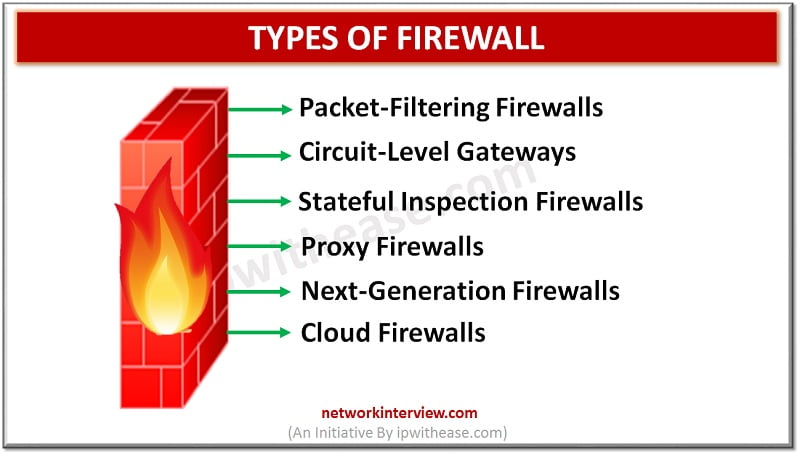
Introduction to Firewall In todays digital scenario, where businesses demand agility and information are hosted on cloud infrastructure security of data is one of the primary concerns of business and protection of data from unwanted sources is the prime objective. …
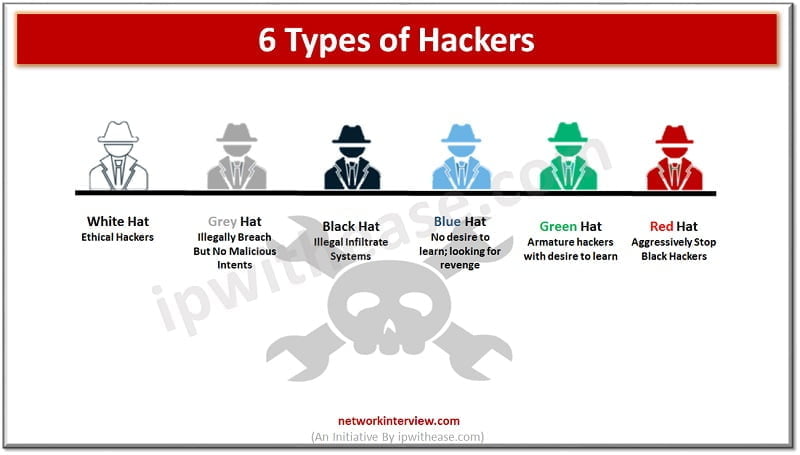
You must have heard the word ‘hacker’ multiple times in cybersecurity. The organizations have trained security staff to take care of cybersecurity threats. Hacking is generally referred to as someone gaining access to your network and systems by unauthorized means. …
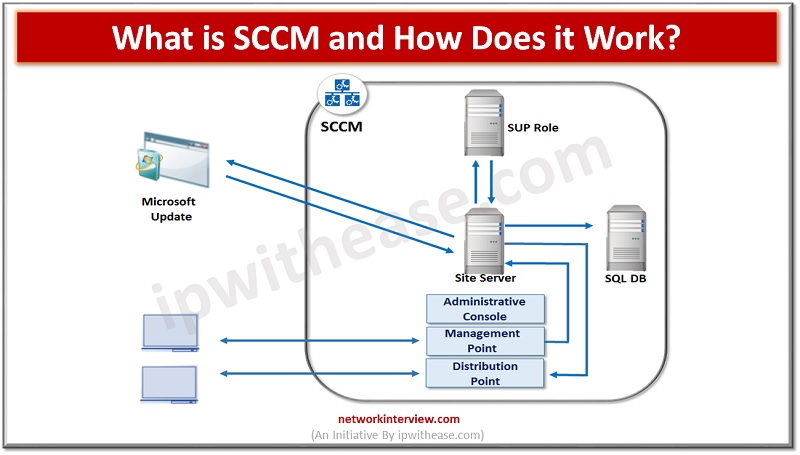
Configuration Manager, commonly known as SCCM, is a powerful and versatile tool created by Microsoft. It provides IT professionals with an integrated platform to manage and deploy software, hardware, and other resources across their networks. In this blog, we’ll take …
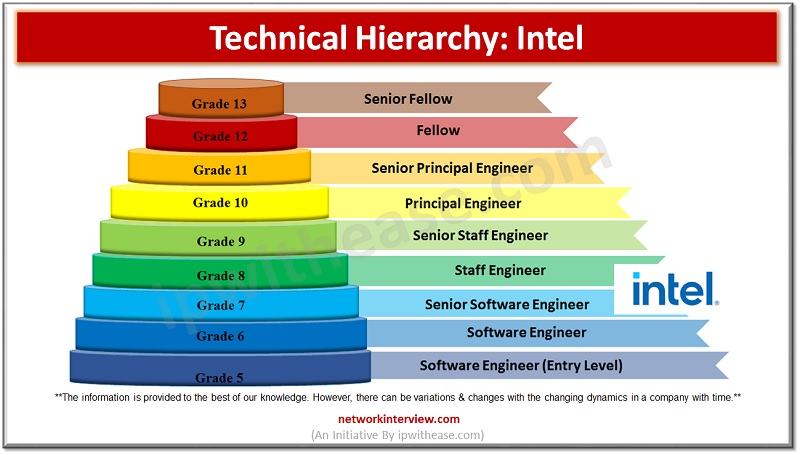
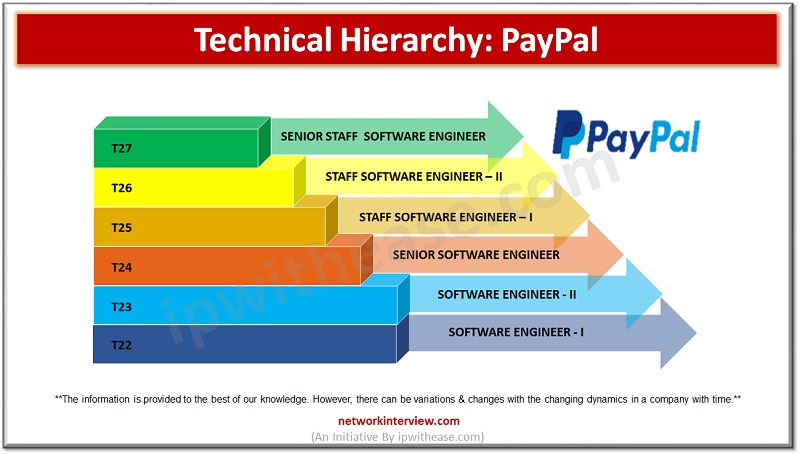
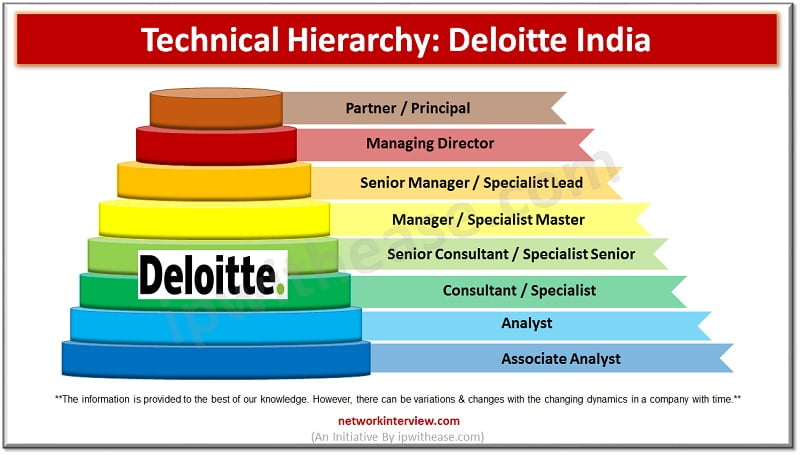
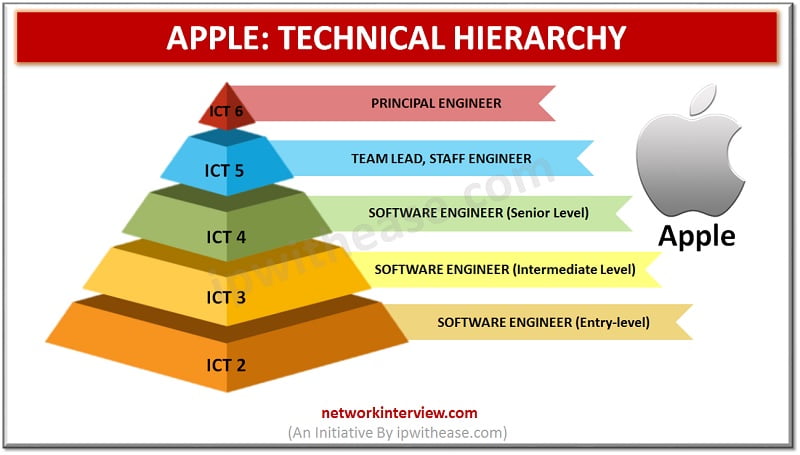
Getting a job in an MNC is always the dream of aspiring new Engineers and developers. But oftentimes, the hierarchy and job positions mentioned in the Interview make them confused and they land on a position lower or higher to …
It is a dream for many graduating Software engineers to land a job at PayPal. The main reason is its global availability and promising salary and other benefits. Are you one of them? Then you should consider certain things first. …
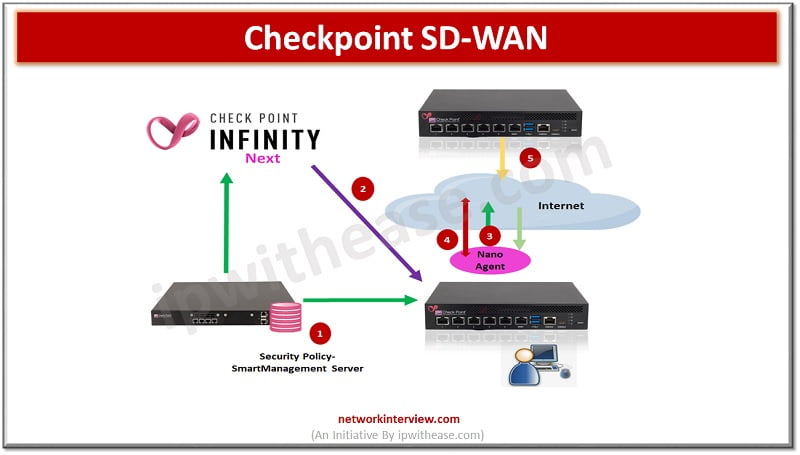
