Firewalls have come a long way since their inception in the year 1908s. The initial firewall was built by Digital Equipment Corporation (DEC) as a packet filtering firewall which simply inspected packet traffic and if it doesn’t match rules packet …
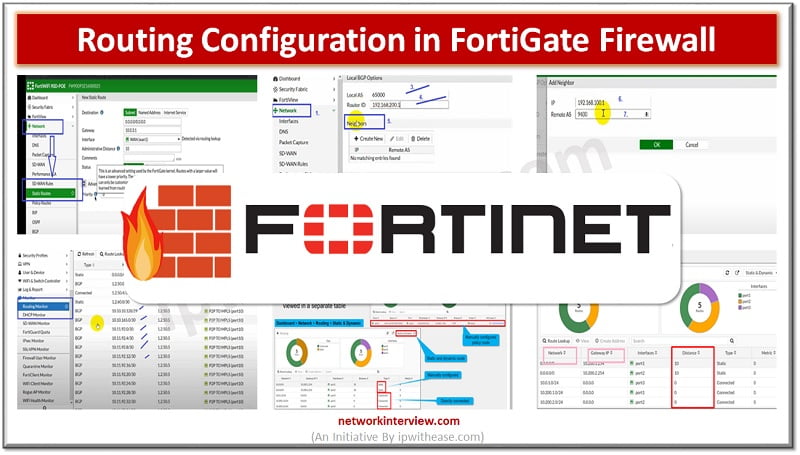
Objectives Routing in Fortinet FortiGate Configuration Steps of Static Routing Configuration Steps of Dynamic Routing (BGP) Policy Base Routing Routing Monitor GUI Troubleshooting Commands for Routing in FortiGate Routing in Fortinet FortiGate Firewall Routing means how a packet can …
Single Sign On & FortiGate Single Sign On Single Sign On (SSO) is a process that allows users to automatically log into every application after being identified, regardless of platform, technology, and domain. FortiGate Single Sign On (FSSO) is a …
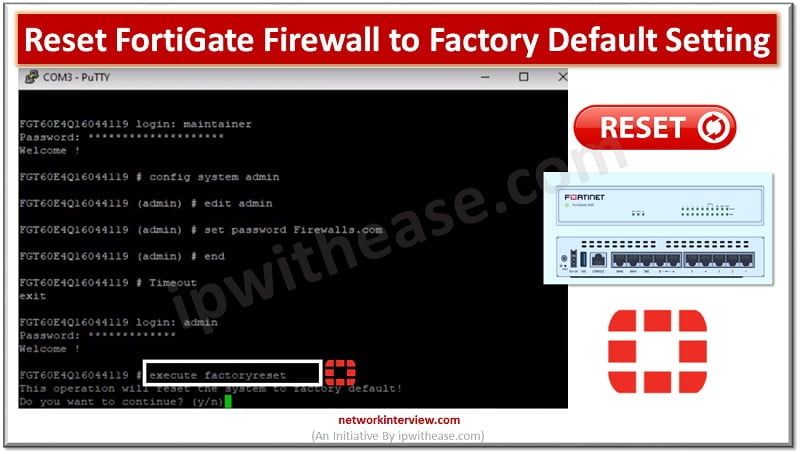
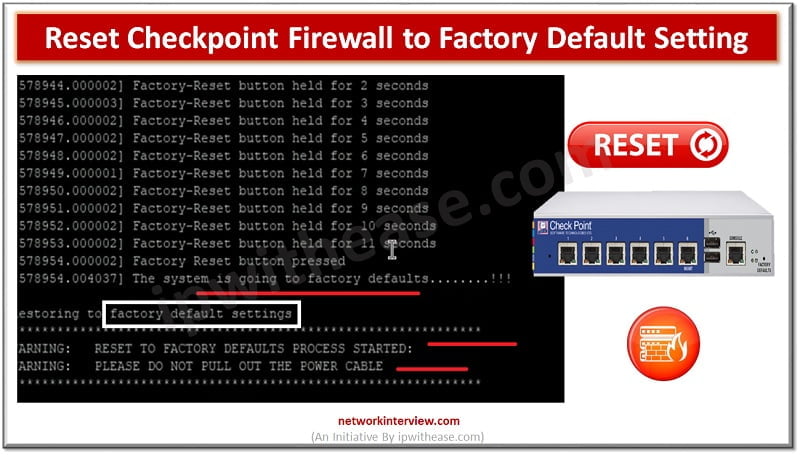
Factory default means resetting the device to the original default configuration and deleting all customized configuration from the firewall/device. Why do we need to reset the firewall to factory default? Device is crashed and need to remove from network Remove …
