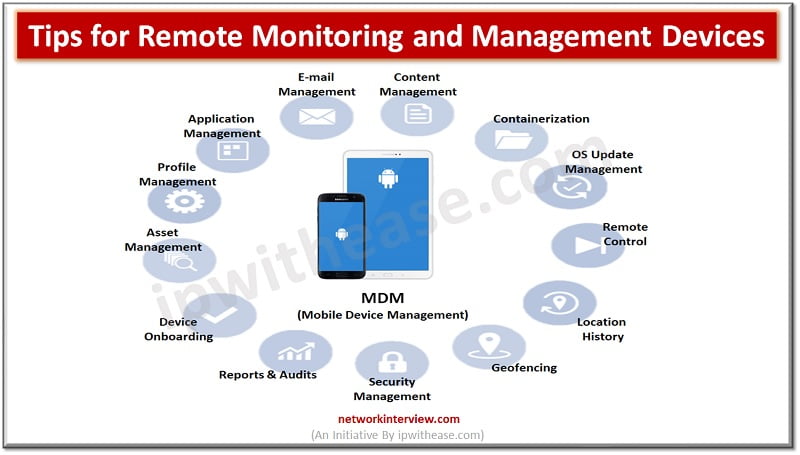
In today’s fast-paced and interconnected world, businesses rely heavily on technology to streamline their operations and stay competitive. With the rising quantity of enterprise devices and the increasing complexity of IT systems, it has become essential for companies to manage …
As a small business owner, one of the most essential decisions you’ll ever make is choosing the right employees for your company. Employees are, no doubt, the most precious asset for the success of every organization. Interestingly, there has never …
As companies use Amazon Web Services, it is essential to manage costs. Given the nature of cloud utilization, the need to watch out for unexpected expenses becomes necessary. This is where AWS Cloud Cost Optimization Tools step in as game …
SEO, or Search Engine Optimization, is the process of optimizing online content and websites to enhance their visibility in search engine results. The main objective of SEO is to attract relevant organic traffic to websites, increasing the likelihood of converting …
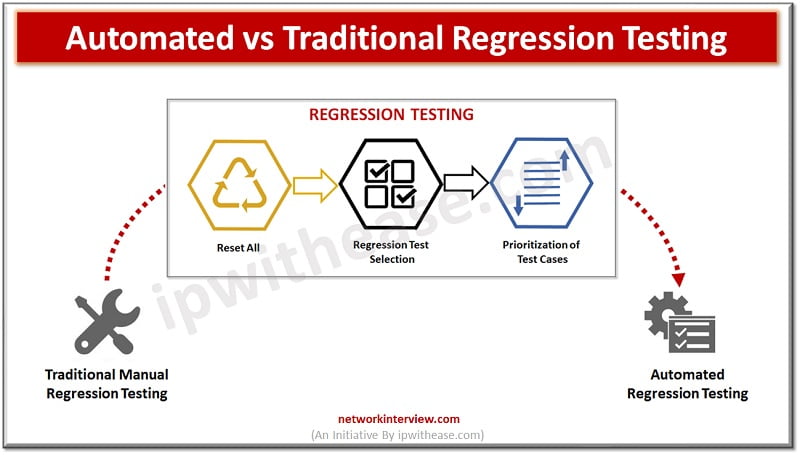
In the field of software development, testing procedures are always changing as a result of the desire to produce high-quality products while preserving agility. Regression testing is one of them and is crucial in verifying that new code changes don’t …
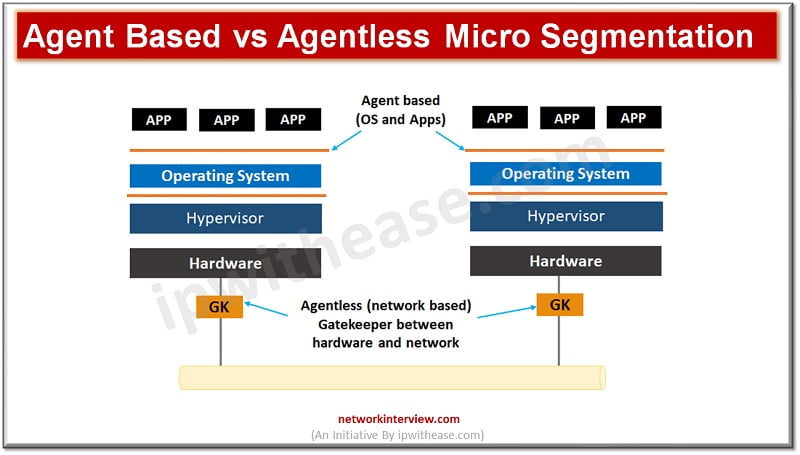
Granular level management of access and security controls is the focus of security techniques deployed nowadays as attacks have become more and more sophisticated so is the dynamics of protection also getting changed frequently. Virtually restricted access to any device …
