In the dynamic world of data analytics, professionals who hold a Master’s in Data Analytics are in high demand. The USA, renowned for its top-notch education and thriving job market, is an ideal destination for pursuing this advanced degree. In …
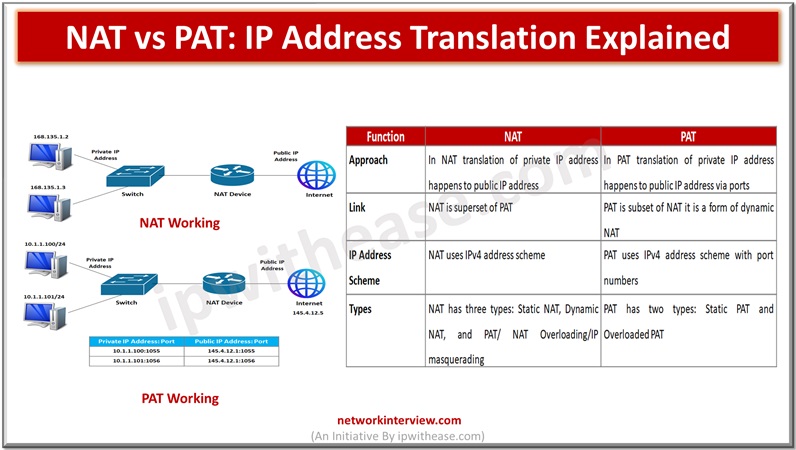
In the networking world IP address translation is required so that internal systems could have access to the external world or Internet. The IPv4 scheme can have a maximum of four billion IPv4 addresses in theory but the actual number …
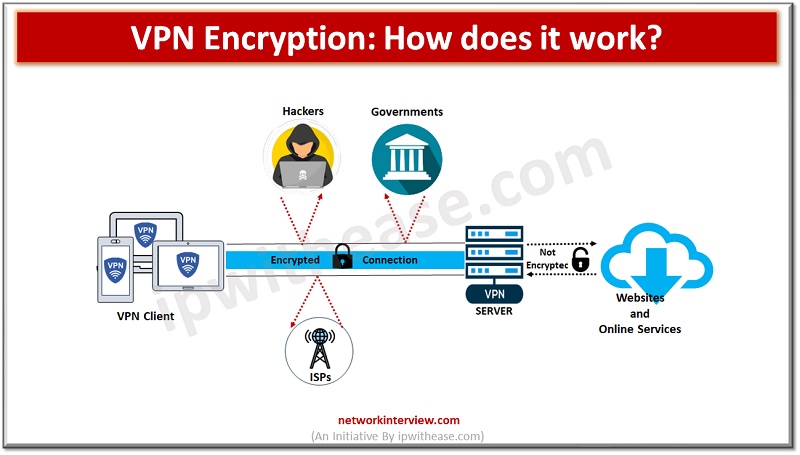
Security is of paramount concern while using the Internet and its services. Have you ever thought about how secure your data is over the Internet while working? When I am connecting to the Internet, we are taking ISP services so …
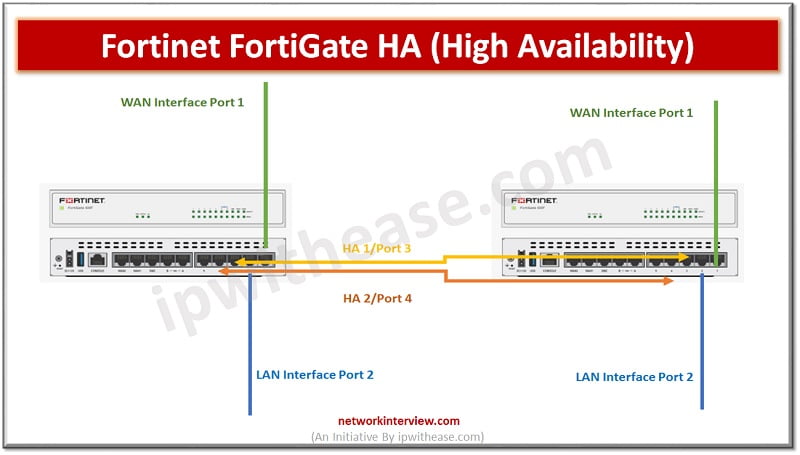
Objectives High Availability HA Modes FGCP (FortiGate Clustering Protocol) Heartbeat Interfaces and Virtual IP Interfaces HA Requirement Configure Primary FortiGate Firewall Configure Secondary FortiGate Firewall HA-Troubleshooting What is High Availability? High Availability (HA) is a feature of Firewalls in which …
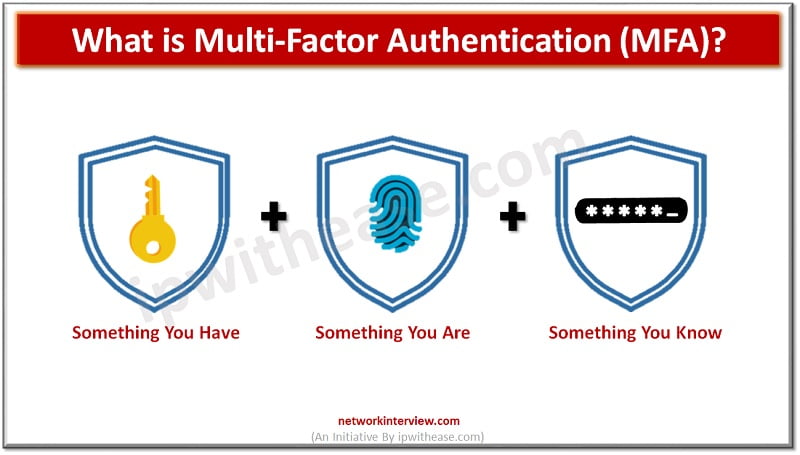
Companies of all sizes are becoming increasingly aware of the need for stronger user authentication to reduce the risk of cyber attacks. This is particularly true in light of recent high-profile attacks on accounts from Internet users such as celebrities, …
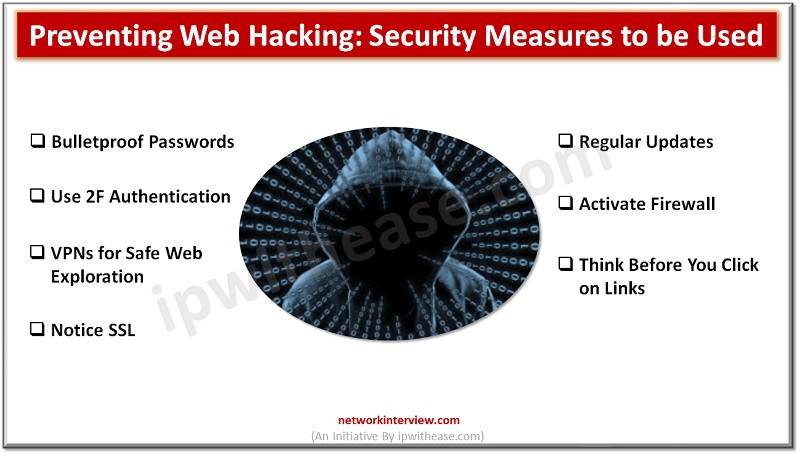