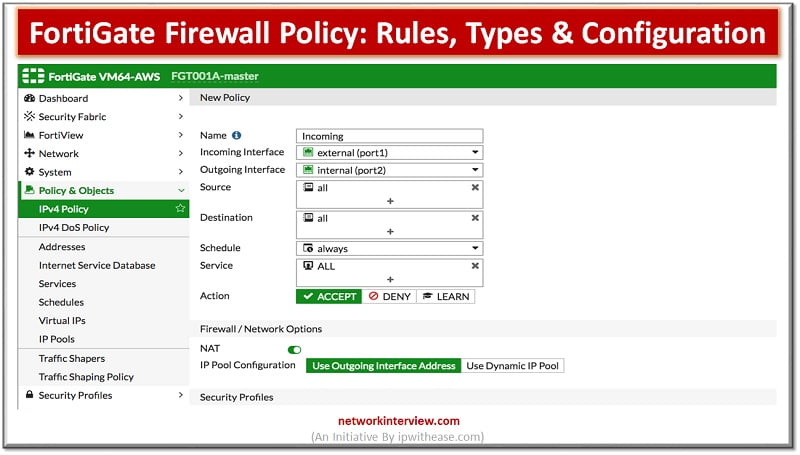
What Are Firewall Policies? Firewall policies define which traffic matches them and what FortiGate does when traffic does match, should the traffic be allowed? Initially FortiGate basis this decision on simple criteria, such as the source of the traffic then …
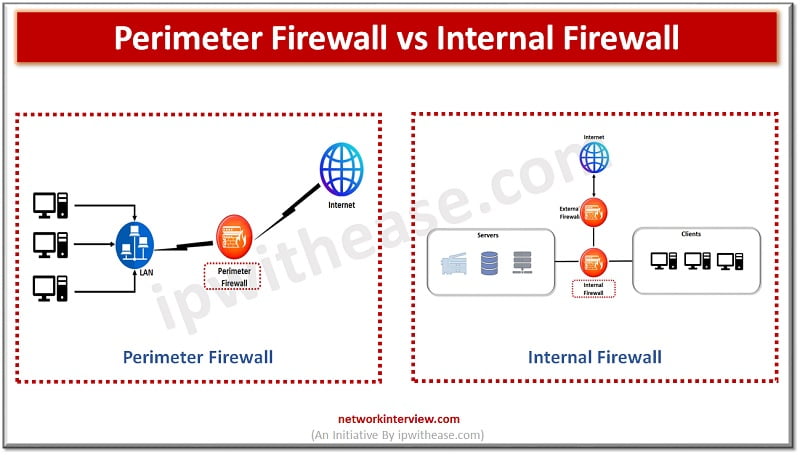
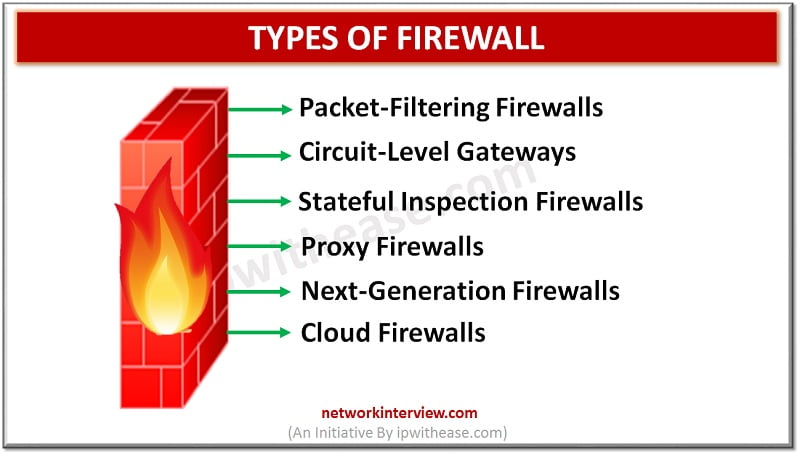
Firewalls are the primary line of defense for organizations; they are there for more than three decades but evolved and came a long way with drastic features and also sold now as separate appliances and make smarter decisions about what …
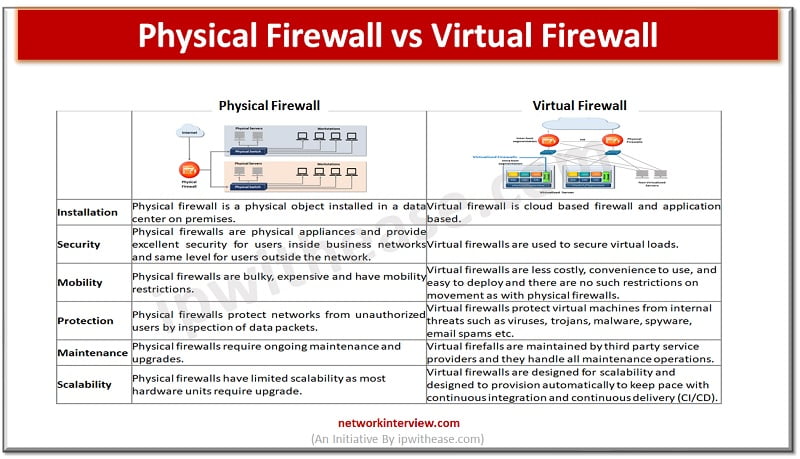
Firewalls are the first line of defense for an organization’s networks. Firewalls come in different categories – they can be a hardware appliance, software based or virtual. The increasing penetration of cloud computing infrastructures has given rise to virtual firewalls. …