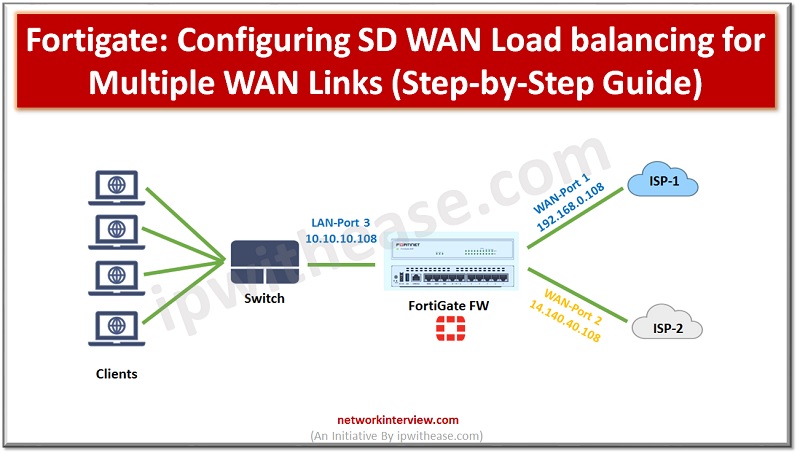
Configuring SD WAN Load balancing Below is the network setup on which we will configure FortiGate SD-WAN with load balancing for two different ISPs. Parameters which we have taken are LAN Port & Segment -> LAN Port 3 & 10.10.10.108 WAN …
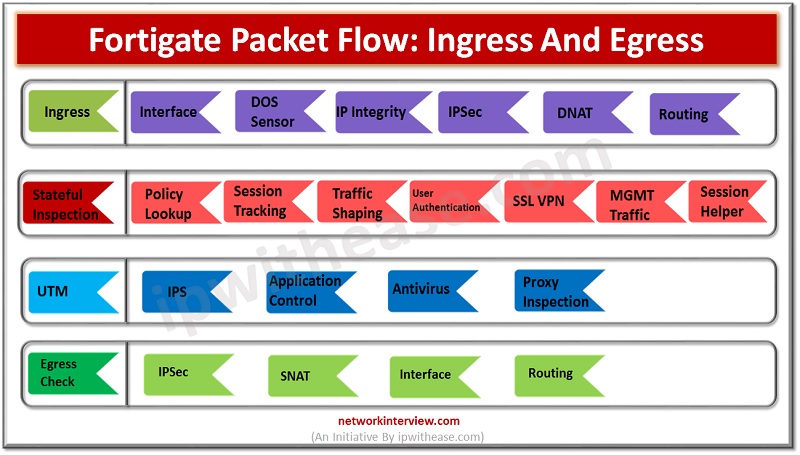
FortiGate packet flow is also known as Life of a Packet. This is the process when the packet enters the Ingress interface and exits from the Egress interface. Stages of FortiGate Packet Flow FortiGate packet flow consist of 4 stages …
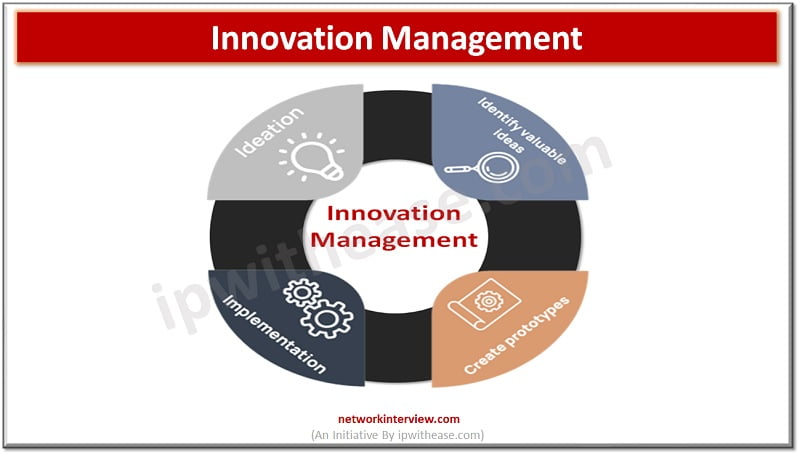
Innovation has become a cornerstone of success in today’s fast-paced and ever-evolving business landscape. Organizations that consistently generate and implement novel ideas are better positioned to adapt to change, meet customer needs, and stay ahead of the competition. To foster …
Data science is a new buzzword in the contemporary business landscape. Organizations leverage data science tools and techniques to find data patterns and make insightful data-driven conclusions and predictions. As a result, the demand for data science graduates is on …
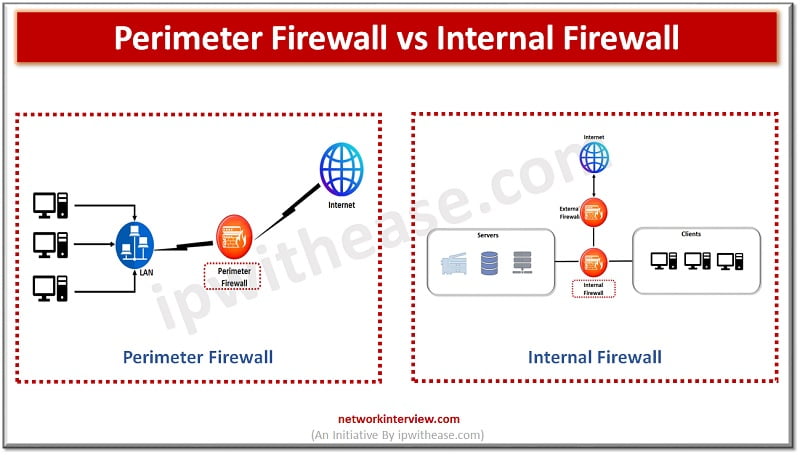
Firewalls have come a long way since their inception in the year 1908s. The initial firewall was built by Digital Equipment Corporation (DEC) as a packet filtering firewall which simply inspected packet traffic and if it doesn’t match rules packet …
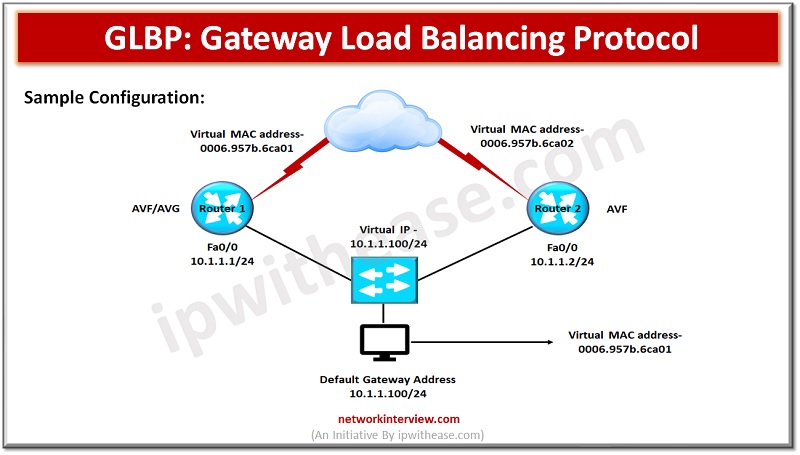
