The majority of enterprises large, medium and small are moving to the cloud ecosystem to run their IT operations. Cloud service providers require a multi-tenancy strategy and products to support multi-tenant scenarios. Networking is one of the most crucial elements …
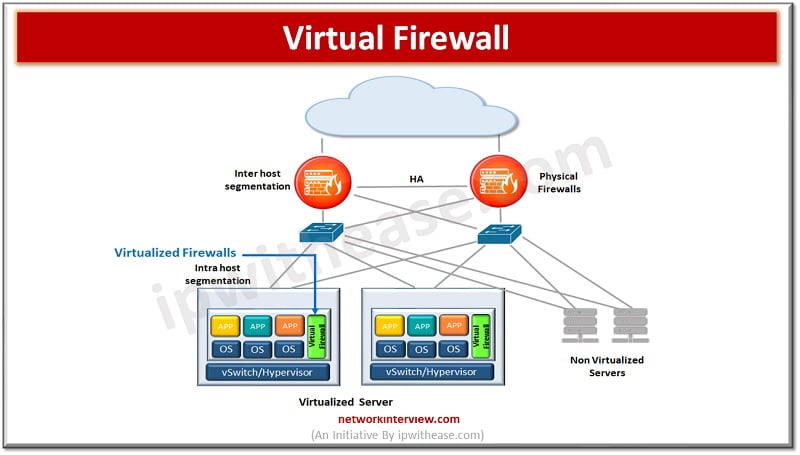
Firewalls have evolved a lot since their inception. The gatekeeper or epitome of perimeter security used to enhance network security. Initial days firewalls were simple packet filters which examined packets of information passing through them and blocked which did not …
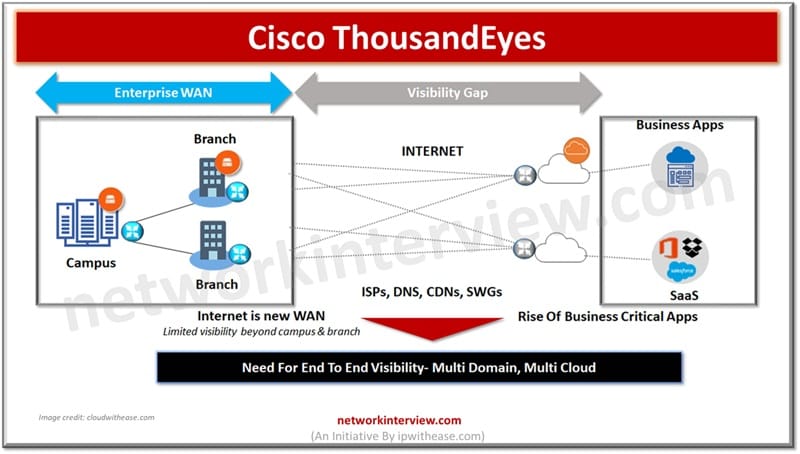
Cisco ThousandEyes is a comprehensive platform for measuring, monitoring, and troubleshooting network performance. It is a cloud-hosted platform that helps organizations ensure reliable and secure user experience and network performance across the globe. ThousandEyes provides insights into the performance and …
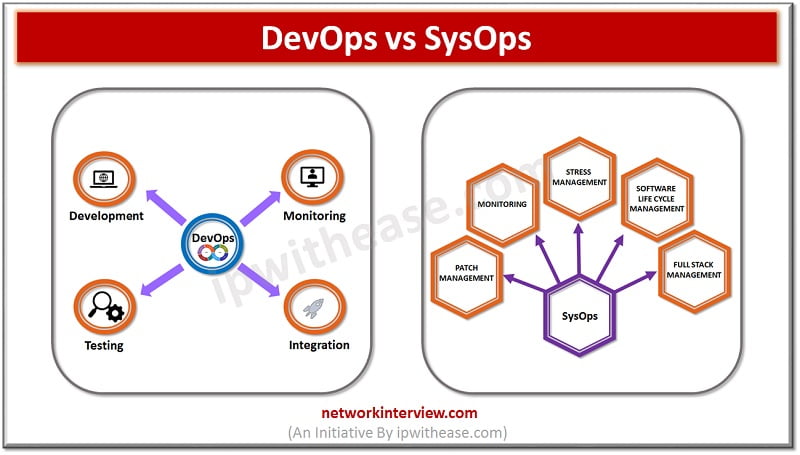
Introduction to DevOps & SysOps Technology advancements are crucial to the dynamic IT landscape in today’s times. Cloud computing has been crucial which presents excellent opportunities to business for the future. SysOps and DevOps are commonly used terminologies in cloud …