Note: This document is for those seekers who have prior knowledge of SD WAN and want to enhance SD WAN concept in Checkpoint perspective. This blog covers below topics of Checkpoint SD WAN: Quantum CheckpointSD-WAN concept Architecture Application basic traffic …
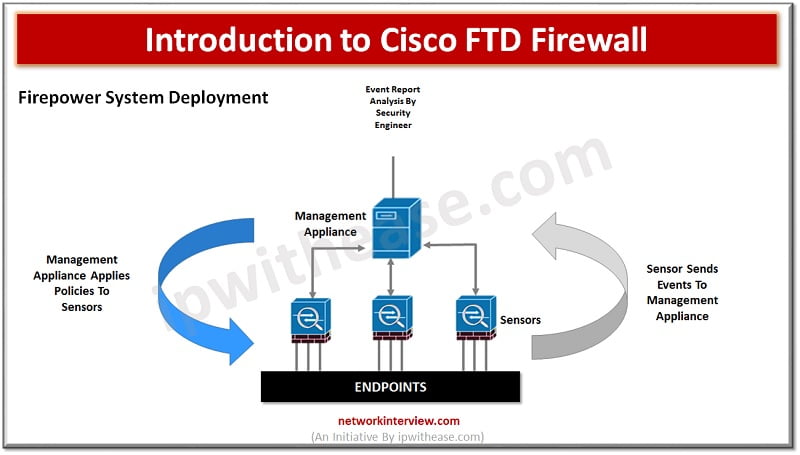
figure:1 As more and more systems are Internet facing due to high penetration of cloud and associates’ applications and services, the need for a very strong security system at perimeter or gateway to enterprises is becoming more and more crucial. …
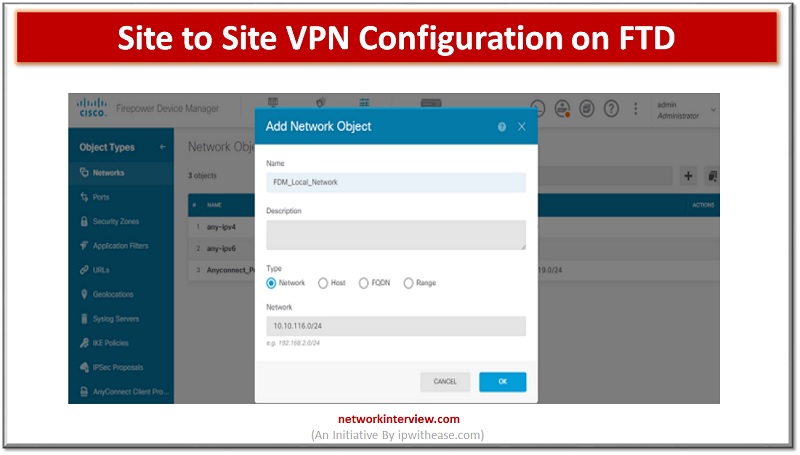
VPNs allow access to restricted sites with secure connection. In FirePower devices we can configure site to site VPN on FTD devices. The site to site VPN is configured for FTD devices using the FirePower Defence management console. In today’s …
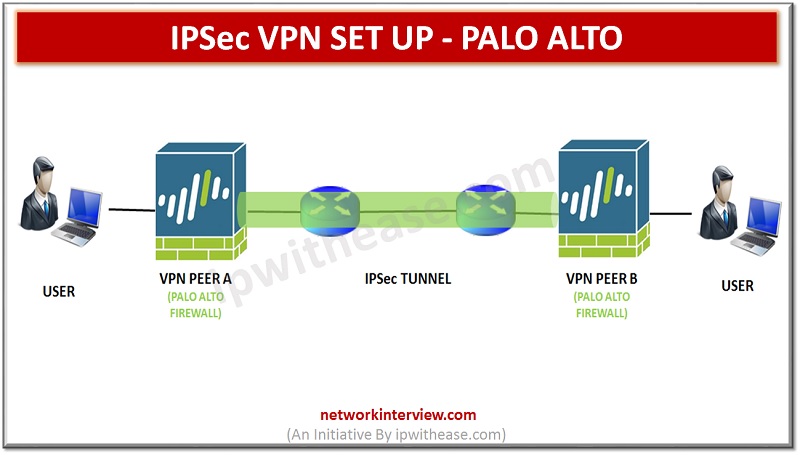
Site-to-Site VPN Overview A VPN connection that allows you to connect two Local Area Networks (LANs) securely is called a site-to-site VPN. Route based VPN can be configuring to connect Palo Alto Networks firewalls located at two sites or to …
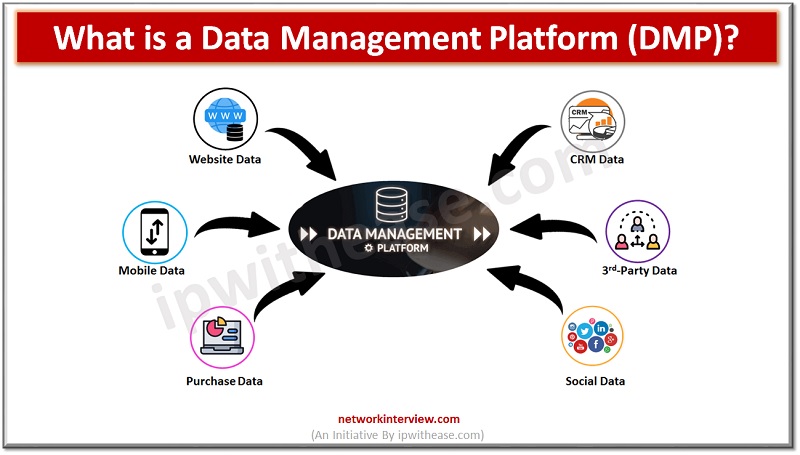
In today’s digital age, data is everything. From businesses to individuals, having access to the right data can make all the difference in making decisions and optimizing processes. Data Management Platforms (DMPs) are powerful systems that enable organizations to manage, …
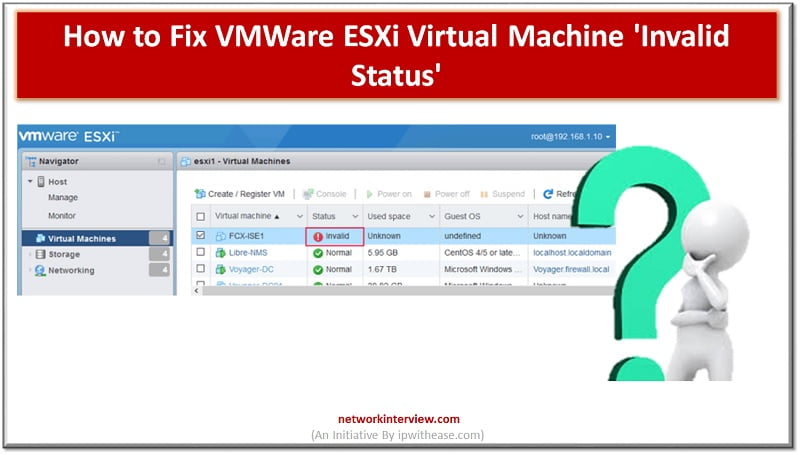
Troubleshooting VMWare ESXi Virtual Machine ‘Invalid Status’ Let’s troubleshoot VM Invalid status You can see multiple “invalid” VM machines in the image below. Here status is showing invalid. Reason of Invalid VM Machine status could be related to the storage …