Introduction to Gateway Load Balancing Protocol Load balancing is one of the key requirements in networks and it can be achieved in several ways such as round robin, host dependent and weighted. Protocols supporting load balancing have the capability to …
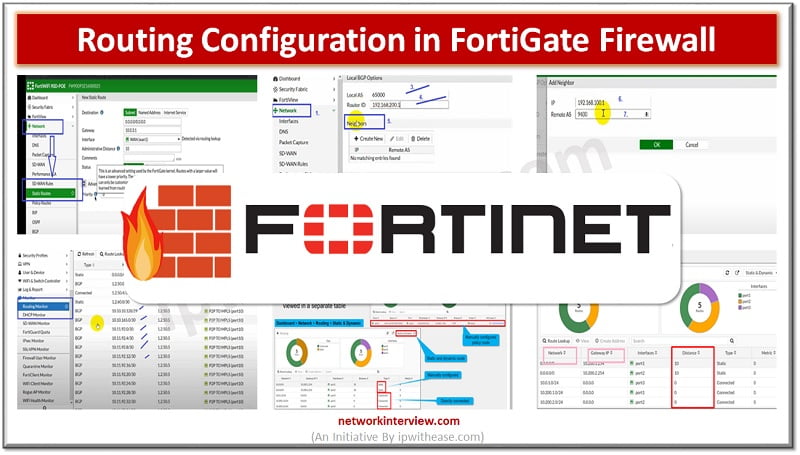
Objectives Routing in Fortinet FortiGate Configuration Steps of Static Routing Configuration Steps of Dynamic Routing (BGP) Policy Base Routing Routing Monitor GUI Troubleshooting Commands for Routing in FortiGate Routing in Fortinet FortiGate Firewall Routing means how a packet can …
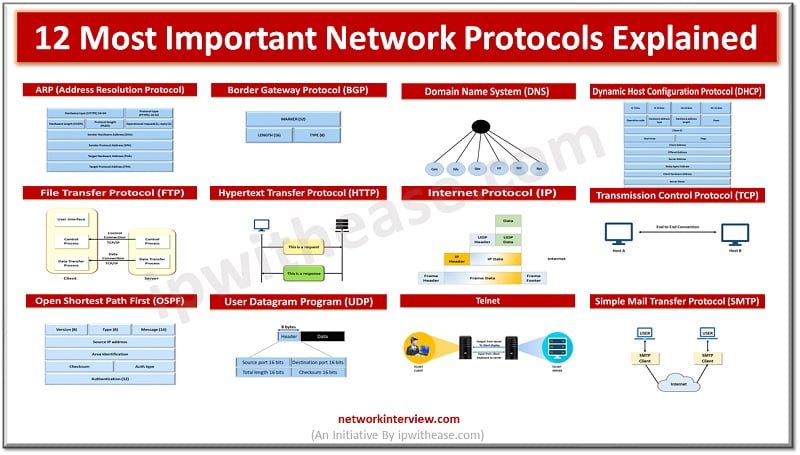
Network protocols establish rules of communication to control and govern exchange of information following secure, reliable methods. These are a set of rules designed to have a standard framework for interchange over networks. There are a variety of network protocols …
Single Sign On & FortiGate Single Sign On Single Sign On (SSO) is a process that allows users to automatically log into every application after being identified, regardless of platform, technology, and domain. FortiGate Single Sign On (FSSO) is a …
Hiring the right candidates for a vacant job position is crucial for any organization’s success. The process of finding the perfect fit can be daunting, as it requires a delicate balance of skill, experience, cultural fit, and potential for growth. …
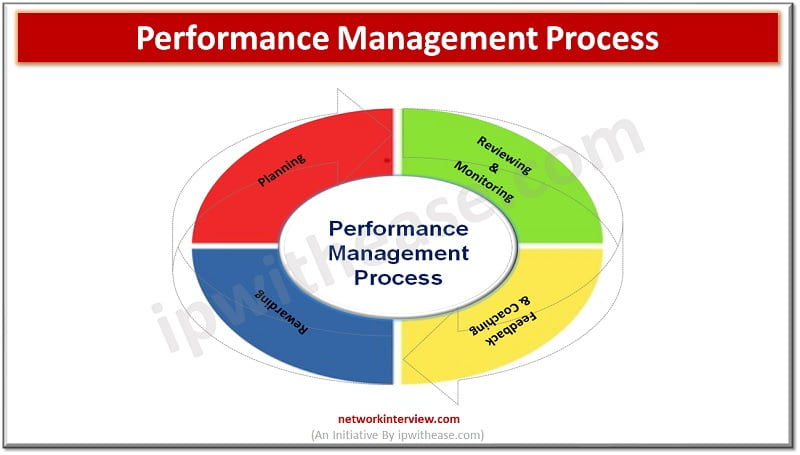
In the dynamic and ever-changing world of business today, companies continuously strive to outperform their competitors and attain long-term prosperity. A fundamental component in achieving organizational greatness is the implementation of a strong performance management process. This system encompasses multiple …