Web hacking is scary. We all know that! Yet, we need to talk about web hacking. The 2021 Cyber Threat Report by SonicWall reveals an alarming 62% increase in ransomware worldwide. Frightening, isn’t it? In this blog post, we’re going …
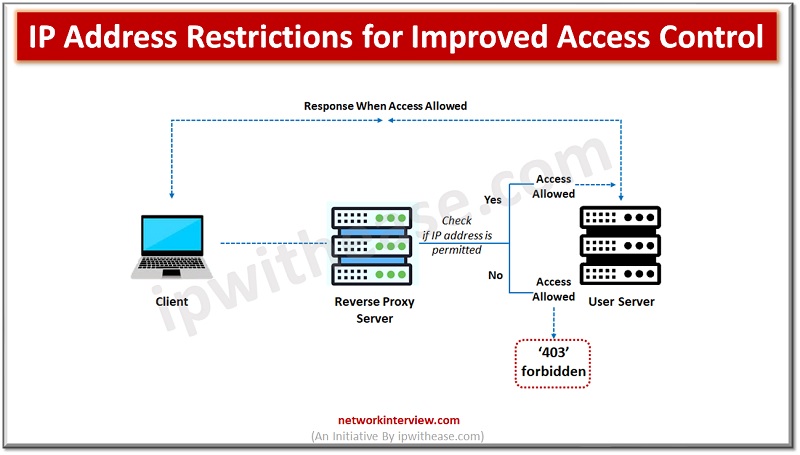
Network security is of paramount importance for IT administrators. Various ways and means and a variety of tools are used to protect organization networks from internal and external attacks. All communications in a network happens via IP addresses as per …
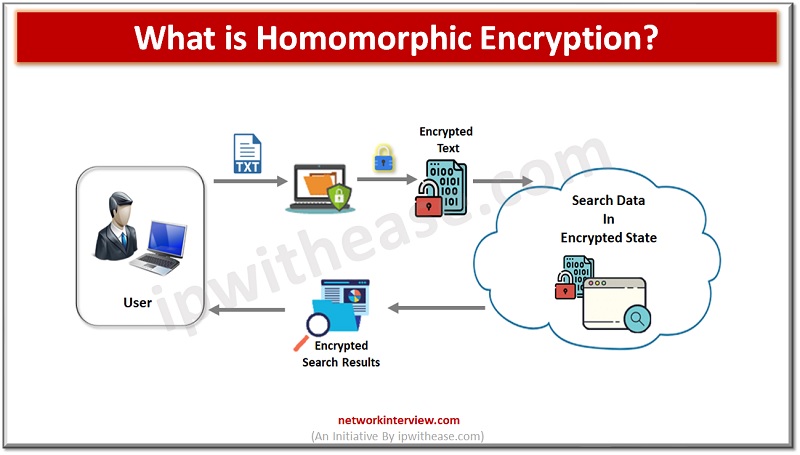
Homomorphic encryption is a powerful and innovative type of encryption that promises to revolutionize the way that data is secured and shared. HE is a relatively new technology and is still in the early stages of research and development. However, …
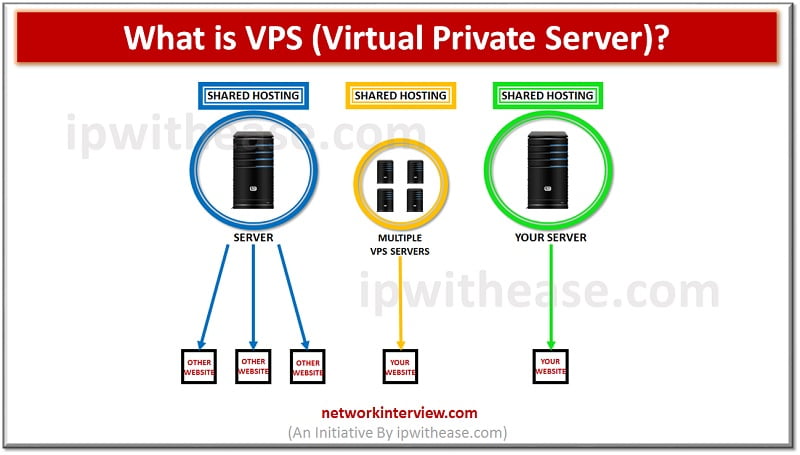
Introduction to VPS (Virtual Private Server) In the IT community, we define with the term VPS (Virtual Private Server), any virtual machine that is sold as a service by an Internet Hosting Service. In normal conditions, a virtual private server …
Are you ready to take your networking career to the next level? The Cisco Certified Network Associate (CCNA) exam is a crucial stepping stone towards achieving that goal. Whether you’re just starting or looking to enhance your skills, passing the …
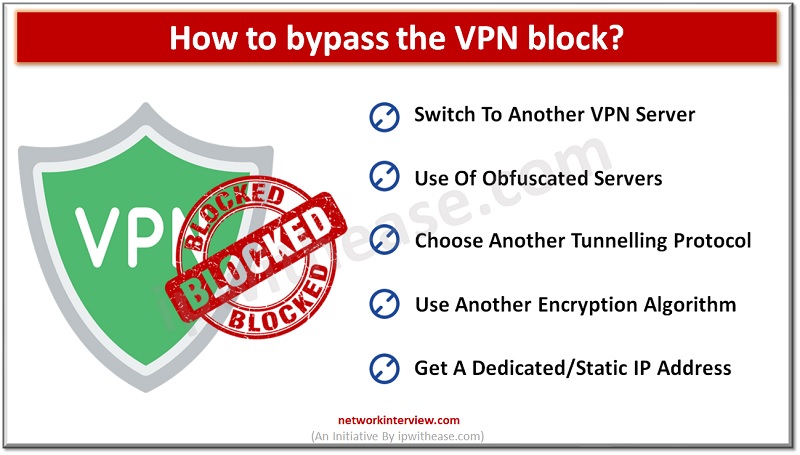
Well, not always. As VPN is a new concept , so the rules are murky and open to multiple interpretations. Though all good VPN companies will do their best to protect your data, privacy, and overall security on the web, …
