9 Major Types of Malware Payloads: How to Mitigate a Malware Attack?
In recent times, the worldwide cyber security scenario has witnessed a surge in potential risks. With the onset of the pandemic, cyber offenders exploited the vulnerability of poorly aligned networks when companies transitioned to remote working setups. The cyber attack rates have increased multifold. This necessitate the need of awareness to prevent and mitigate these attacks.
Malware is a type of software that is intentionally designed to harm a computer system, network, or mobile device. It is created and used by hackers to gain unauthorized access to sensitive information.
In this blog, we will under the different types of malware payloads and the ways to mitigate them.
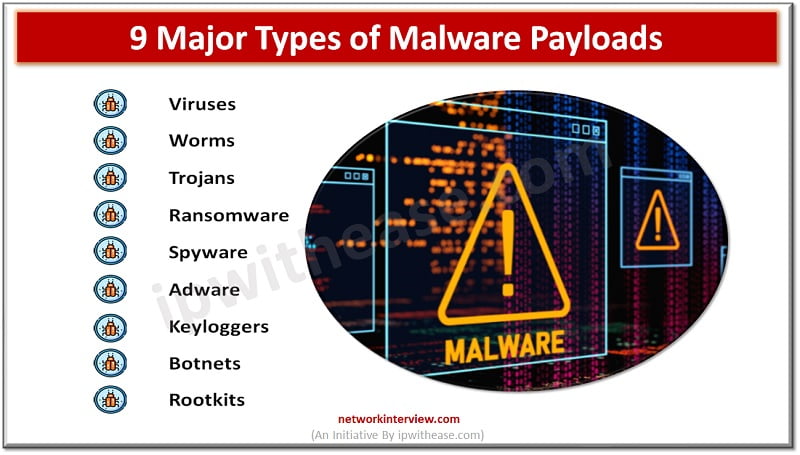
Types of Malware Payloads
Malware payloads refer to the malicious components or actions performed by malware once it infects a system. These payloads can vary depending on the objectives of the malware and the techniques used to achieve them. Identifying these kinds of malware payloads is the initial step in guarding against them.
Here are some common types of malware payloads:
- Viruses: Viruses are self-replicating malware that infects files or programs by attaching their malicious code to them. The payload of a virus can range from simply displaying an annoying message to causing data corruption or destruction.
- Worms: Worms are standalone malware programs that can spread across networks without requiring user interaction. Their payloads often involve exploiting network vulnerabilities to infect other systems, creating backdoors, or carrying out denial-of-service (DoS) attacks.
- Trojans: Trojans, or Trojan horses, disguise themselves as legitimate or desirable software to trick users into executing them. Once activated, Trojans can perform various payloads, such as stealing sensitive information, creating backdoors, or facilitating remote control by the attacker.
- Ransomware: Ransomware encrypts the victim’s files and demands a ransom payment in exchange for the decryption key. The payload of ransomware is typically focused on locking files and displaying ransom messages, often causing significant disruptions and financial losses.
- Spyware: Spyware is designed to secretly monitor and gather information about a user’s activities, often including keystrokes, browsing habits, and sensitive data. The payload of spyware involves transmitting the stolen information to the attacker or controlling it remotely.
- Adware: Adware displays unwanted advertisements on infected systems. While not always inherently malicious, some adware can be invasive and gather user information for targeted advertising purposes. The payload typically involves delivering and displaying advertisements.
- Keyloggers: Keyloggers record keystrokes made by a user, allowing attackers to capture sensitive information such as passwords, credit card numbers, or other confidential data. The payload of keyloggers is focused on capturing and transmitting this information to the attacker.
- Botnets: Botnets consist of compromised computers, or “bots,” which are controlled remotely by a command-and-control (C&C) server. The payload involves turning the infected systems into part of a network, allowing the attacker to perform coordinated actions, such as launching distributed denial-of-service (DDoS) attacks or distributing spam emails.
- Rootkits: Rootkits are designed to gain unauthorized access to a system and hide their presence. The payload of a rootkit involves concealing its files, processes, or network connections, making it difficult to detect or remove.
These are just a few examples of the diverse range of payloads that malware can have. As malware constantly evolves, new types of payloads and techniques emerge to exploit vulnerabilities and achieve the objectives of the attackers.
How to Mitigate a Malware Attack?
Mitigating a malware attack involves taking proactive measures to prevent infections and minimize the impact of malware if it does infiltrate a system. Here are some general steps to help mitigate a malware attack:
- Keep software up to date: Regularly update your operating system, software applications, and antivirus/anti-malware programs. Updates often include security patches that address known vulnerabilities.
- Use reputable security software: Install a reliable antivirus/anti-malware solution and keep it updated. This software can help detect and block malware before it infects your system.
- Exercise caution with email attachments and downloads: Be vigilant when opening email attachments or downloading files from the internet. Only open attachments or download files from trusted sources, and scan them with security software before opening.
- Enable a firewall: Use a firewall to monitor incoming and outgoing network traffic. This helps block unauthorized access and can prevent malware from communicating with its command-and-control server.
- Implement strong passwords and multi-factor authentication (MFA): Use complex passwords that are difficult to guess and consider enabling MFA whenever possible. This provides an additional layer of security by requiring a second form of authentication.
- Regularly back up important data: Perform regular backups of your important files and data. Store backups on separate devices or off-site to ensure they are not affected by a malware attack. This helps minimize the impact of data loss in case of an infection.
- Practice safe browsing habits: Be cautious when visiting websites, especially those of unknown or suspicious origin. Avoid clicking on suspicious links, pop-ups, or advertisements, as they may lead to malware-infected websites.
- Educate and train users: Promote cybersecurity awareness among employees and educate them about safe online practices. Teach them how to identify phishing emails, suspicious websites, and potentially malicious files.
- Enable system and application sandboxing: Sandboxing isolates programs and processes from the rest of the system, limiting the potential damage caused by malware. Utilize virtualized environments or sandboxing features provided by your operating system or security software.
- Monitor system activity: Regularly monitor your systems for any unusual or suspicious behavior. This can involve analyzing network traffic, reviewing system logs, and using intrusion detection systems (IDS) or security information and event management (SIEM) tools.
- Respond quickly to infections: If you suspect a malware infection, isolate the affected system from the network to prevent further spread. Scan the system using updated security software and follow appropriate incident response procedures.
Remember that no security measure is foolproof, but implementing these practices can significantly reduce the risk of malware infections and mitigate the impact of an attack.
Continue Reading
What is Multi-Factor Authentication (MFA) & How Does it Work?
WEP vs TKIP vs CCMP: Understanding what each encryption technique offers
Tag:Security