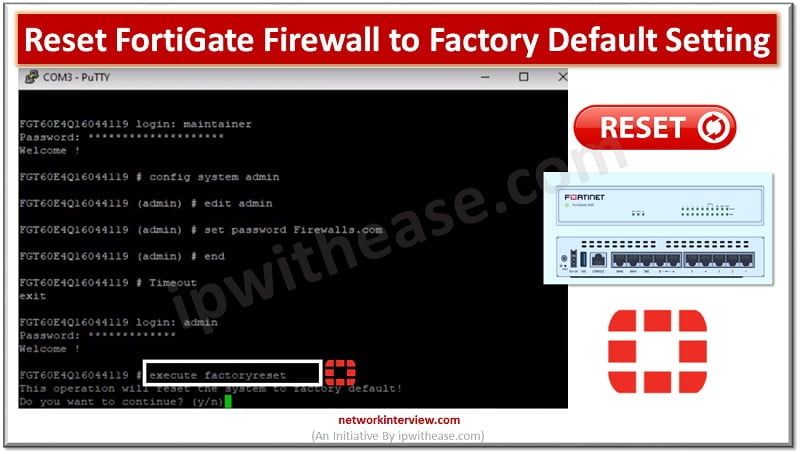
Factory default means resetting the device to the original default configuration and deleting all customized configuration from the firewall/device. Why do we need to reset the firewall to factory default? Device is crashed and need to remove from network Remove …
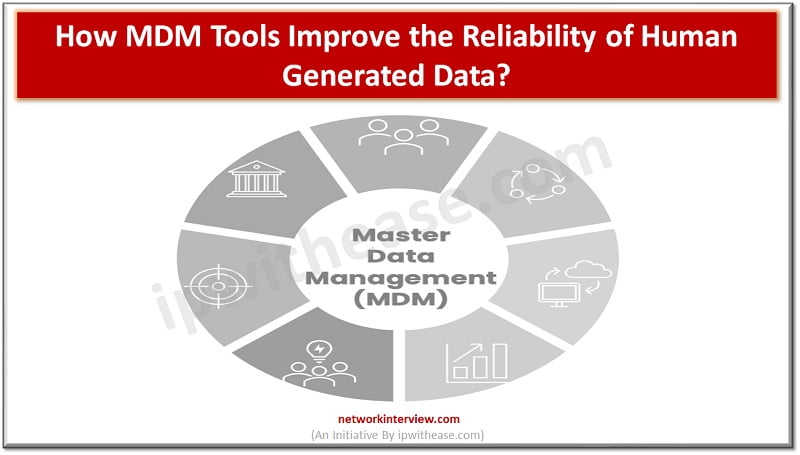
As we move into an increasingly digital world, businesses must collect and manage up-to-date data easily. Manual storage processes are often inadequate and unreliable, especially with large customer datasets, putting organizations at a disadvantage. Fortunately, Master Data Management (MDM) tools …
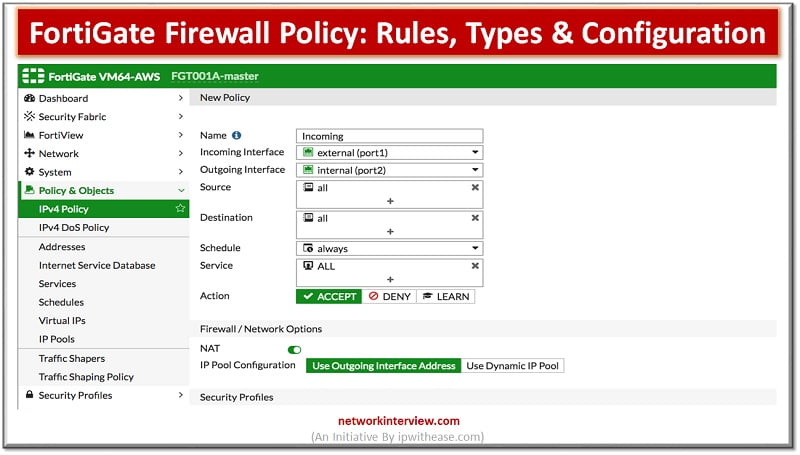
What Are Firewall Policies? Firewall policies define which traffic matches them and what FortiGate does when traffic does match, should the traffic be allowed? Initially FortiGate basis this decision on simple criteria, such as the source of the traffic then …
The CSPO (Certified Scrum Product Owner) certification is considered prestigious for individuals aiming to succeed in Agile product management. With the increasing popularity of Agile methodologies in various industries, obtaining a CSPO certification can unlock various career prospects and showcase …
In today’s digital age, the security of user access rights has become more important than ever before. Managing user access rights is a crucial task in any organization that deals with sensitive data. The rise of distributed systems has made …
