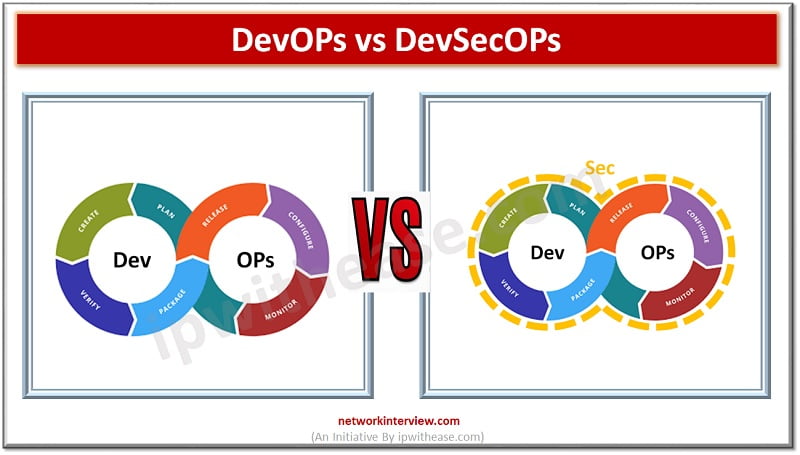
DevOps vs DevSecOps: Understand the difference
Software development and operations teams are always striving to establish a consistent environment for development globally. The products are brought from hands of developers to customers however the existence of silos between development, QA and operations teams always create conflicting interests and it is doubled when requirements of security are also required to become an integral part of software development.
Today we look more in detail about DevOPs and DevSecOps strategy and principles, how they work, what are their advantages etc.
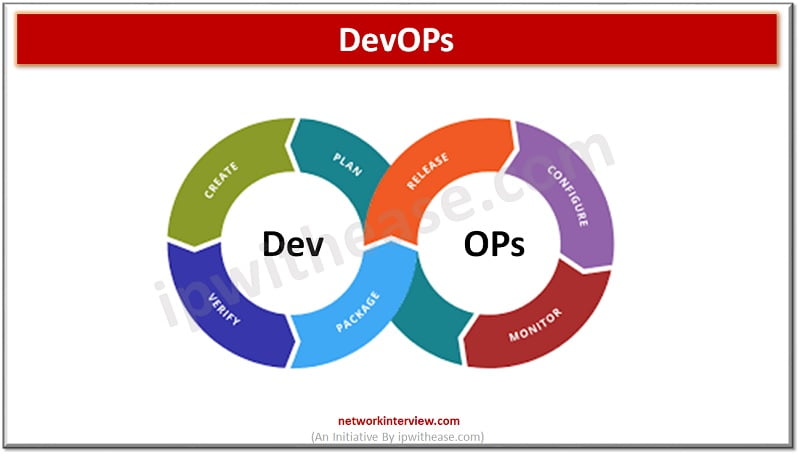
About DevOps
‘DevOPs’ is a combination of two words ‘Development’ and ‘Operations’. It represents a set of principles, ideas, practices and tools which helps an organization to increase its ability to deliver applications and services with improved efficiency and at a much faster pace instead of traditional methods of development. It is a software development strategy which aims to bridge the gap between development teams and IT operations teams. The IT operations team and development team work in collaboration during the entire software development lifecycle to produce better, reliable applications and products.
Advantages of DevOps
- Improved customer satisfaction and retention
- Business efficiency improvement
- Improved response times
- Reduction in costs over time
- Improved business agility
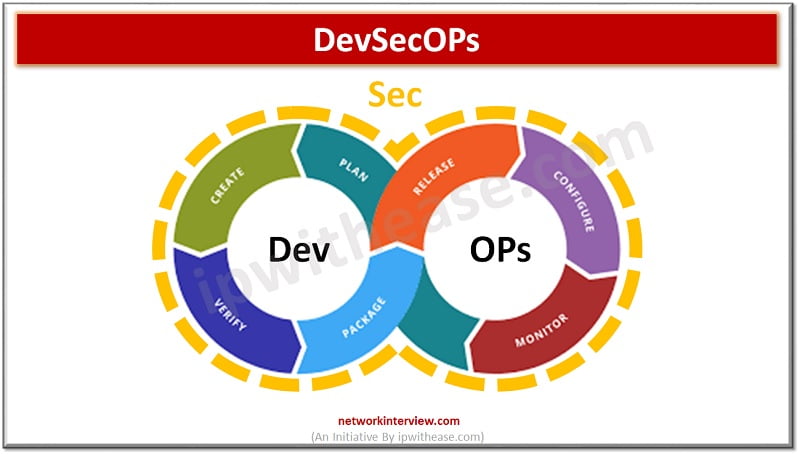
About DevSecOps
The DevOPs offers speed and quality development and deployment but it does not cater to needs of security. The focus on security has increased tremendously hence DevSecOps has come into picture. DevSecOps optimizes the DevOPs strategy by security automation and implementation. It breaks silos between development teams and security teams and empowers development teams not only to be responsible for performance of applications in production but also accountable for product security in production.
The goal is to focus on security requirements right from the beginning of software development life cycle and provide built in security practices throughout the integration pipeline.
Developer responsibilities in DevSecOps
- Composition analysis in conjunction with security to choose safe third party and open-source tools
- Static and dynamic analysis of code along with automated vulnerability scans and penetration tests
- Automated tests alongside functional tests and check and verify against improper security configurations
- Threat modelling adoption to understand how attackers think and operate
Comparison: DevOps vs DevSecOps
Below table summarizes the differences between the two:
Function | DevOps | DevSecOps |
| Definition | DevOPs is a combination or unification of “Development’ and ‘Operations” . It is a set of principles and strategies to increase organization ability to deliver application and services with improved efficiency and at a faster pace | DevSecOps is a combination or unification of ‘Development’ , ‘Security’ and ‘Operations. It focuses on incorporation of security practises in development |
| Methodology | It is a software development methodology which aim to bridge gap between development and IT operations team and hence their collaboration during entire software development lifecycle | It is a methodology which is integrated into DevOPs process to incorporate security at every stage of software development process |
| Goal | Breakdown organization silos and adoption of a culture where people work together by developing and automating continuous delivery pipeline | Goal is to move security activities throughout the software development lifecycle and provide built in security practises throughout the continuous integration pipeline |
| Approach | Based on cultural philosophy which support agile movement in the context of system-oriented approach | It is about validating all building blocks and embed security in architecture design |
| Elements | CI/CD are critical elements of DevOps , automation of code development process let teams change code more frequently and in reliable manner | Shift left is most critical element in DevSecOps making security core responsibility for each and everyone involved in development and identifying issues early and fixing them quickly |
| Tools | Ansible, Docker, Puppet, Jenkins, Chef, Nagios, Kubernetes etc. | Aqua Security, Codacy, Checkmarx, Prisma cloud, Threatmodeler etc. |
Download the comparison table: DevOPs vs DevSecOPs
Continue Reading:
SecOps vs DevOps: Understand the difference
Cloud Engineer vs DevOps Engineer : Future of 21st Century
Tag:cloud, comparison, virtualization