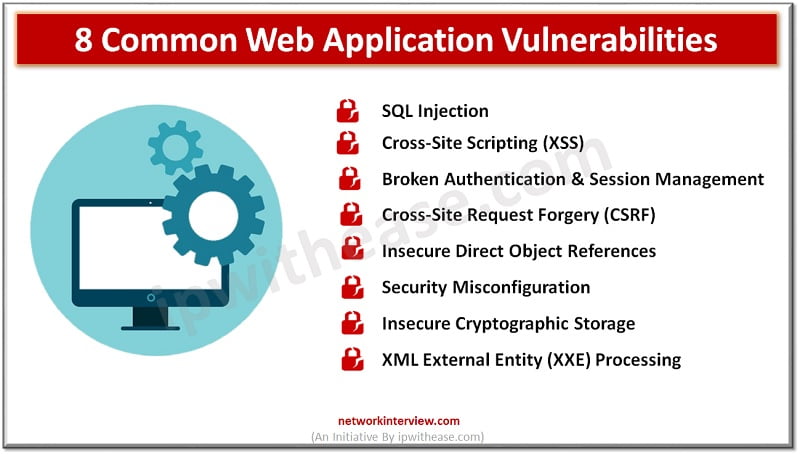
Introduction to Web Application Vulnerabilities Web application vulnerabilities are glitches or imperfections found in the system. These can lead to security risks, such as cyber-attacks or data breaches. Sadly, these risks occur more often than network or asset dangers. According …
Understanding each Encryption Technique When we dive in-depth to explore more about wireless key management and encryption technologies, then we would find that network protocols play an imperative part in it. As we are dealing with the technologies that are …
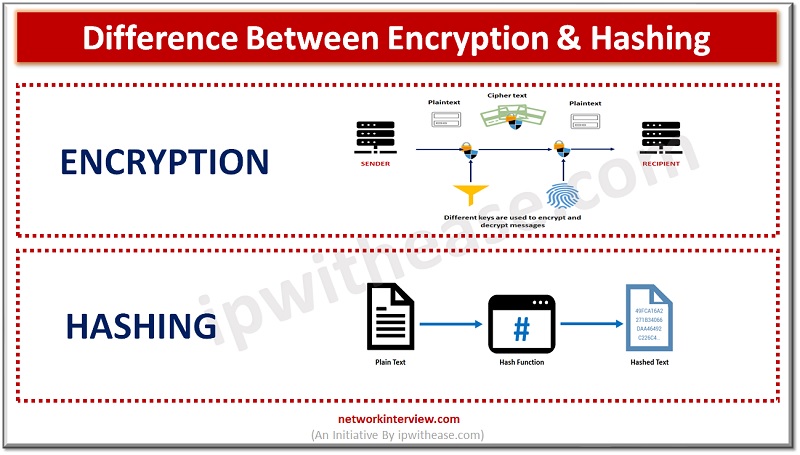
In the realm of data security, hashing and encryption are commonly employed to protect information from unauthorized access. While both methods have distinct processes and advantages, they are occasionally mistakenly used interchangeably. This blog will delve into the definitions of …
The digital marketplace is growing at an unprecedented rate, with e-commerce businesses serving as the cornerstone of this rapid expansion. As these businesses evolve and flourish, they face a pivotal challenge: securing their customers’ financial information. One of the most …