Advancements in technology have revolutionized our lives, simplifying the achievement of various goals and tasks. Among these technological advancements, ai voice generator tools play a significant role in enhancing convenience and understanding. TTS ( Text to Speech) enables influencers to …
What was once restricted to academic discourses and testing facilities has evolved into things that are more accessible to the general public. This surge of Artificial Intelligence has penetrated the human realm. Artificial intelligence (AI) chatbots are at the forefront …
Regression testing plays a critical part in software development by verifying that modifications or upgrades to a program do not generate new faults or disrupt current functionality. However, since regression test suites may frequently be extensive and time-consuming, selecting test …
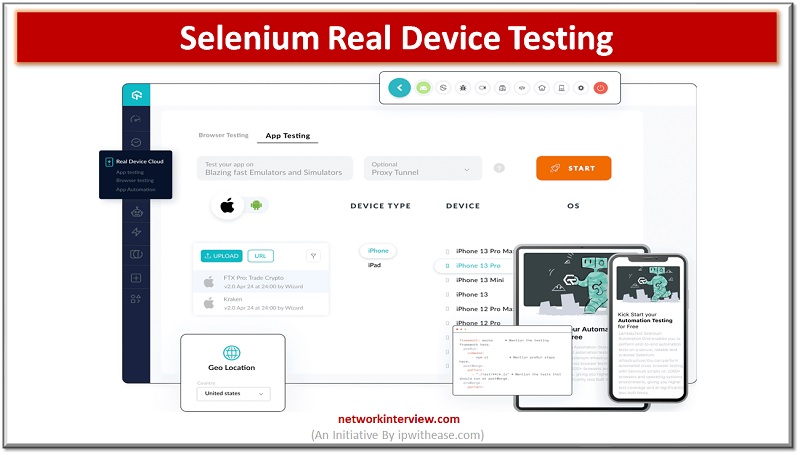
Selenium Real Device Testing A hugely well-liked open-source framework called Selenium enables programmers and testers to automate web browsers and produce automated tests that perfectly mimic user interactions with web applications. The use of strong error handling and reporting techniques …
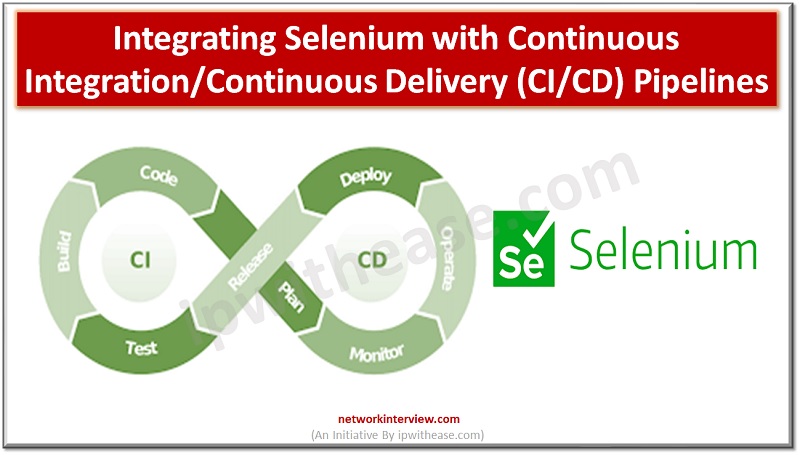
Introduction to Continuous Integration/Continuous Delivery The contemporary practice for application development included separating the development process into three separate stages. These included the development, testing, and the production phase. The application developers separated these phases, which means that the next …
Artificial Intelligence and Machine Learning are two emerging concepts which are playing a very crucial role since the Covid pandemic hit us. Both technologies are being used to study the new virus, test potential medical treatments, analyse impact on public …