Introduction to ISP & VPN Internet service providers (ISP) facilitates internet navigation and helps in transmitting all your Internet packets however VPN creates a secure tunnel where data is encrypted during transmission. Often people get confused between the two terms …
As the world becomes increasingly digital, the need for efficient, reliable, and cost-effective networking solutions is more critical than ever. One such solution that has gained popularity in recent years is the Virtual Router. In this article, we will learn …
The cybersecurity industry has become increasingly competitive, making it essential for professionals to validate their skills through certifications. Cisco offers a range of CyberOps certifications that are highly sought after by employers. In this article, we will guide you through …
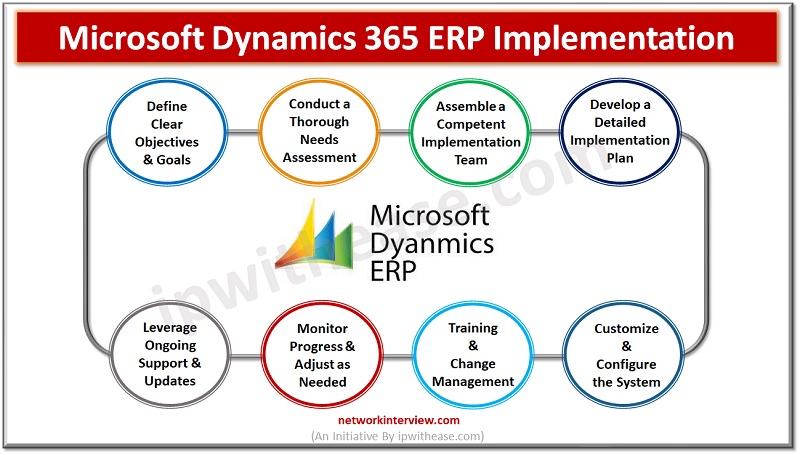
Organizations are continually looking for methods to improve efficiency, simplify processes, and boost profitability in today’s dynamic business world. Microsoft Dynamics 365 ERP, an integrated enterprise resource planning system created to improve many parts of corporate management, is one of …
Dynamic changes have happened in the financial area over ongoing years. IT (Information Technology) services are indispensable to this change’s prosperity. IT services envelop assorted advancements and arrangements and oblige numerous requirements across different businesses. For this situation, monetary establishments …
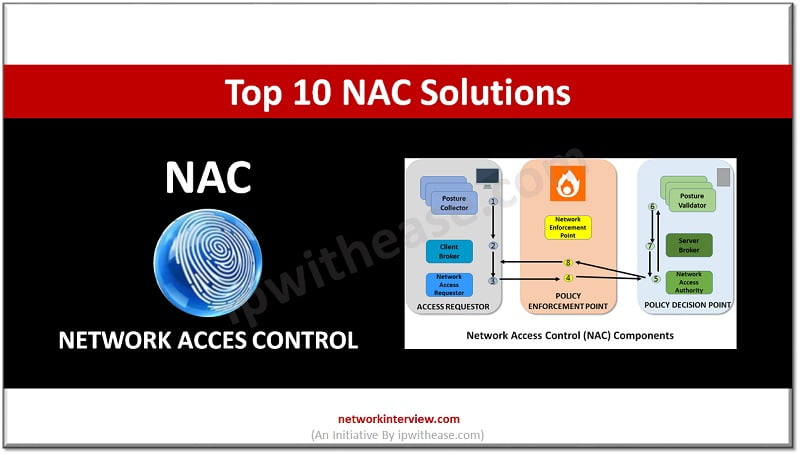
In today’s internet world a good NAC solution partner is needed for every company involved in the digital or e-commerce industries. In this article, you will get to know the top 10 NAC solutions for your business. Let’s start the …