Overview In our previous article, we studied IPSec VPN Set Up. In this article we will run through CLI commands and GUI steps to configure an IPSec VPN, including the tunnel and route configuration on a Palo Alto Networks firewall. …
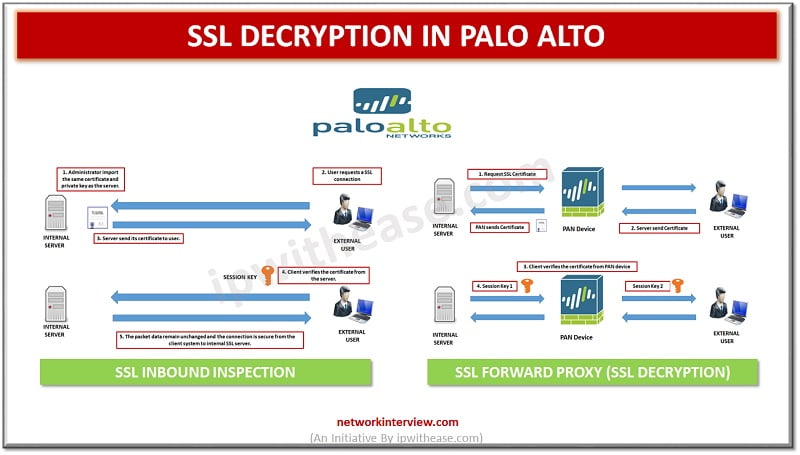
Before digging deep into Palo alto SSL Decryption, let’s first understand what is Decryption? What is Decryption? Palo Alto firewalls can be decrypt and inspect traffic to gain visibility of threats and to control protocols, certificate verification and failure handling. …
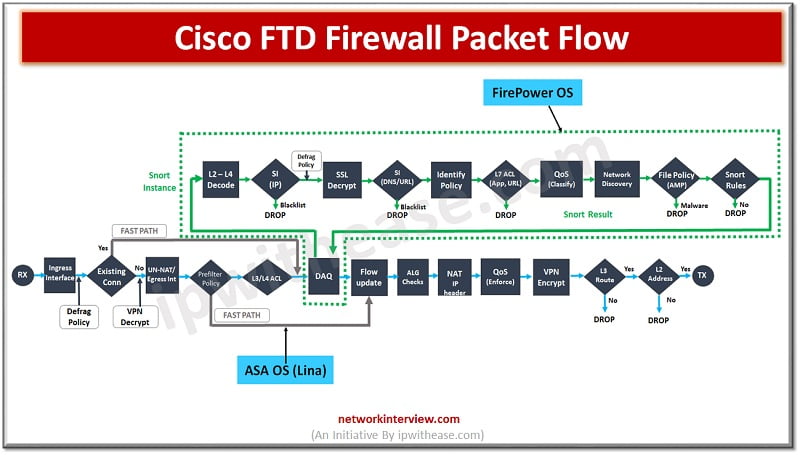
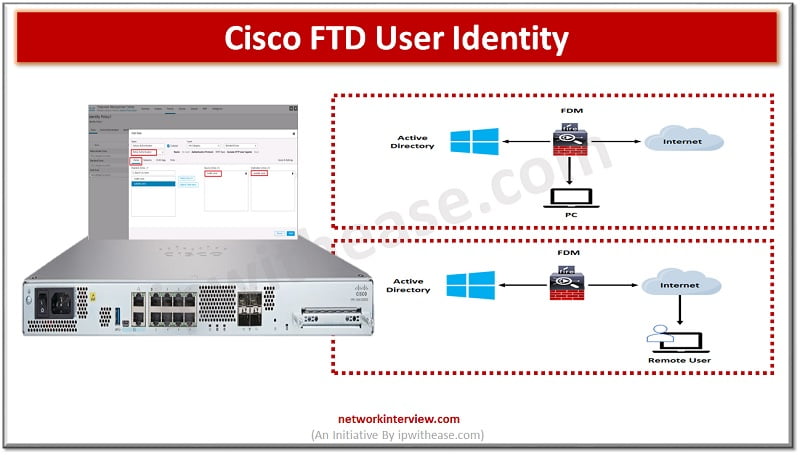
User identity information helps to identify the source of policy breaches, attacks or network vulnerabilities and trace them to specific users. Majority of traffic inspection products support filtering based on IP address. However, Cisco FTD identity policy feature gives the …
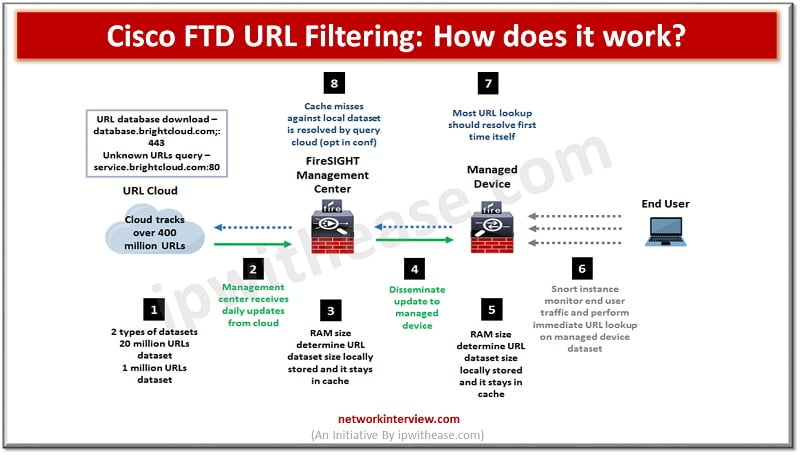
Pic: Showing How Cisco FTD URL Filtering works URL filtering or content filtering is one of the key features of firewalls. It helps to prevent access to harmful and malicious content which could cause data loss, system crash, virus or …
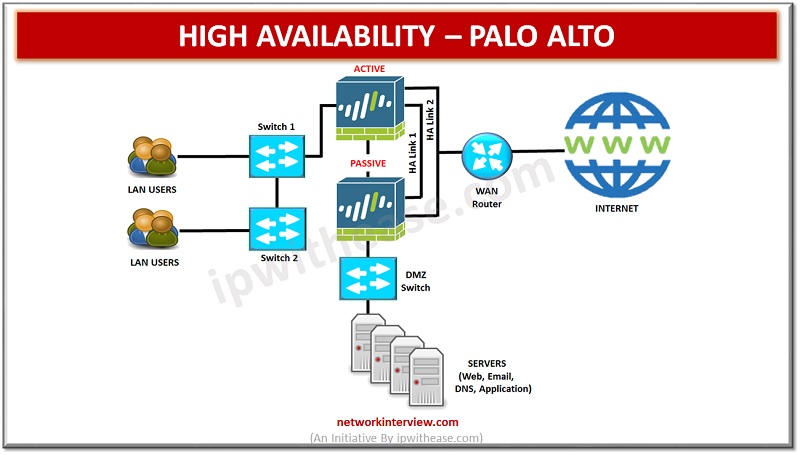
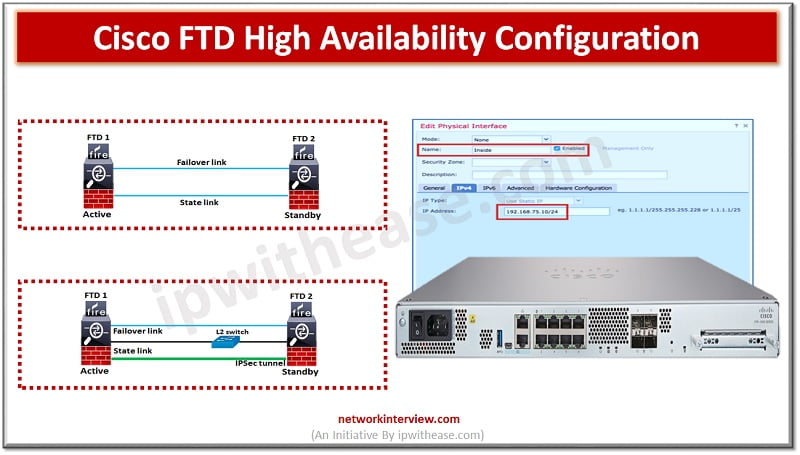
High availability (HA) refers to a system or component that is operational without interruption for long periods of time. High availability (HA) is measured as a percentage, with a 100% percent system indicating a service that experiences zero downtime. High …