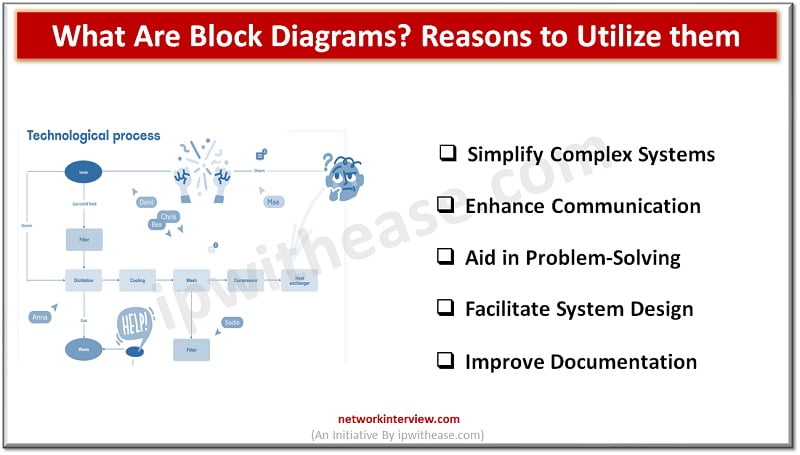
Block diagrams are powerful visual tools that help simplify complex systems and processes by breaking them down into interconnected blocks or functional units. They provide a high-level overview of the components and relationships within a system, enabling teams to better …
Firewalls are the primary line of defense for organizations; they are there for more than three decades but evolved and came a long way with drastic features and also sold now as separate appliances and make smarter decisions about what …
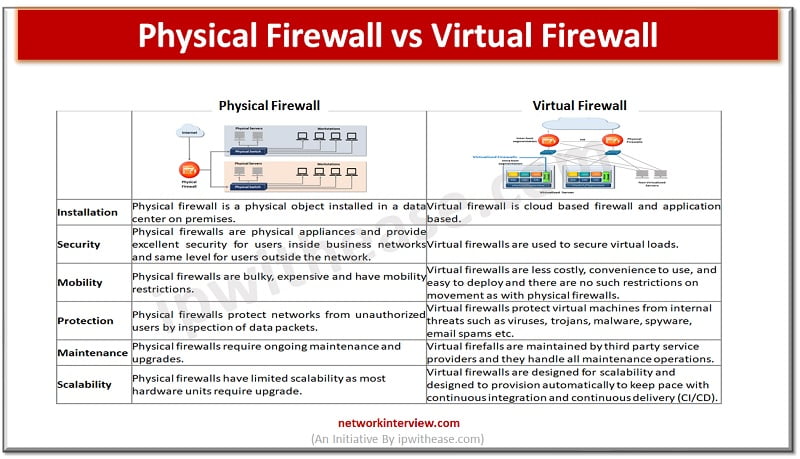
Firewalls are the first line of defense for an organization’s networks. Firewalls come in different categories – they can be a hardware appliance, software based or virtual. The increasing penetration of cloud computing infrastructures has given rise to virtual firewalls. …
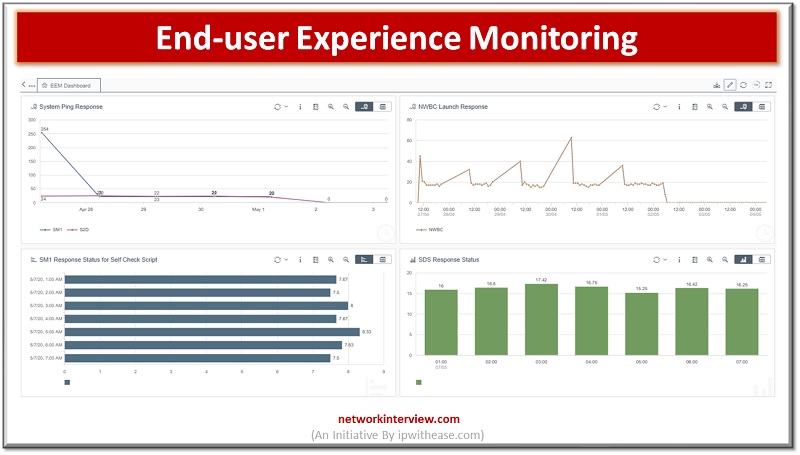
The Importance of End-User Experience Monitoring End-user experience monitoring is a critical aspect of ensuring a high-quality digital experience. The need for businesses to provide an optimal digital experience to their customers is at its peak, and digital experience monitoring …
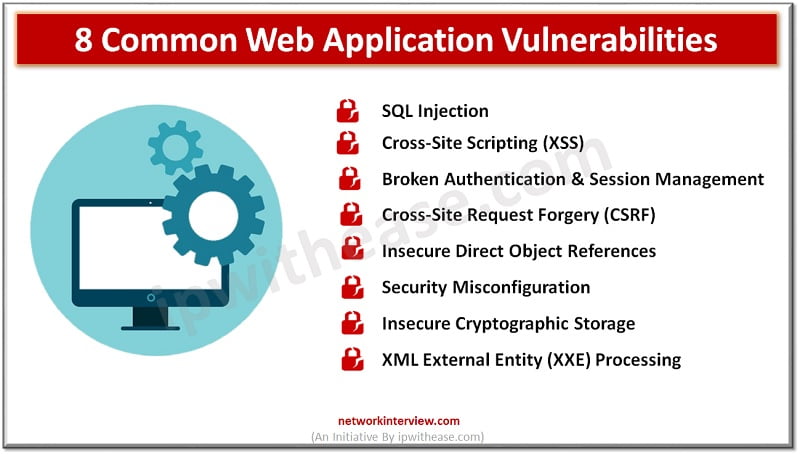
Introduction to Web Application Vulnerabilities Web application vulnerabilities are glitches or imperfections found in the system. These can lead to security risks, such as cyber-attacks or data breaches. Sadly, these risks occur more often than network or asset dangers. According …