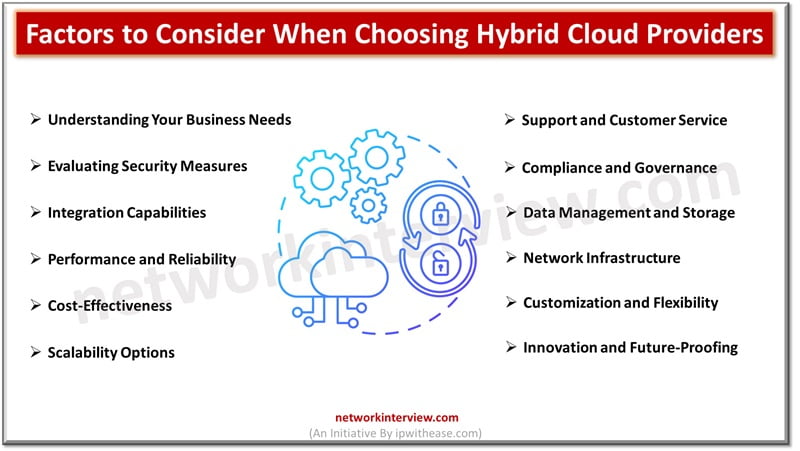
Are you overwhelmed by the myriad of hybrid cloud computing providers available? Choosing the right one can significantly affect your business’s scalability and efficiency. This blog will guide you through key factors to consider when selecting a hybrid cloud provider. …
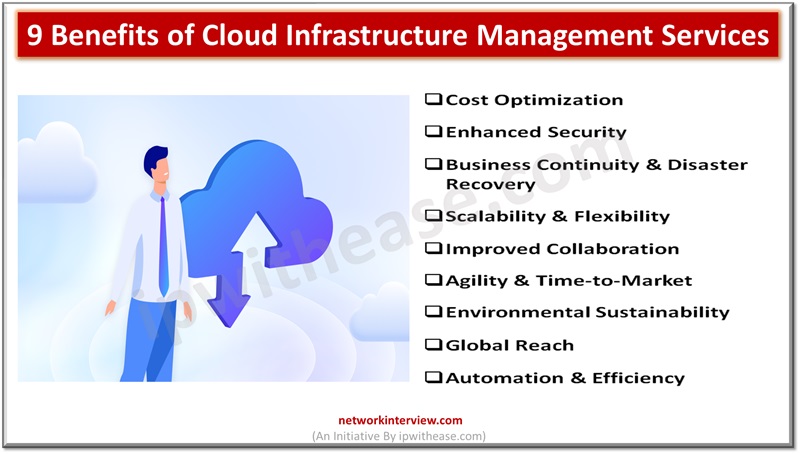
Cloud infrastructure has become an omnipresent force, exerting a profound impact on individuals worldwide, both directly and indirectly. Directly, individuals interact with cloud services in their daily lives, from storing personal files on platforms like Google Drive to streaming entertainment …
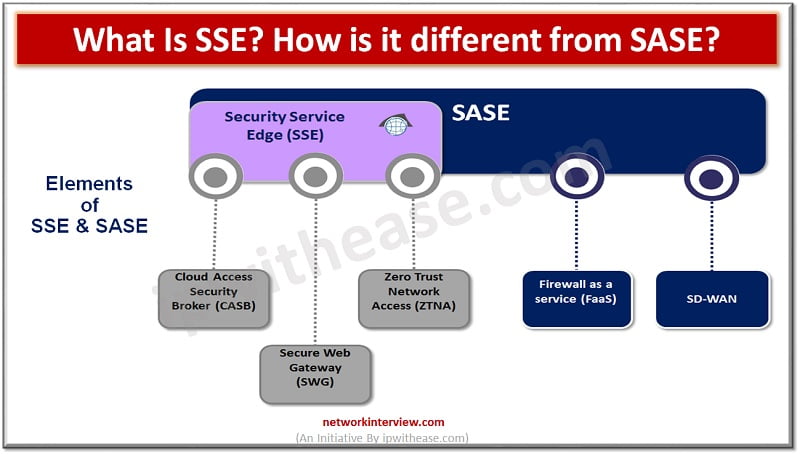
Introduction to SSE & SASE Security and network architecture have taken a front seat since cloud adoption is all time high and constantly growing. The demand for remote workforce is increasing and per Gartner research demand for remote working is …
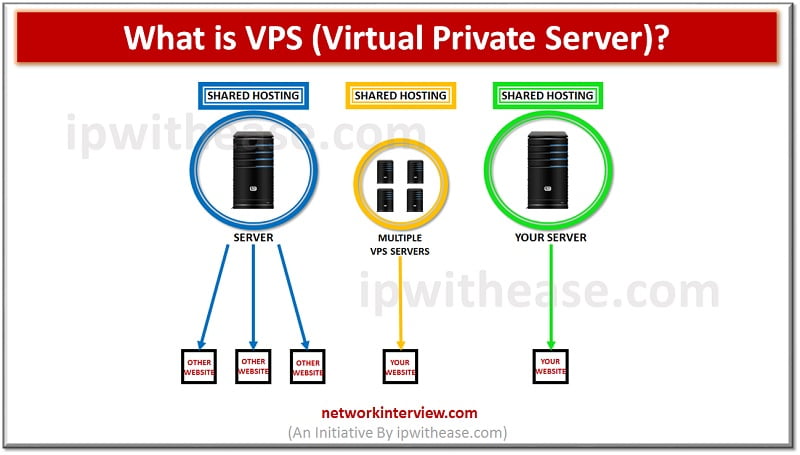
Introduction to VPS (Virtual Private Server) In the IT community, we define with the term VPS (Virtual Private Server), any virtual machine that is sold as a service by an Internet Hosting Service. In normal conditions, a virtual private server …
