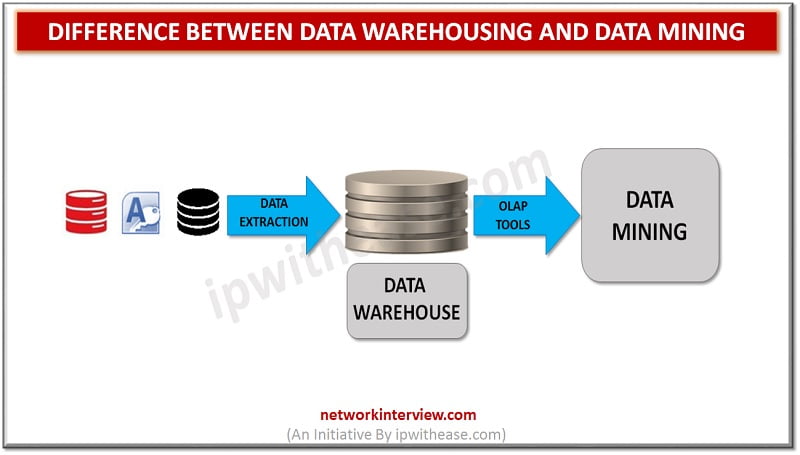
Before discussing difference between Data Warehousing and Data Mining, let’s understand the two terms first. Data Warehousing Data Warehousing refers to a collective place for holding or storing data which is gathered from a range of different sources to derive …
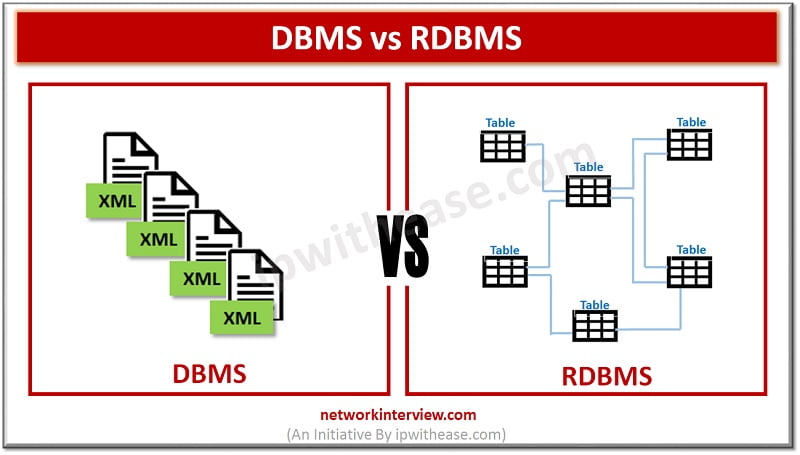
The data world is constantly evolving and changing, this in turn has created a necessity to have a solution, software or technology in place to handle the data in the proper manner. The need to create and manage properly is …
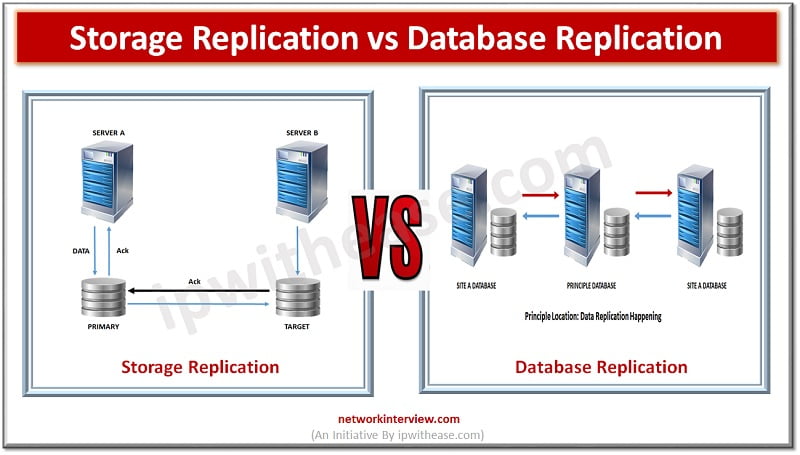
Mission critical Business applications require uninterrupted availability of systems. Use of ‘Replication’ technologies let IT environments deliver robust data protection for the enterprises. Today we look at some replication technologies ! Storage Replication Storage replication technology enables replication of volumes …
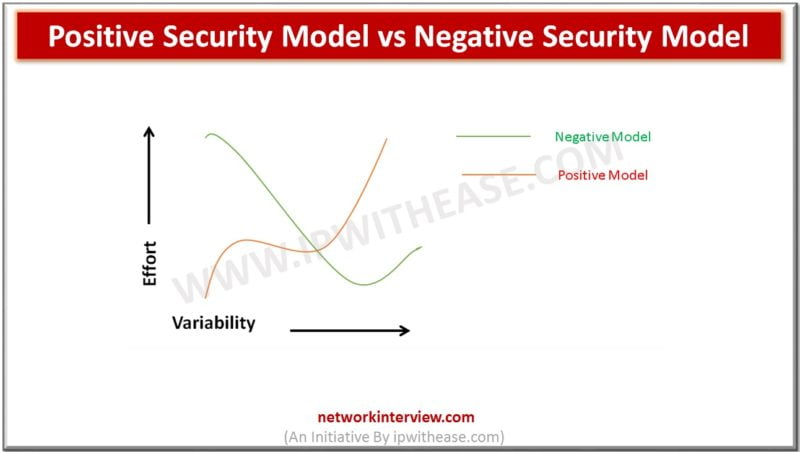
Introduction : Positive Security Model & Negative Security Model Achieving highest level of security and being one step ahead from the hackers has always been a significant challenge for any IT company. Security is always a hot discussion topic whenever …
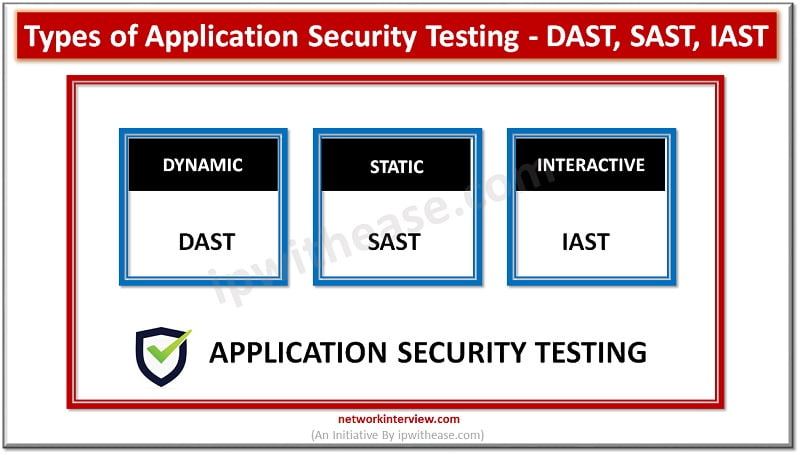
Introduction to Application Security Testing Application Security testing is an integral part of SDLC (Software development lifecycle) and used to discover the weaknesses, risks or threats in software applications and help to detect vulnerabilities hidden in applications which can be …
If you are a tech enthusiast or experienced with Cloud services, then you should have come across the word Big Data and Cloud Computing. Though they are often used together they have different meaning purposes. Are you new to this …