Understanding each Encryption Technique When we dive in-depth to explore more about wireless key management and encryption technologies, then we would find that network protocols play an imperative part in it. As we are dealing with the technologies that are …
In today’s fast-paced and competitive business landscape, small businesses face numerous challenges that can hinder growth and productivity. Limited resources, time constraints, and the need to juggle multiple tasks often leave small business owners overwhelmed and struggling to keep up. …
One of the most popular programs for signing PDFs is Adobe Acrobat Reader DC, which allows you to electronically sign documents on your computer or mobile device. Here’s how to do it: Open the PDF you want to sign in …
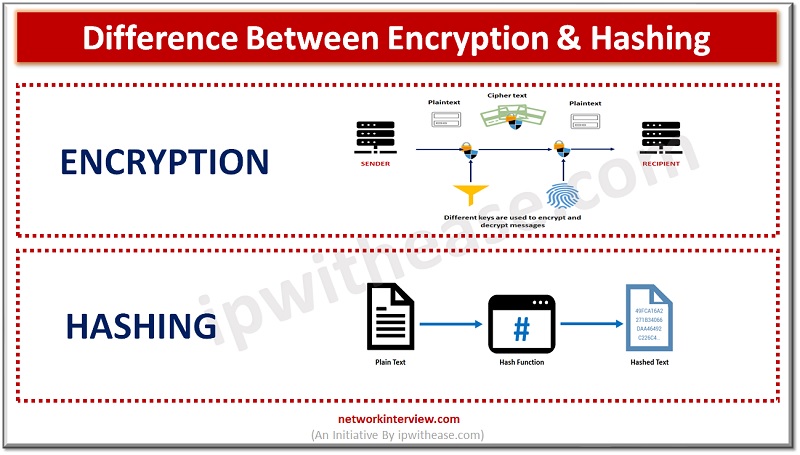
In the realm of data security, hashing and encryption are commonly employed to protect information from unauthorized access. While both methods have distinct processes and advantages, they are occasionally mistakenly used interchangeably. This blog will delve into the definitions of …
The digital marketplace is growing at an unprecedented rate, with e-commerce businesses serving as the cornerstone of this rapid expansion. As these businesses evolve and flourish, they face a pivotal challenge: securing their customers’ financial information. One of the most …
Discussing the implications of VPN providers logging user activity and the importance of privacy policy The usage of VPNs has become increasingly popular among internet users who place great importance on privacy policy and security. VPNs are known for their …