To ensure uptime and continuous availability in the event of disaster is a required key feature for any production environments be it servers, networks and other computing equipment. All Cisco devices majority support high availability (HA) also known as failover. …
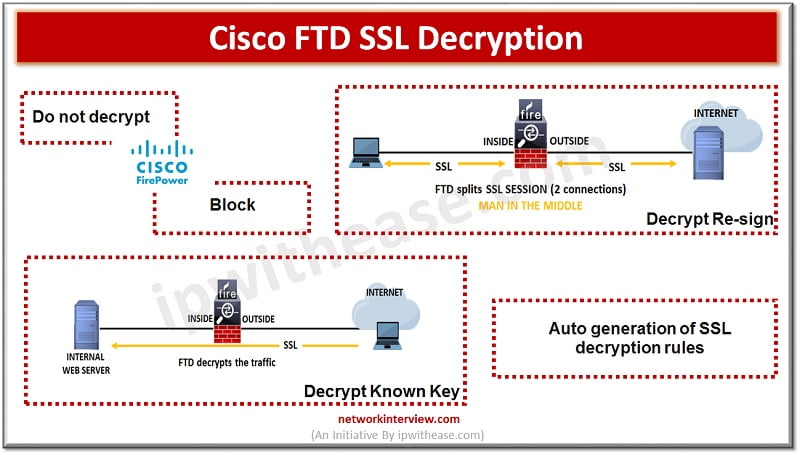
Some protocols like HTTPS use Secure socket layer (SSL), transport layer protocol (TLS) to encrypt traffic for secure transmissions. As the system cant inspect encrypted connections we first must decrypt to apply access roles which consider higher layer traffic characteristics …
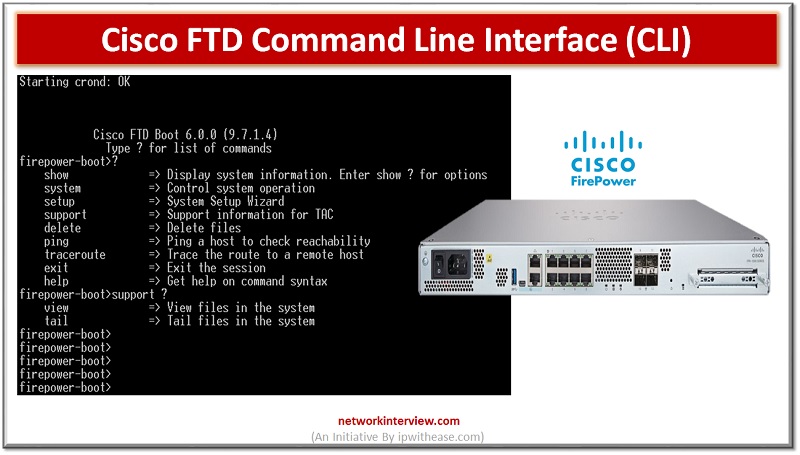
Majority of Cisco devices provide command line interface (CLI) as we call it to configure, manage and troubleshoot devices. Use of CLI allows users to execute Cisco IOS commands directly and simply as well as via remote access. In today’s …
In the evaluation of next generation firewalls (NGFW), the next leap made by Cisco FTD is (Unified Firepower threat defence) software which includes not just NGFW but also Next generation Intrusion prevention systems (NGIP), Advanced Malware protection (AMP) and many …
With the increasing popularity of mobile devices, businesses have been looking for ways to engage their customers more effectively. One of the solutions they have come up with is progressive web apps (PWAs). In this post, we will discuss what …
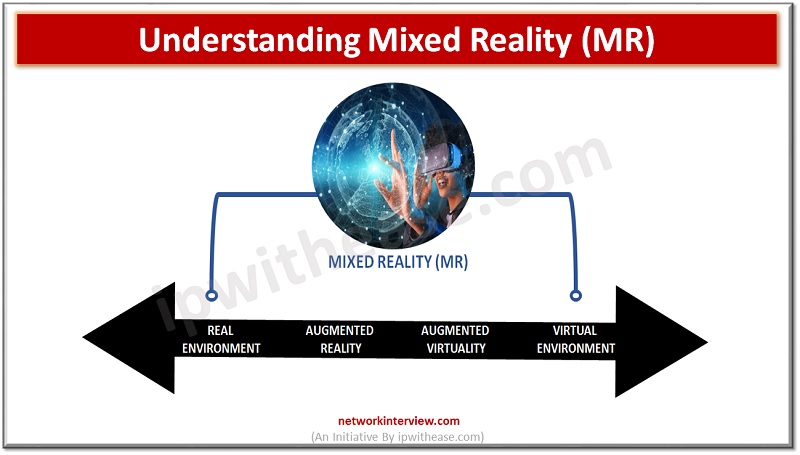
Mixed reality (MR) is a technology that has been gaining traction in recent years and is quickly becoming a powerful tool in various industries. In this blog article, we’ll take an in-depth look at what MR is, the different types …