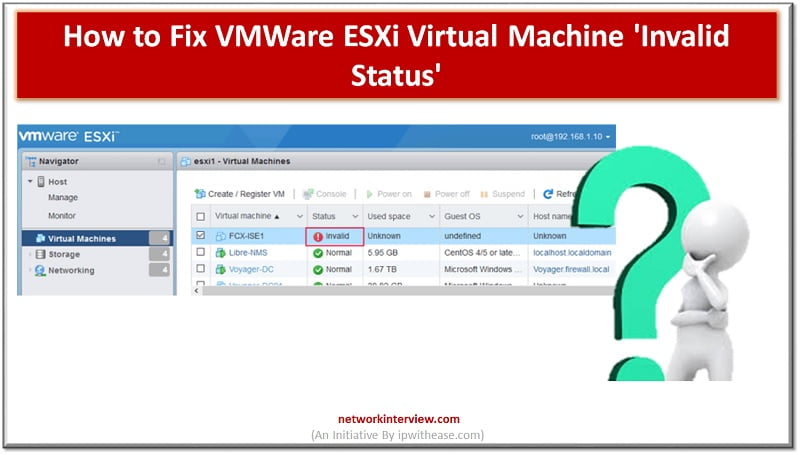
Troubleshooting VMWare ESXi Virtual Machine ‘Invalid Status’ Let’s troubleshoot VM Invalid status You can see multiple “invalid” VM machines in the image below. Here status is showing invalid. Reason of Invalid VM Machine status could be related to the storage …
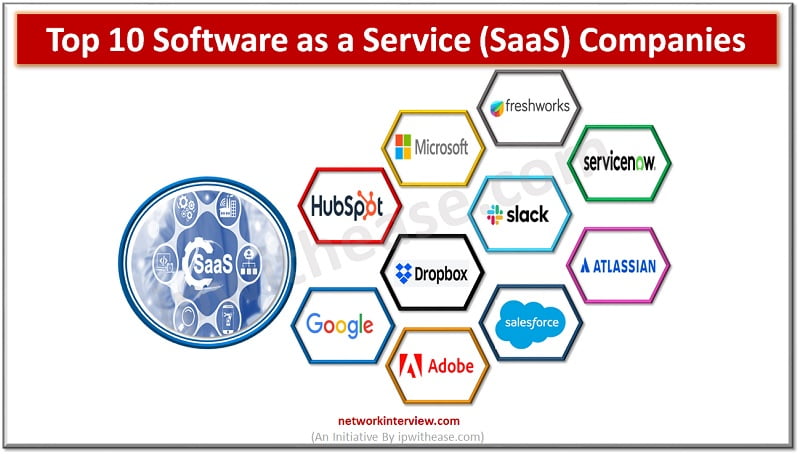
Software as a Service (SaaS) is an umbrella term for cloud-based services delivered to customers over the internet. The software operates on a subscription model, helping businesses reduce capital expenditure and operational expenses by shifting from upfront payments for software …
A common question arises in the mind of IT focals related to Cloud access security broker (CASB) service products such as we already have a web proxy firewall then how is this different? Is CASB a replacement for web proxy/ …
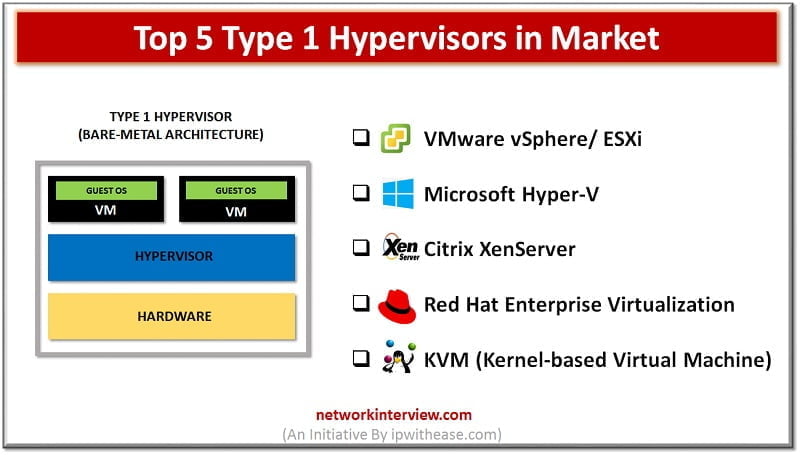
Types of Hypervisors Virtual Machine Monitor or VMM also called as Hypervisor is a technology that separates software (computer operating system) from hardware. With a hypervisor, a host computer can support and accommodate many other virtual machines by sharing its …