Each iPhone and iPad has a set storage capacity, but even the largest storage devices can eventually become filled with the content you acquire through music, apps, photos, and messages. Unfortunately, you cannot increase your device’s storage capacity, but there …
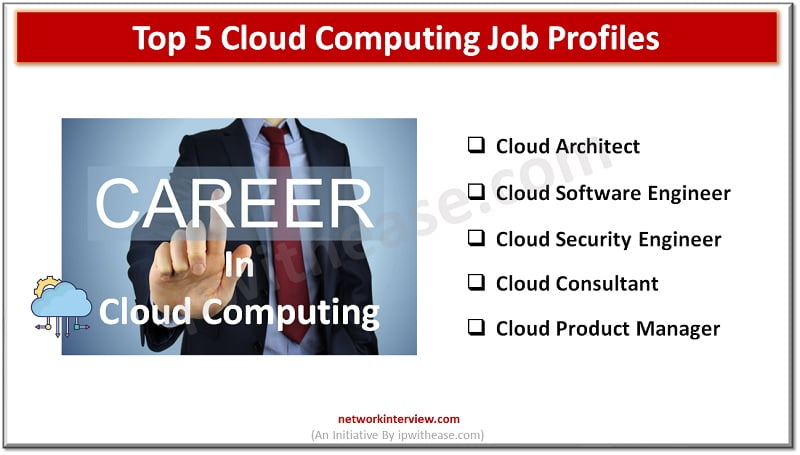
In today’s rapidly evolving digital landscape, the importance of cloud computing is inescapable. As a cornerstone of modern technology, cloud computing has transformed how businesses operate by offering flexible, cost-effective, and scalable solutions to data storage and management. But what …
What are infographics and how can they be useful for IT professionals? We’re explaining the answers along with tips on how to make infographics that resonate. Have you heard of infographics? You know about other formats that are great for …
In today’s digital age, cybersecurity is a critical concern for businesses of all sizes. With cyber threats becoming more sophisticated and prevalent, it is essential for employees to be well informed and proactive in protecting sensitive company and customer data. …
Every business is more than just a person or a team working on a task. If you’re a business owner or manager, you know how many aspects and issues a company has to deal with throughout the day. It’s incredibly …
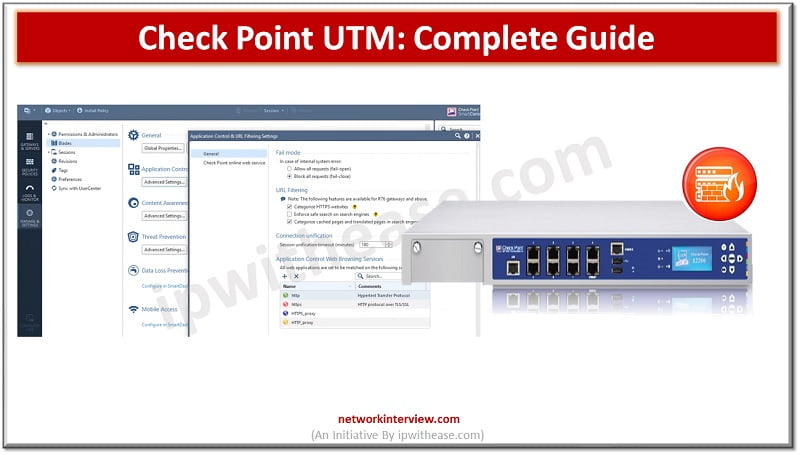
UTM (Unified Threat Management) solution deployed at the gateway level and scans all the malicious and suspicious traffic which passes through the network. UTM has multiple parameters such as URL Filtering Application Control Intrusion Prevention System Antivirus & Anti-Bot Data …