Discussing the implications of VPN providers logging user activity and the importance of privacy policy The usage of VPNs has become increasingly popular among internet users who place great importance on privacy policy and security. VPNs are known for their …
In recent times, the worldwide cyber security scenario has witnessed a surge in potential risks. With the onset of the pandemic, cyber offenders exploited the vulnerability of poorly aligned networks when companies transitioned to remote working setups. The cyber attack …
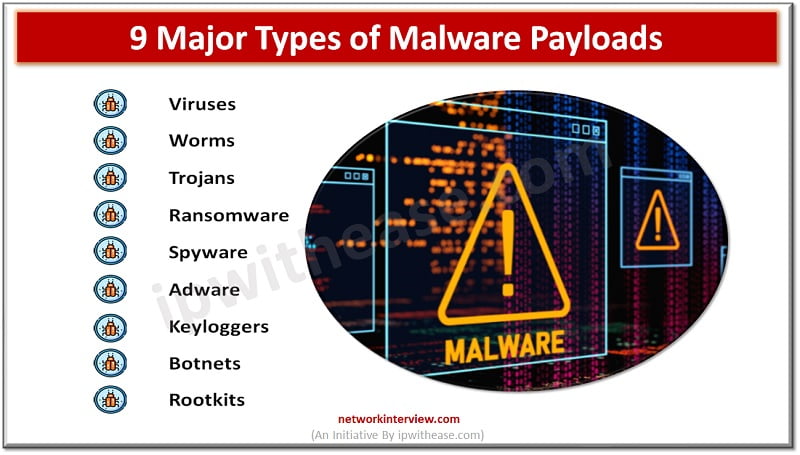
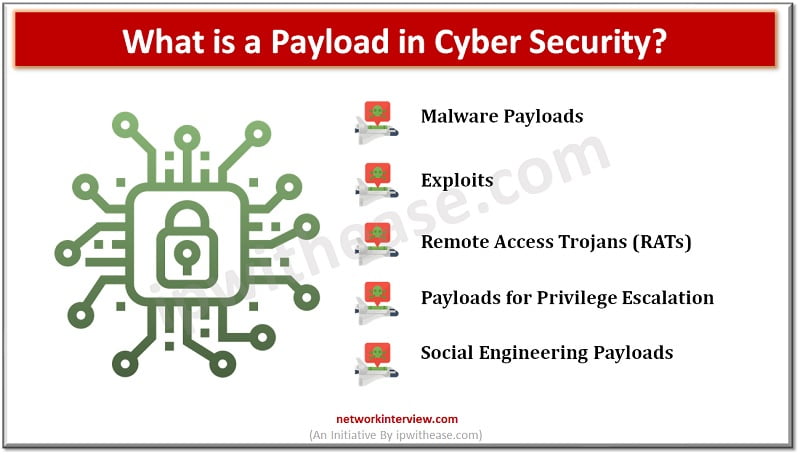
As a cybersecurity professional, you will come across many technical terms and jargon in the field. One of the terms that we often hear in cybersecurity is “payload.” In simple terms, a payload refers to the part of a malicious …