Are you wondering what all the buzz around Virtual Reality (VR) is about? VR is rapidly becoming a major part of our lives, from gaming to entertainment to education. In this article, we will explore the basics of virtual reality, …
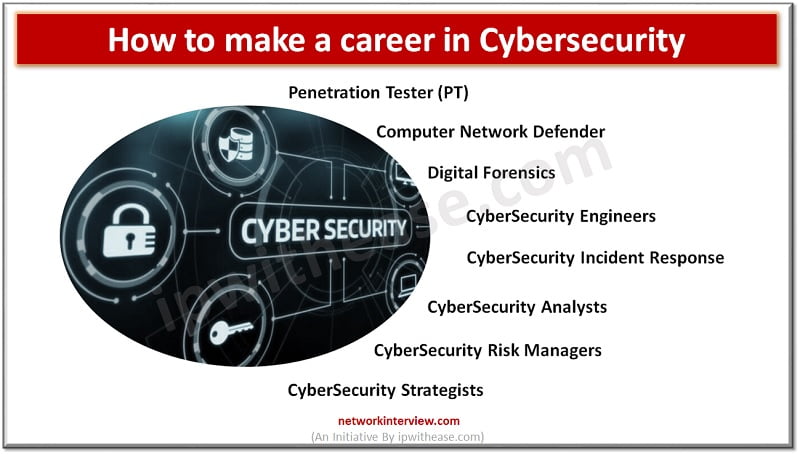
Career in Cybersecurity In this digital world, data is everywhere. This ensures that there are ample opportunities for people who have a passion for ethical hacking, known as “ethical hackers” to find jobs with companies that need their services. A …
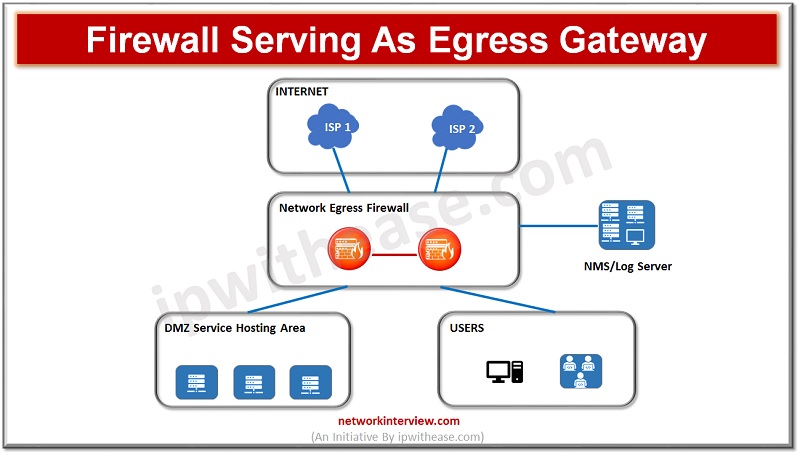
(Diagram depicting firewall acting as Egress Gateway) As enterprises are moving onto cloud their critical business applications, infrastructure services and use of hybrid clouds have evolved, secure networking is the demand of time along with performance and scalability of networks …
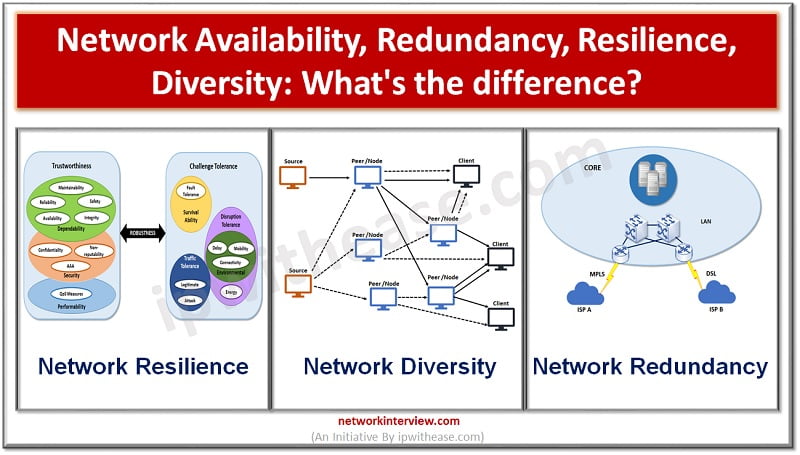
As critical organization infrastructures are moving onto cloud and relying more on Internet networking services it is essential for networks to be resilient having ability to provide and maintain an acceptable level of service in the event of faults and …
Today, engineering graduates dream of getting a job at a leading Software Development or Information Technology company. But software engineers are not only needed in technical companies but there are also good career opportunities in other firms. One of them …
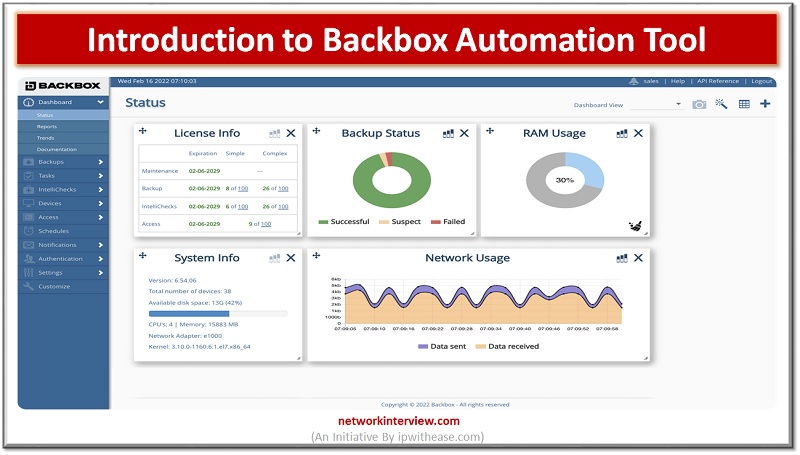
Are you looking to boost your productivity and efficiency as an IT administrator? If so, you’ll love the BackBox Automation Tool. This tool will help streamline your day-to-day operations, increase visibility into your network and accelerate troubleshooting. It’s the perfect …