In today’s world, securing online businesses and safeguarding sensitive data is a top priority for web-based businesses. Network access control (NAC) solutions have become highly useful in achieving this crucial goal. NAC systems act as gatekeepers, controlling who can access …
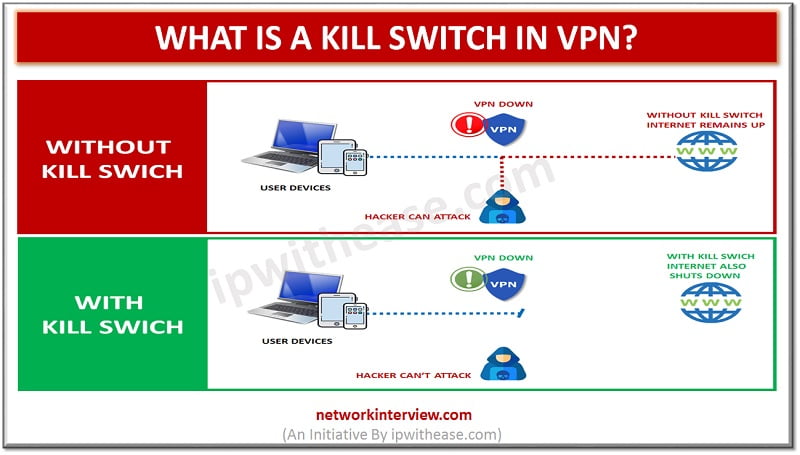
Kill switch in VPN A VPN kill switch is also known as an internet kill switch. For the VPN security solution, a VPN kill switch is a critical piece. It is considered to be the top feature for the best …
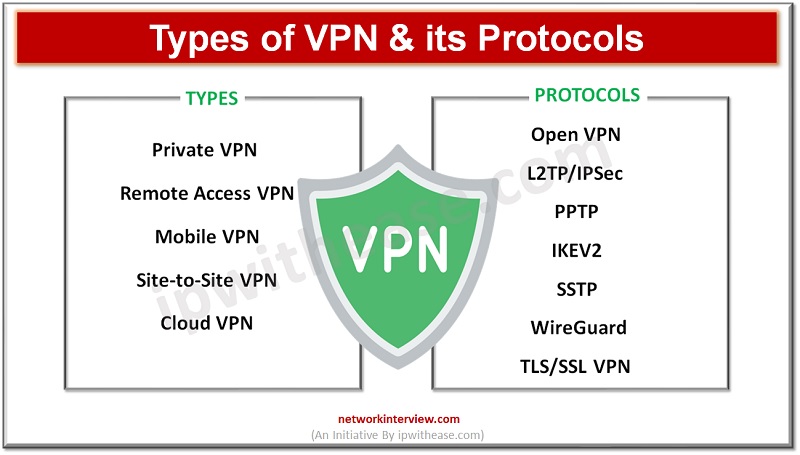
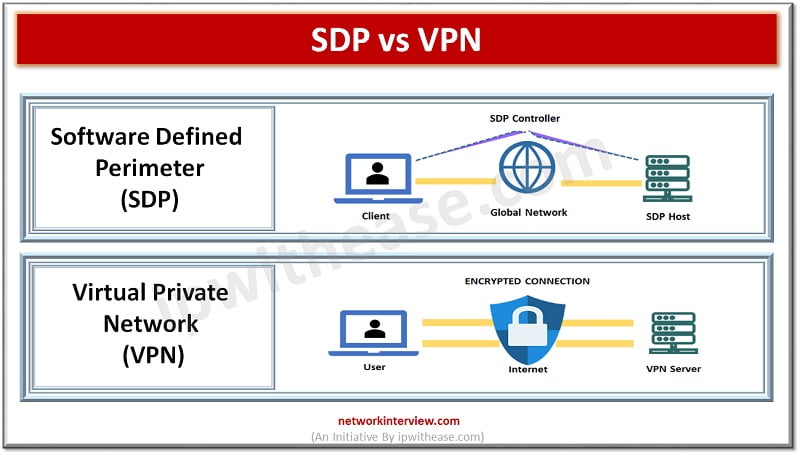
VPN (Virtual private Network) has become an essential part of network and security suite when it comes to secured communication over Internet. VPN forms secured tunnels between a local client and a remote server. Remote and mobile workers use VPN …
We occasionally run into issues online browsing that prevent us from visiting a website. Our connection, the software we employ, or the device itself may occasionally be at fault. However, the website may be preventing us due to a fault. …
A Virtual Private Network (VPN) is a technology that creates a secure and encrypted connection over the internet, allowing users to access the internet as if they were connected to a private network. VPNs are used for several purposes, primarily …
Adapting to the evolving digital landscape is essential for businesses of all sizes. Today, every business is striving to establish a strong online presence. And as today’s customers demand more, businesses can no longer ignore the significance of digitalization. This …