Cyber attacks are becoming more common and sophisticated, which means businesses need to be more prepared than ever before. The COVID-19 pandemic has brought with it a rise in remote work, leading to an increased reliance on technology for business …
Let’s understand the difference between “Reset” and “Factory-Reset”. Reset – Admin can only wipe-out the configuration Factory-Reset/Default – Admin can wipe out the configuration of device and put the device in default operation/firmware. For Example, when you buy a Firewall, …
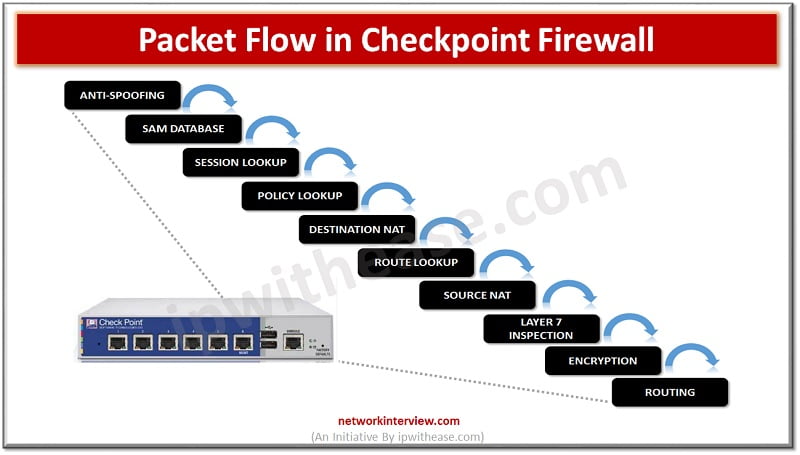
Checkpoint Firewall Packet Flow In the above image Checkpoint Firewall packet flow is shown. Let’s start with Anti-spoofing. Anti-Spoofing Anti-spoofing is a technique which can identify the packet and drop it if the packet has a FAKE/False source address. Let’s …
You might not know, but every domain name (website) has a unique IP address which makes it accessible to the network and users. If you are thinking about why a website has an IP address, then take into account that …
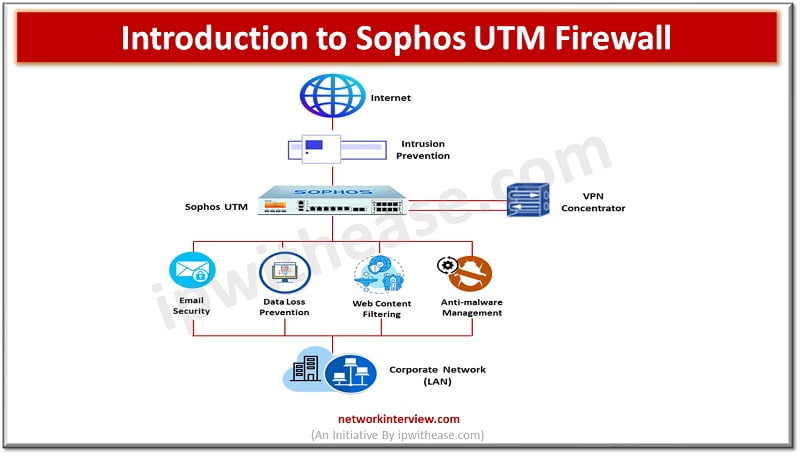