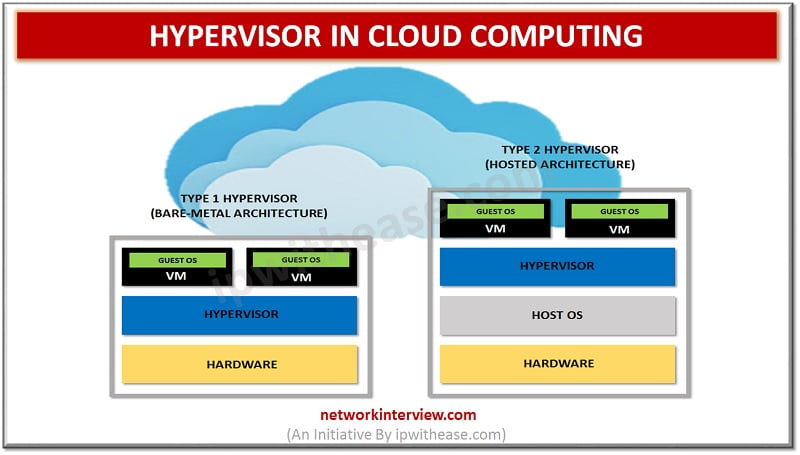
Hypervisor in Cloud Computing: For long, Applications were assigned dedicated physical servers and resources like CPU, memory and storage. Growth and demand in the ever changing IT environment stipulated for a cost effective and energy saving solution. Virtualization technology gained …
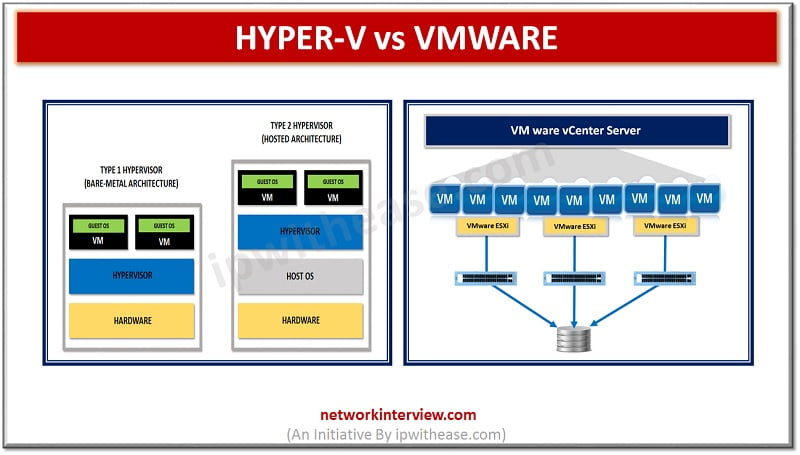
Hyper V vs VMware In computing, virtualization refers to the act of engendering a virtual version of one thing, as well as virtual constituent platforms, storage contrivances, and electronic network resources. On a very broad level, there are 3 styles …
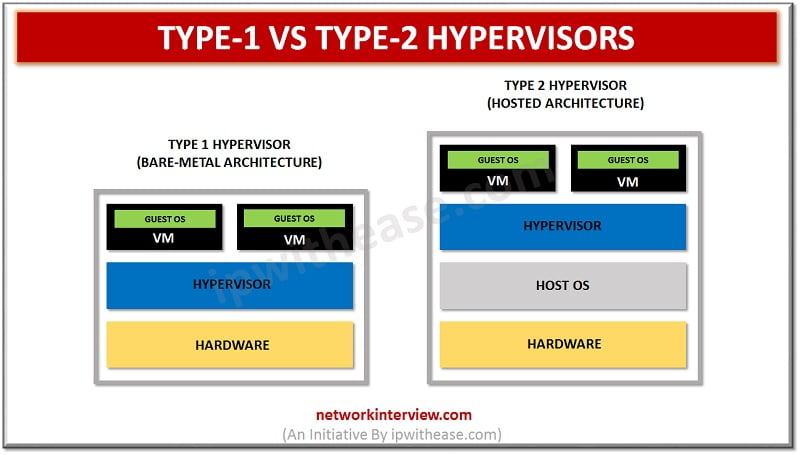
Type-1 vs Type-2 Hypervisors Server virtualization is perhaps the sultriest point in the IT world today. It has been around for a long time, and its ubiquity continues developing, particularly in big business environments. What makes virtualization conceivable in hypervisors? …
XEN vs KVM Talking about the virtualization concept, hypervisors technology is quite a well-known concept. A hypervisor is used by a person who would wish to merge the server space or run a number of other independent machines with the …