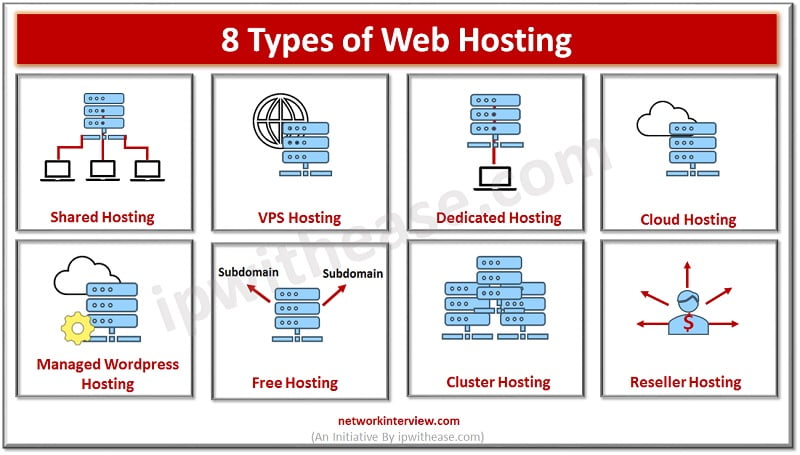
What is Web Hosting? Web hosting services let organizations and persons publish on the Internet or Internet page and plays a critical role in online presence. These websites are stored on systems hosted over the web or Internet. There are …
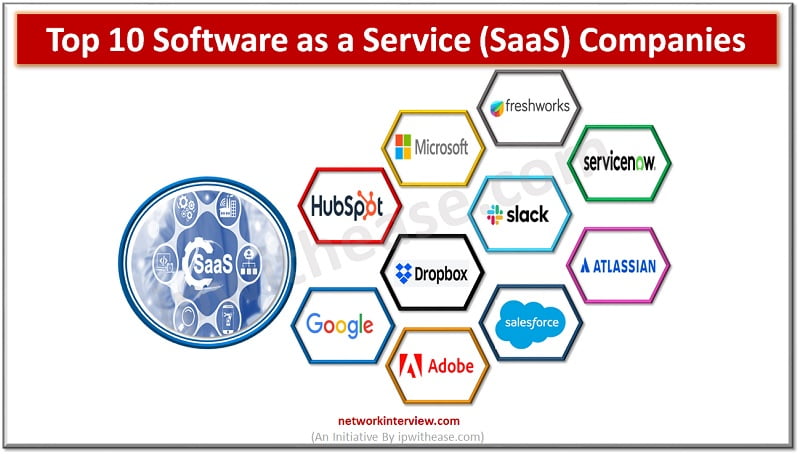
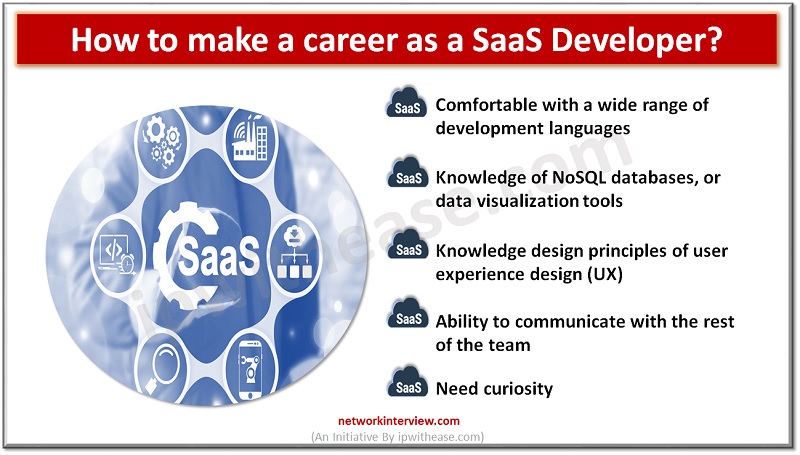
Software as a Service (SaaS) is an umbrella term for cloud-based services delivered to customers over the internet. The software operates on a subscription model, helping businesses reduce capital expenditure and operational expenses by shifting from upfront payments for software …
Software as a service (SaaS) is a type of software deployment model that delivers software services to users over the internet. The SaaS model enables third-party vendors to develop and host software applications so they can be accessed by consumers …
Search engine optimization is a field that’s growing more important every day. With the prevalence of search engines like Google, Bing and Yahoo rising, SEO has become an essential practice for any website hoping to attract visitors. Unfortunately, there are …
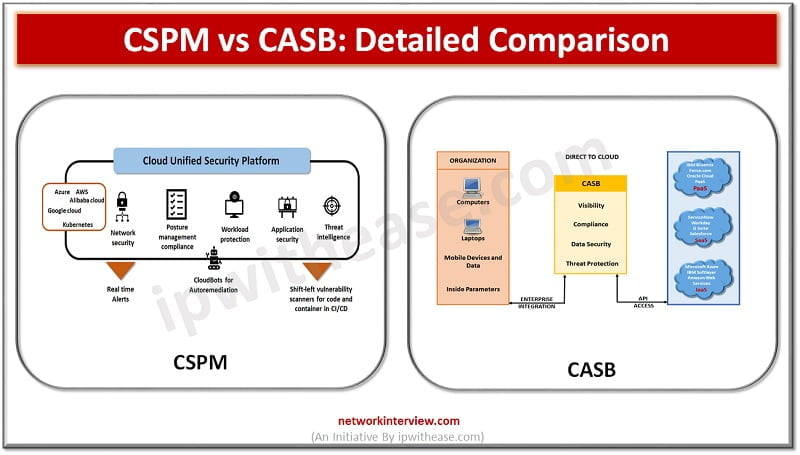
Enterprises are moving their workloads on cloud infrastructure. Gartner forecasts that globally public cloud spending will increase by 18.4% in 2021 to a total of $304.9 billion. As organizations shift IT spend more and more on cloud services, they are …