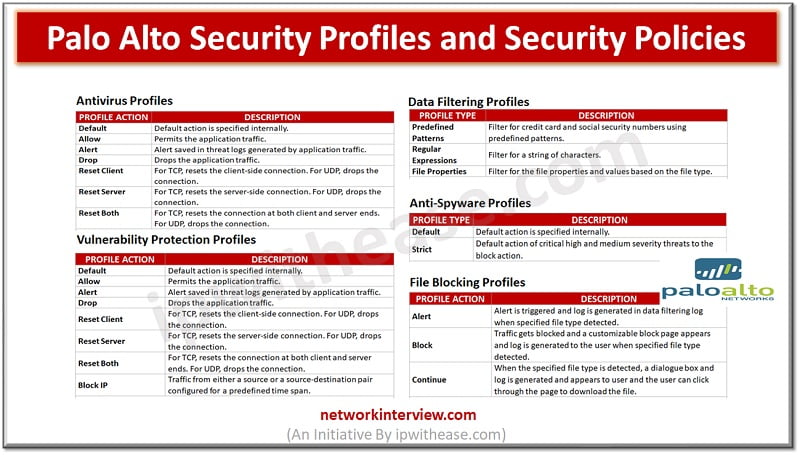
Below are the key profile types provisioned in Palo Alto Firewall. Lets discus all the profile types one by one – Palo Alto Security Profiles & Security Policies While security policy rules enable to allow or block traffic in network, …
In the digital age, email remains a cornerstone of communication. However, the traditional email experience is undergoing a metamorphosis, thanks to the infusion of Artificial Intelligence (AI). Let’s explore this transformative journey. The Email of Yesteryears Historically, email platforms were …
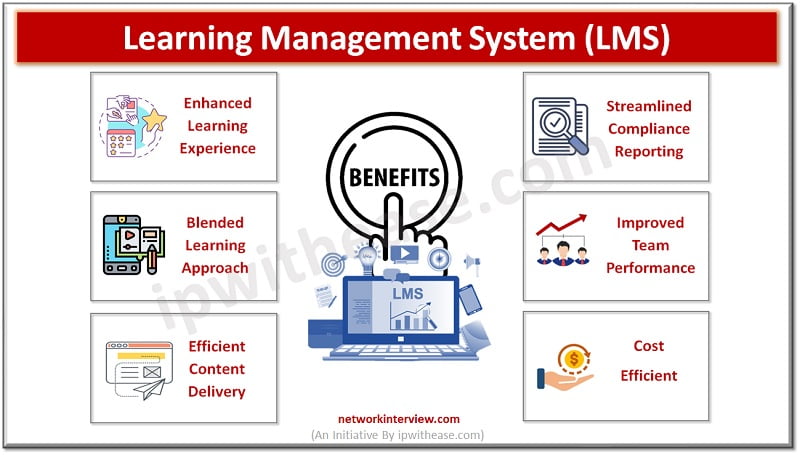
In today’s digital age, online learning has become an integral part of education at all levels. It’s no surprise that businesses are also embracing this technology to enhance their training and professional development programs. One tool that has gained popularity …
Unless you’ve been living on another planet for the last several years, you’ll have heard the term “cyberattack” thrown around literally everywhere—from news channels to social media. For some people, the concept of a cyberattack is still a little hard …
Ethical Hacking and cyber security are two concepts we often remain confused about. To get a basic idea of the difference between ethical hacking and cyber security, remember that both terms have the same goal: to keep data safe. The …
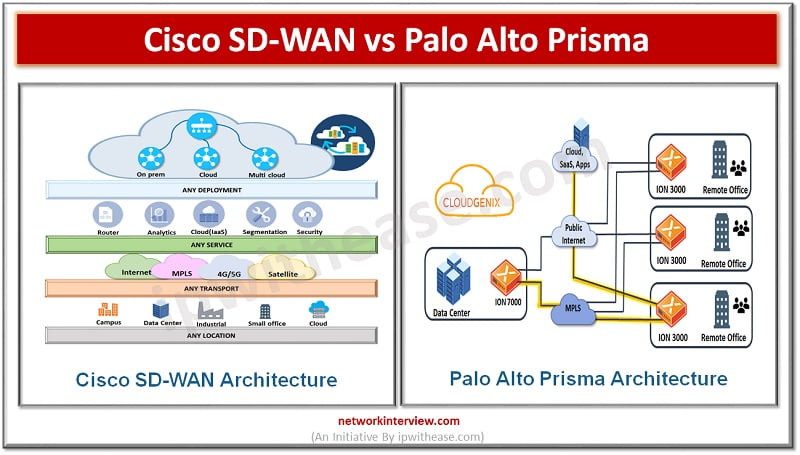
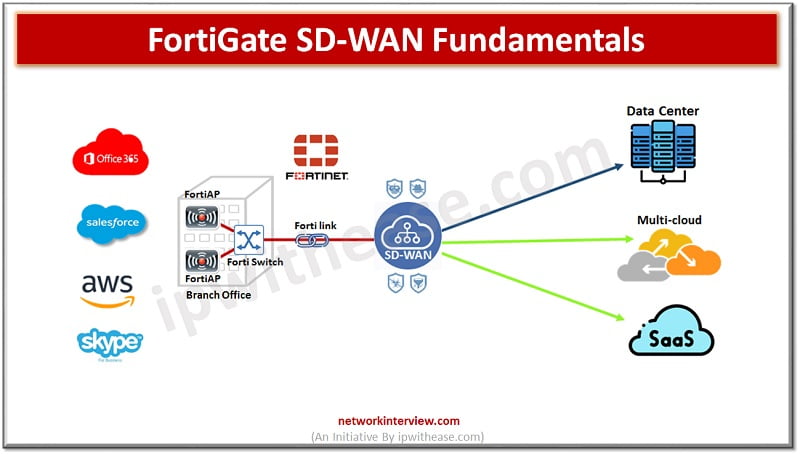