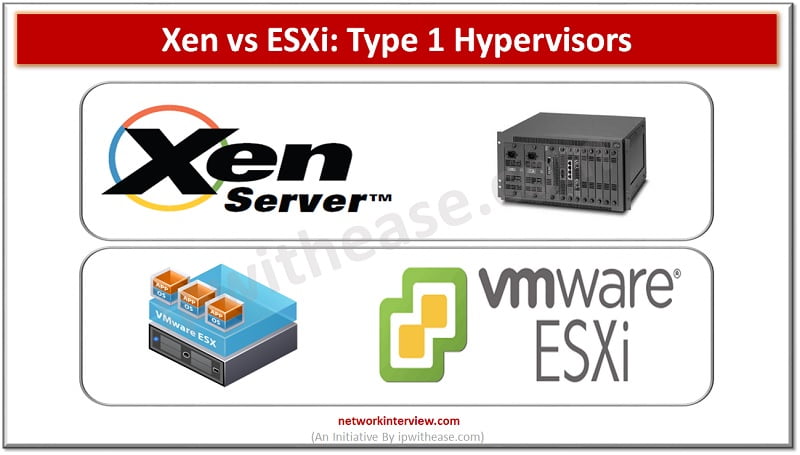
Xen and ESXi are unique form of type-1 hypervisors that are specially built for deploying and serving the virtual computers. There can be various kinds of similarities between the two, but here our aim is to bifurcate both of them …
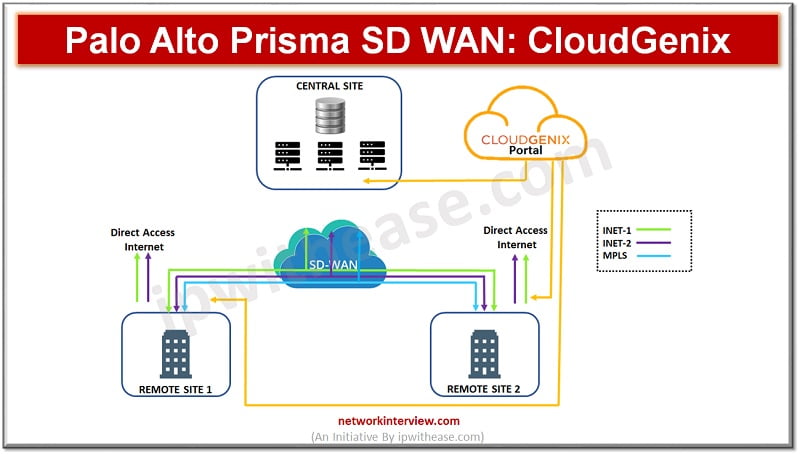
Introduction to Palo Alto Prisma SD WAN More and more organizations are moving towards hosting and running business applications in public cloud such as Microsoft Azure, Amazon AWS, Google cloud etc. Application hosting and running over public cloud has its …
In the hosting web sector, there is a lot of confusion regarding the technological differences between cloud hosting and VPS hosting. Most people misinterpret the fundamental distinction between the two due to the lack of understanding of the key distinctions …
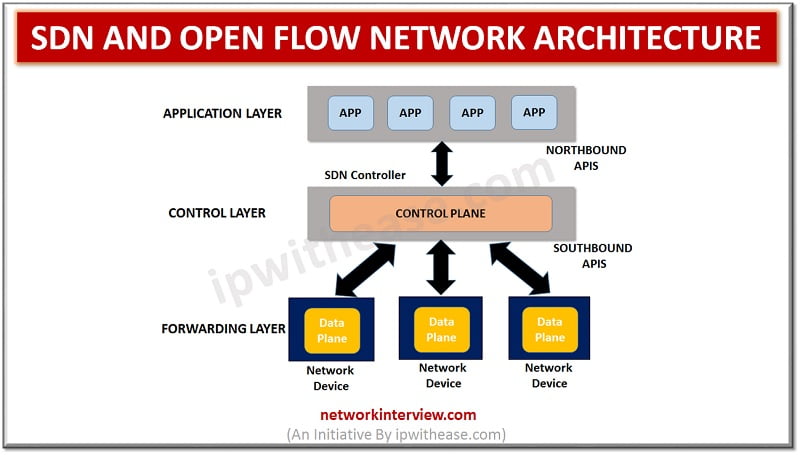
SDN technology detaches dependency on binding both hardware and software. Starting with the SDN network 10 years back, a number of start-ups started to develop open networking systems and white box switches for data centres. In this article we will …
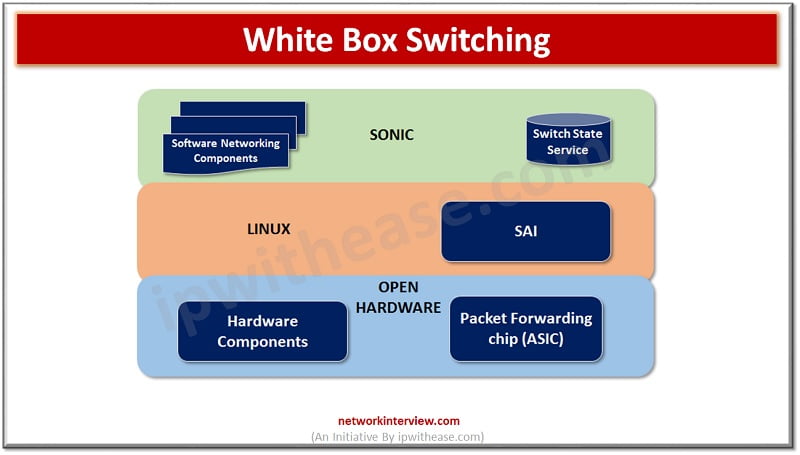