A common question arises in the mind of IT focals related to Cloud access security broker (CASB) service products such as we already have a web proxy firewall then how is this different? Is CASB a replacement for web proxy/ …
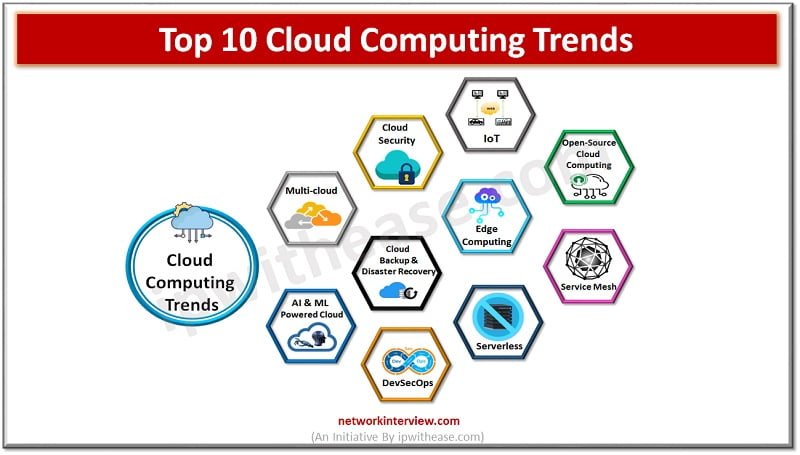
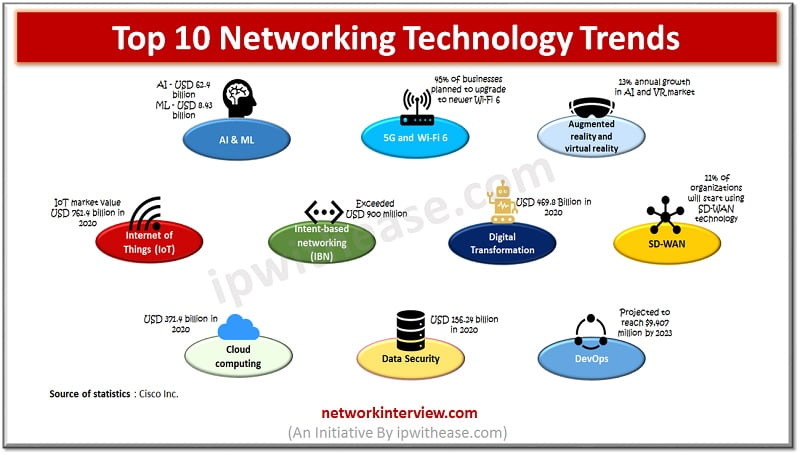
Ever-Emerging New Technologies New technology trends arise every day, but not all of them remain relevant. The same goes for the cloud computing industry. There are some technologies that have solid potential while others will disappear sooner than later. Today, …
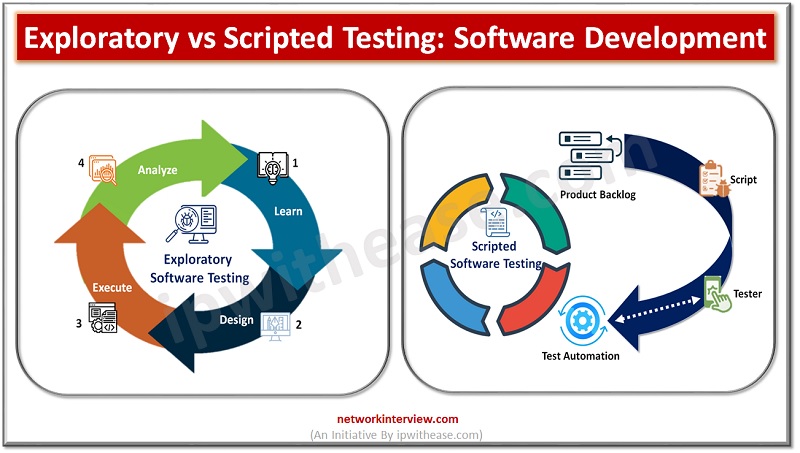
Software testing is a critical component of the software development process. When it comes to software testing, there are two main types: exploratory and scripted testing. Both testing methods have their merits and can be used in different scenarios depending …
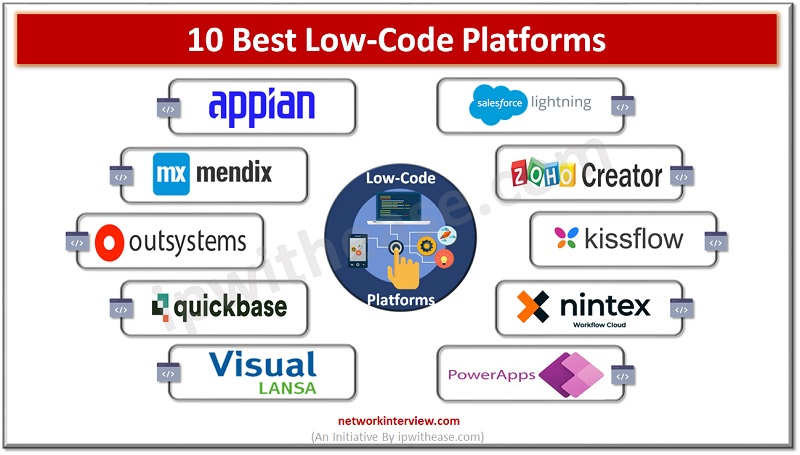
Introduction to Low-code Low-code software is great for users who want to perform complicated tasks quickly and efficiently. In this blog post, you will learn about ten best low-code platforms that you can use for your next project. These solutions …
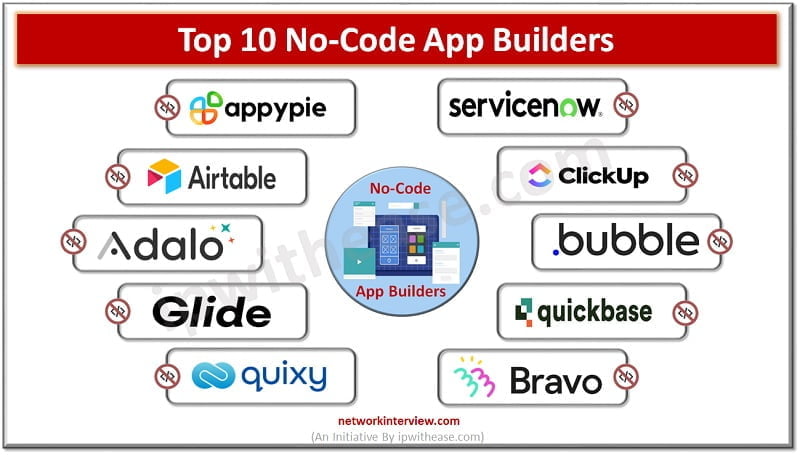
No-code app builders are a great option for teams that want to rapidly prototype or build software apps without needing to learn code first. They’re also an excellent choice for project teams who need to build and launch new apps …
Low-code vs No-code No-code and low-code software are both ways of building apps with limited coding experience. But they each have their own advantages and disadvantages. Choosing the right one for your team and project can help you create an …