SD-WAN Solutions Penetration of cloud all around the enterprises also brought the need for hybrid networking solutions supporting private WANs and commodity Internet connections to support adoption of cloud applications, remote connectivity, scalability with application performance and including visibility. Major …
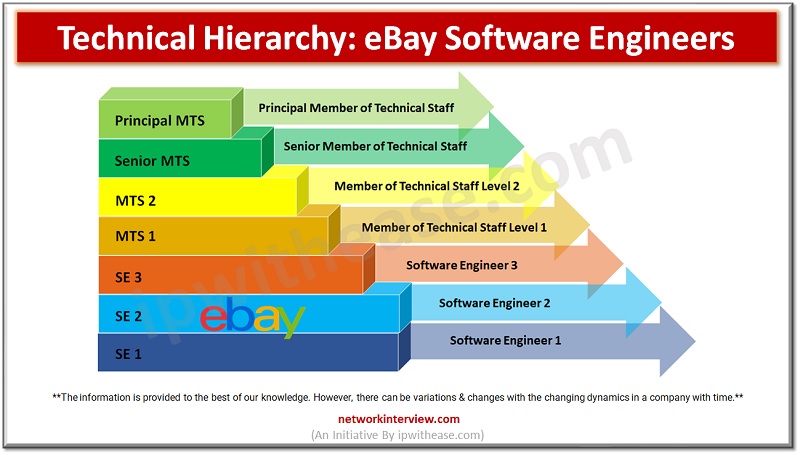
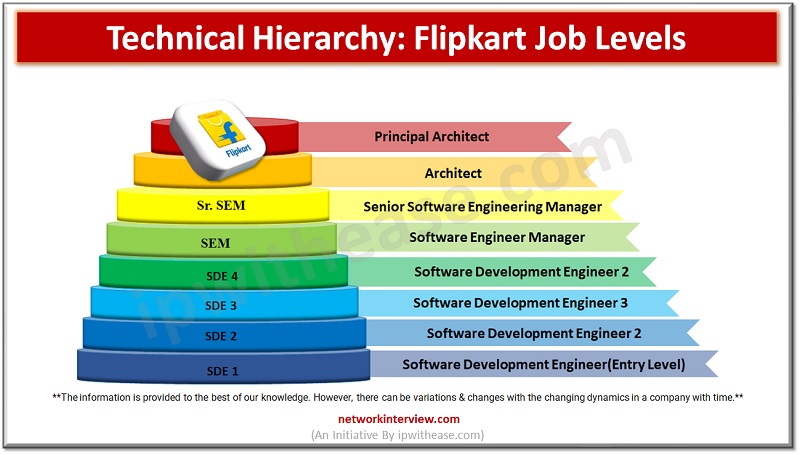
As the E-commerce industry has boomed very fast in the past years, many new engineering and other IT graduates are willing to get a job at E-commerce companies like Amazon, Flipkart, eBay, etc… But it’s important to know about the …
In today’s remote world E-commerce and logistics have been achieved as a successful industry. So it is a common interest for many of the new graduates to get a job at E-commerce giants like Amazon, Flipkart, and eBay. Are you …
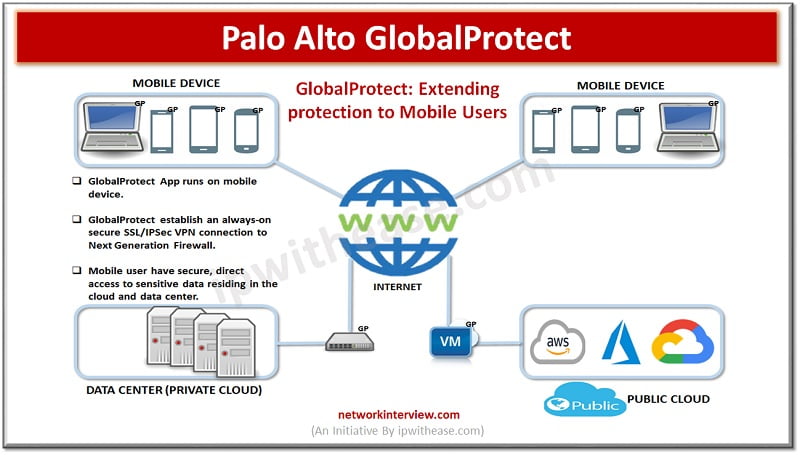
Introduction Palo Alto GlobalProtect is a network security for endpoints that protects mobile workforce by extending the Next-Generation Security Platform to all users geographically anywhere. GlobalProtect secures traffic by applying security policies with Palo Alto next-generation to the application. GlobalProtect …
Artificial intelligence is becoming so deeply intertwined with our lives. And slowly, it’s making his presence known in the field of education too. There is an increased need to move past the traditional ways of learning and teaching. Indeed, some …
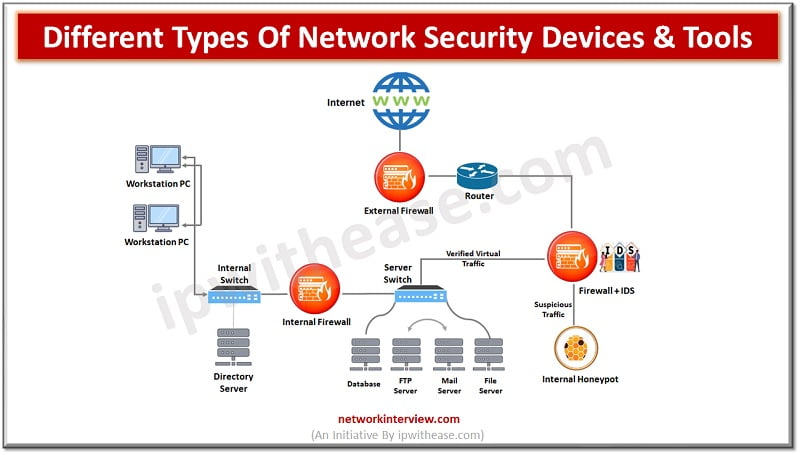
There are several aspects to security and Network Security is one of the key components in this. Network security protects networks from unauthorized access and threats. Organizations deploy or adapt measures to protect networks from malicious attackers. Network security devices …