Network switch is the main component of telecommunication networks especially in the case of fiber optics networks. In the traditional switch choice of a specific vendor switch you are bound by software provided by the vendor. The switch market is …
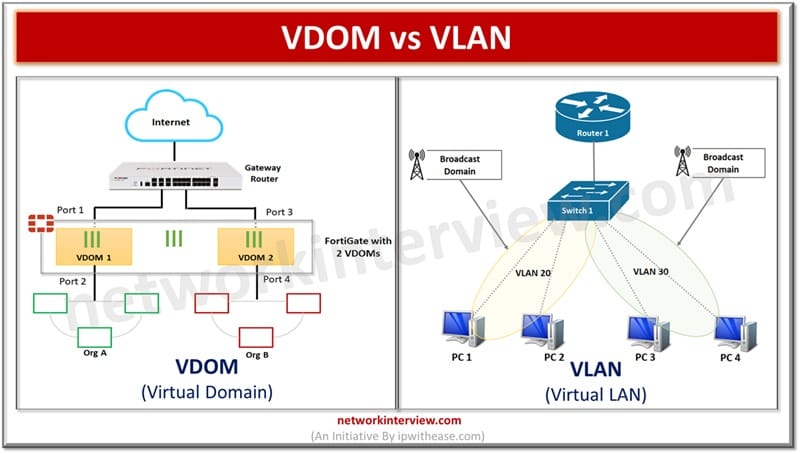
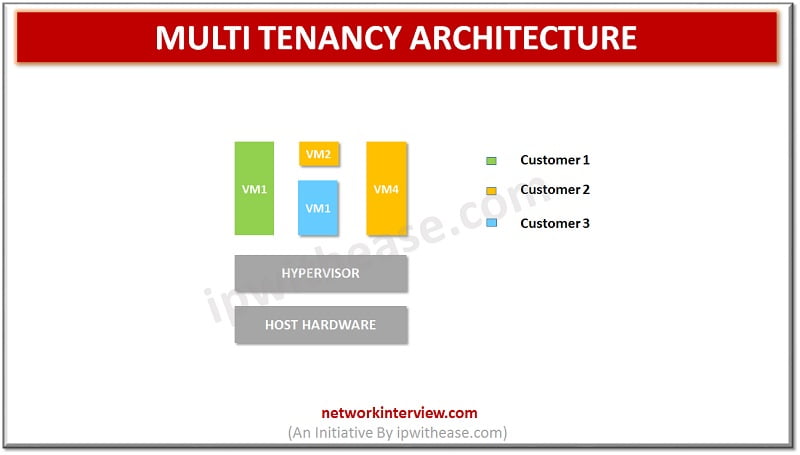
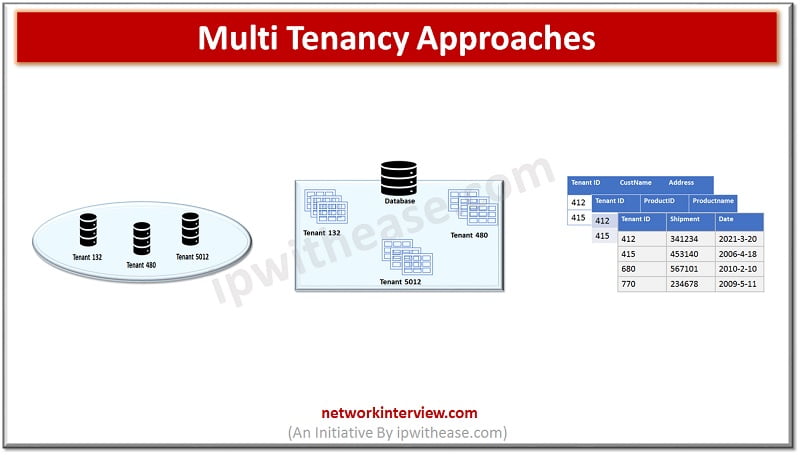
Introduction to Multi Tenancy Advent of cloud computing had brought many new models of delivery and services in Infrastructure services, Application services, Network services and so on. Cloud computing provides a cost-effective way to use computing resources, share applications, share …
Introduction to Multi Tenancy in Cloud Multi Tenancy offers customers , organizations and consumers which are sharing infrastructure and databases to gain advantages on price and performance front. Service offerings available through cloud involve customers (or ‘tenants’) getting a piece …
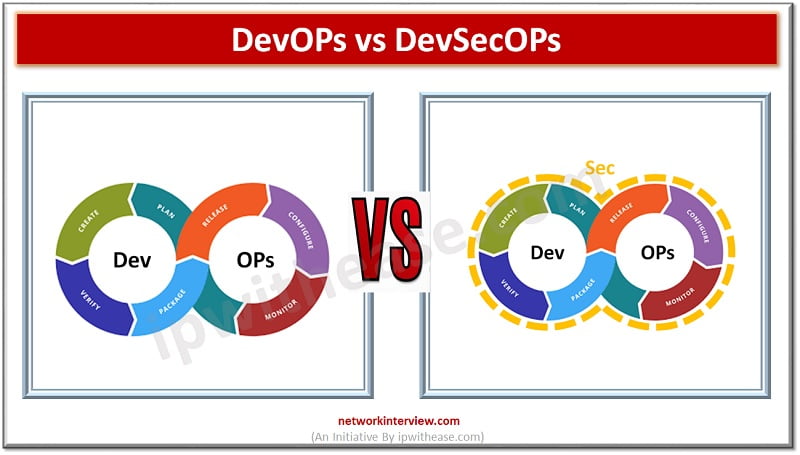
Software development and operations teams are always striving to establish a consistent environment for development globally. The products are brought from hands of developers to customers however the existence of silos between development, QA and operations teams always create conflicting …