In today’s digital world, businesses need software applications to keep pace with their changing needs and requirements. Businesses now look for more efficient ways to build and deploy these applications, without compromising on the quality or functionality. To meet this …
No-code is an emerging trend that allows non-technical users to build custom applications without writing code. In other words, no code means no programming skills are required. Instead, a no-code platform uses natural user interface (NUI) tools to create apps …
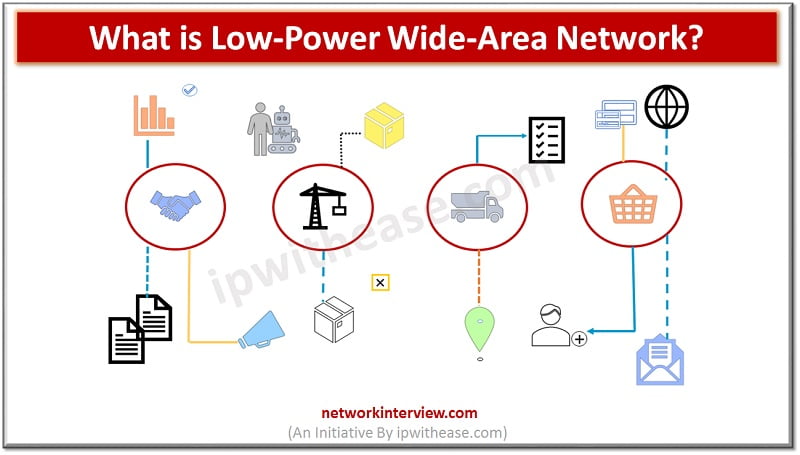
Low power wide area network (LPWAN) technologies offer a cost and power efficient wireless solution options for leveraging existing networks, global reach and strong built in security. They empowered and strengthened business case for IoT solutions as they help network …
Apple is considered to be an important tech player in the world. And getting a post in Apple Inc. is a dream come true for many graduates. But you can’t select your future career based on the reputation of the …
Introduction to Networking technology Networking technology have evolved significantly over the years as demands on Ethernet and Wi FI have tremendous increased. Apart from supporting a range of devices Local area networks require to manage traffic getting generated from many other …
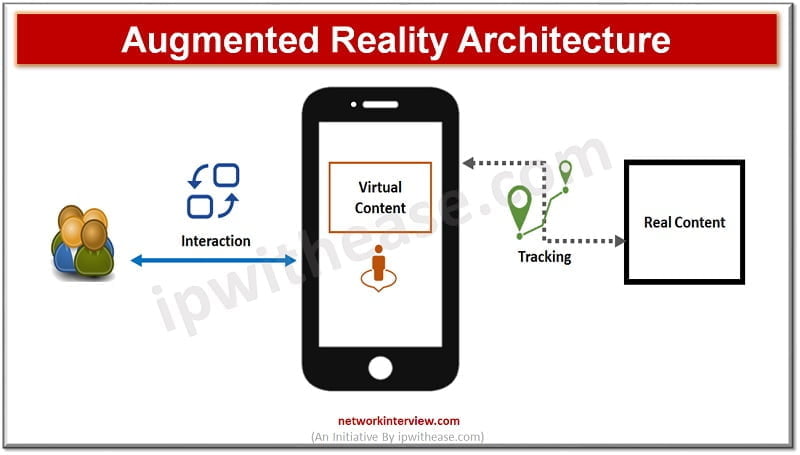
Just in time access to information, anywhere, everywhere is the focus of businesses. Enhancing customer experience by increased engagement and interaction to provide richer user experience, increasing the perceived value of brands and products with access to detailed analytics is …