SD-WAN Local Breakout SD-WAN is a virtual interface which connects different link types using a group of member interfaces. Using SD-WAN simplifies configuration for administrators who can configure a single set of routes and firewall policies and deploy them to …
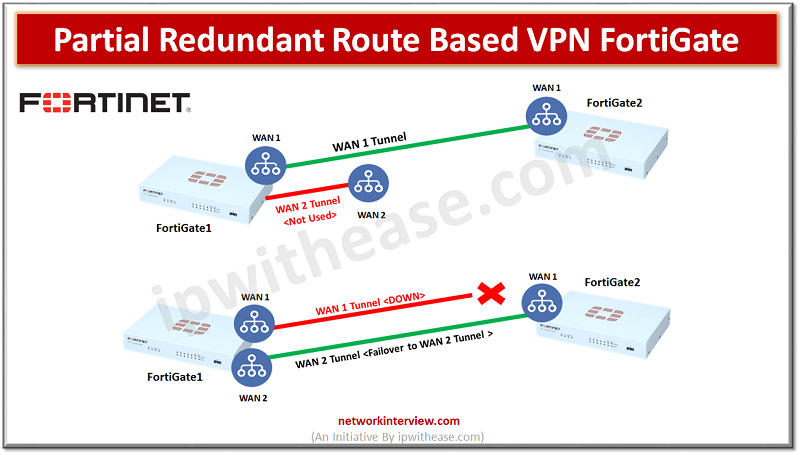
Objectives FortiGate1 has two WAN links and FortiGate2 has single WAN link Create site-to-site route based VPN with Redundant Connection Configure Dead-Peer-Detection failover Configure Link-Health Partial Redundancy is where we don’t have primary and secondary WAN connections on both peer1 …
Artificial intelligence (AI) models are now widely used in many applications, including natural language processing, autonomous cars, and medical diagnosis. These AI models mainly rely on data annotation, a vital step in supervised learning that includes labeling data. The caliber …
Due to the rapid deployment of technology in the educational sector, the way we interact, learn, or teach knowledge is transforming. The EdTech revolution in software development offers a plethora of applications that are shaping today’s educational landscape. The term …
What is URL Filtering? Sometimes you browse your favorite social networking site on any of the web browser and that web browser displays the message “You are not allowed to browse following website”. This is because of the URL filtering. …