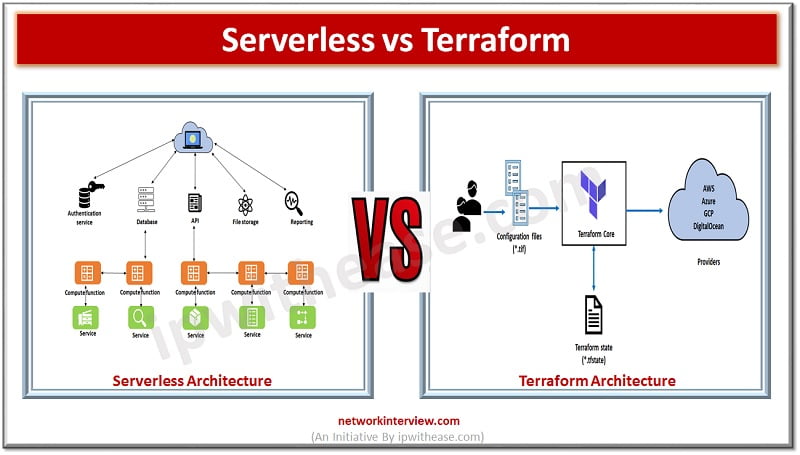
Infrastructure as a code is one of the greatest changes brought by DevOps in recent times. Complicated provisioning, deployment and release of cloud infrastructure processes which required following complicated steps where cloud resources were created manually is a thing of …
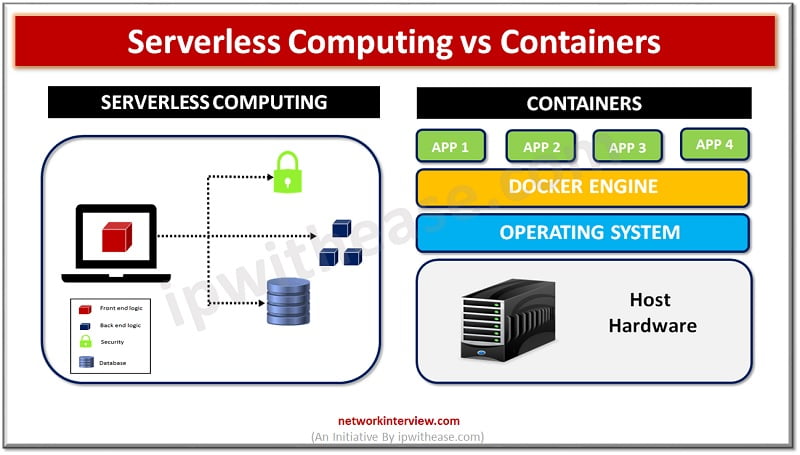
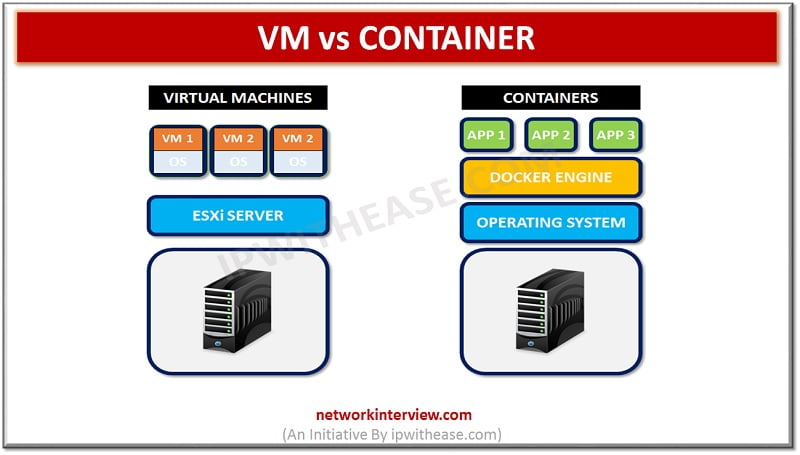
Introduction In the era of enterprise computing organizations are seeking ways to develop, deploy and manage applications in a more efficient , fast and scalable manner. Traditionally applications are tightly linked to servers and the operating systems which executed their …
Data centres operations be it from cloud or on premises network is the backbone of these infrastructures which supports businesses starting from application delivery to security. As workloads are changed, migrate, evolve networking technologies too need to match the pace. …
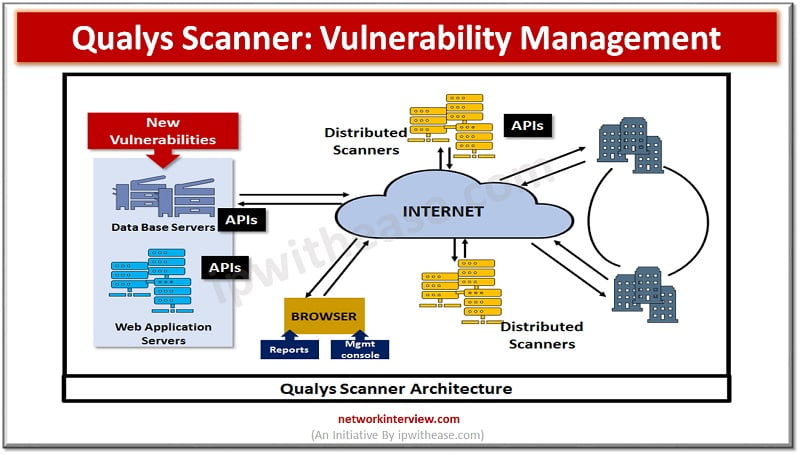
Vulnerability management is a critical component of risk management as attackers are always looking for new vulnerabilities to exploit and take advantage of them which may have gone unnoticed. Several Vulnerability management tools are available in the market which help …
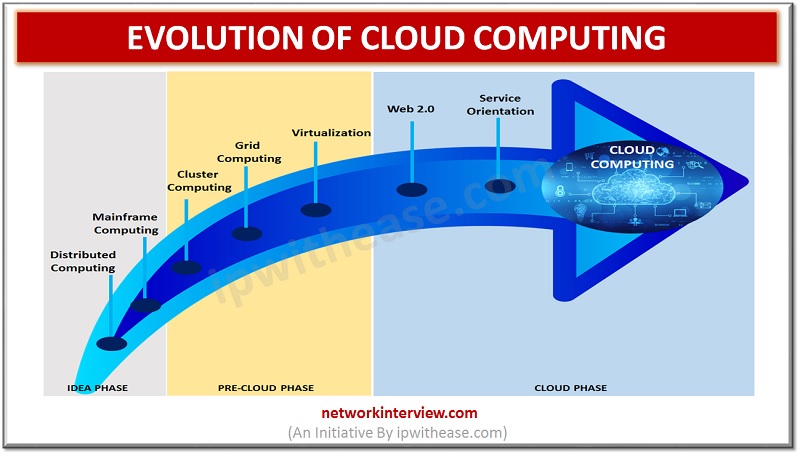
Introduction to Evolution of Cloud Computing Cloud computing is playing an important role in everyone’s life. We cannot imagine a world without Cloud Computing techniques to handle Big Data. But we didn’t reach this level in few years. The evolution …
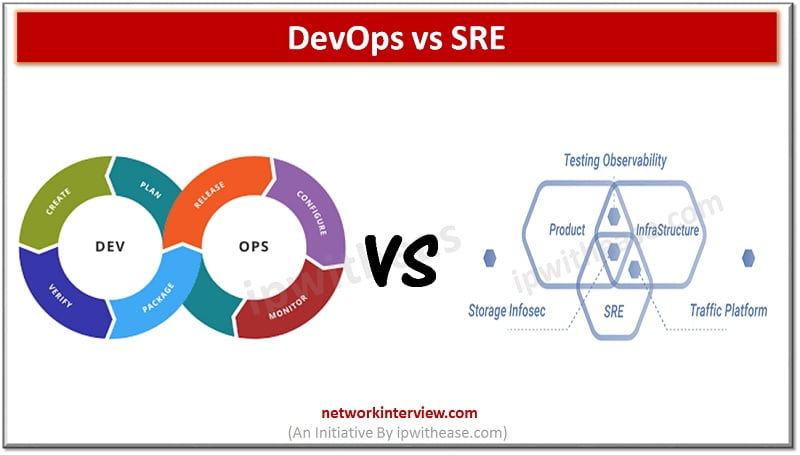
Introduction: DevOps vs SRE After Google introduced Site Reliability Engineer into the software development process, the whole IT industry was confused and had this question “What is the difference between the DevOps and SRE?” In short, there is not much …
SDN and Open Flow Network Architecture With colossal growth in Cloud computing and Intent based networking, SDN technology has clearly lead the race. Infact SDN has also catered to needs of overgrowing demand on IT for faster response to requests …
VM VS CONTAINER Virtual Machines VM or Virtual machine enables you to create and operate a discrete virtual environment- an operating system, acting like an individual computer. Through VMs, softwares that cannot work on your main OS, can easily work …