What is Dark Web? The dark web, a concealed part of the internet, serves as a shield for users’ online privacy against traffic analysis attacks. Accessible only through specialized dark web browsers or technologies, it remains intentionally hidden. How is …
Traditional model of working from the office is quickly diminishing and becoming a thing of the past. As we transition to a hybrid model of working, network security becomes more and more complex. At the same time organizations resources are …
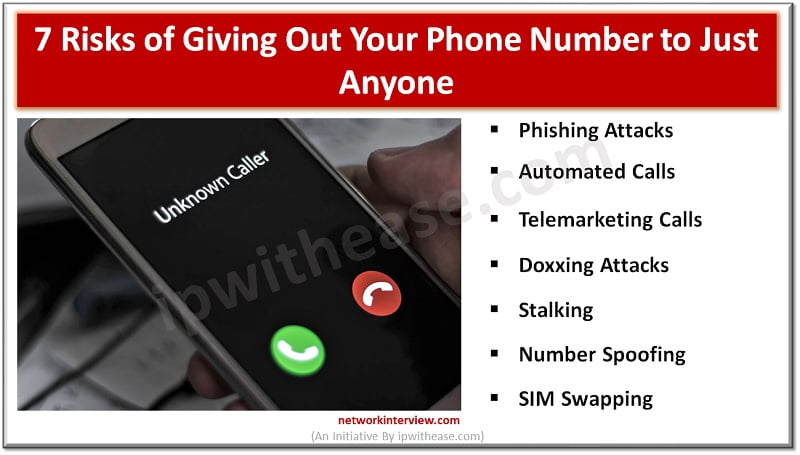
Many people don’t think twice about giving out their contact numbers. But did you know that this seemingly ordinary practice could expose you to a variety of threats? The fact is, your phone number belongs to personally identifiable information, commonly …
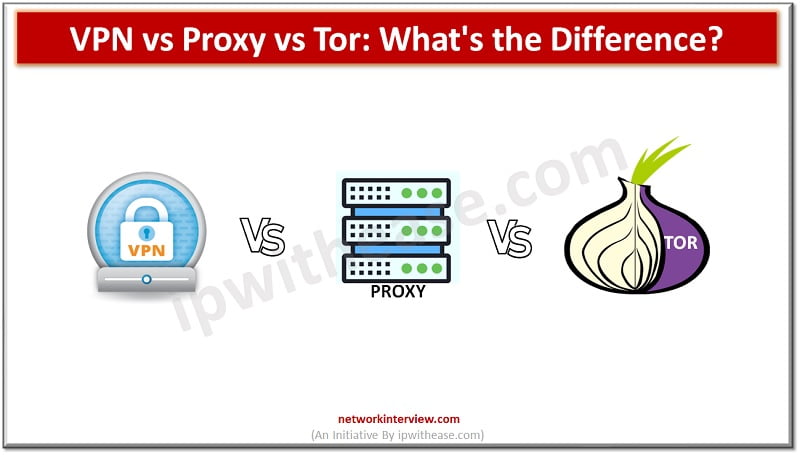
In today’s digital age, protecting our privacy and security online has become increasingly important. With the rise of cyber threats and the constant tracking of our online activities, it’s crucial to find effective ways to safeguard our personal information. Three …
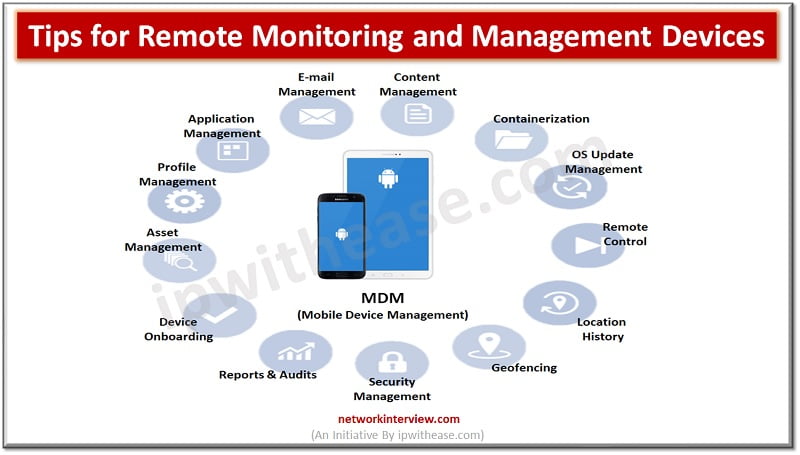
In today’s fast-paced and interconnected world, businesses rely heavily on technology to streamline their operations and stay competitive. With the rising quantity of enterprise devices and the increasing complexity of IT systems, it has become essential for companies to manage …
As a small business owner, one of the most essential decisions you’ll ever make is choosing the right employees for your company. Employees are, no doubt, the most precious asset for the success of every organization. Interestingly, there has never …