Firewalls have come a long way and have been there for decades to provide protection against malicious attacks and intrusions. In their infancy days firewalls were a simple filtering mechanism based on ports and IP addresses. But over time, firewalls …
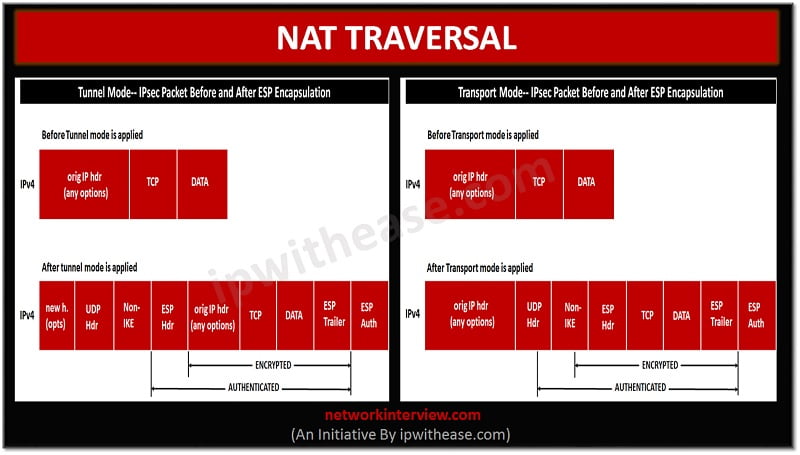
Overview The IPSEC NAT Traversal feature introduces IPSEC traffic to travel through Network Address Translation (NAT) or Port Address Translation (PAT) device in the network by addressing many incompatibilities between NAT and IPSEC. NAT Traversal is a UDP encapsulation which …
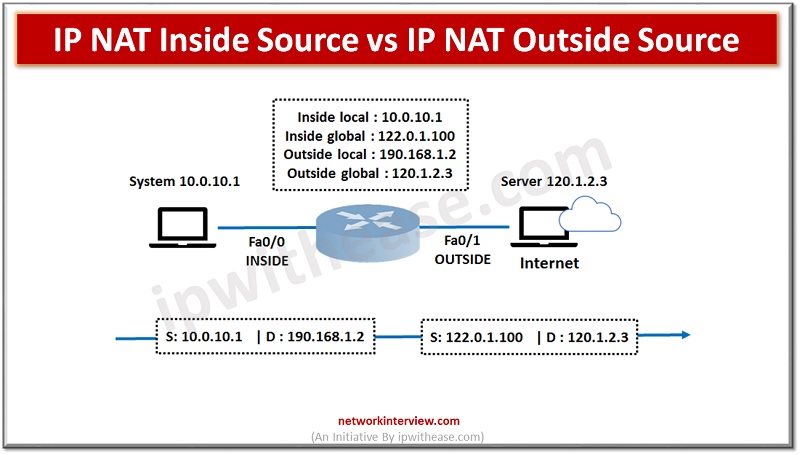
In order to access the Internet, we need one public IP address; however, we can use Private IP address in private networks. The Network address translation (NAT) allows multiple devices to access the Internet with a single public IP address. …
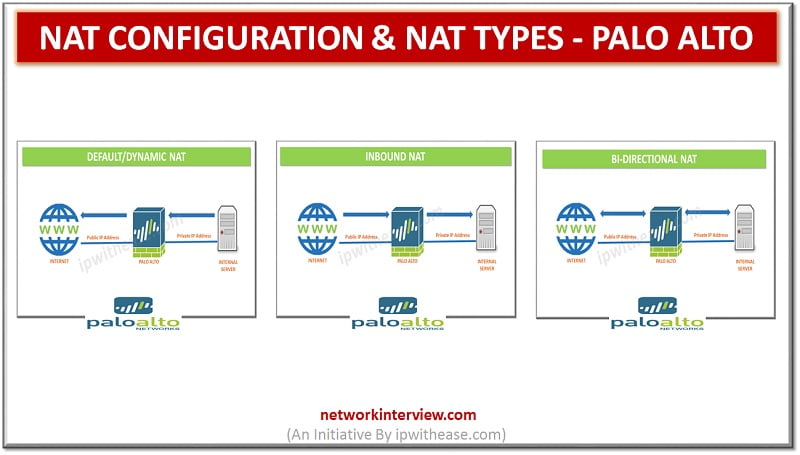
In the previous post we discussed the Architecture of Palo alto firewall. Now, we will discuss the NAT configuration and NAT types in Palo alto. Network Address Translation (NAT) allows to translate private, non-routable IP addresses to one or more …
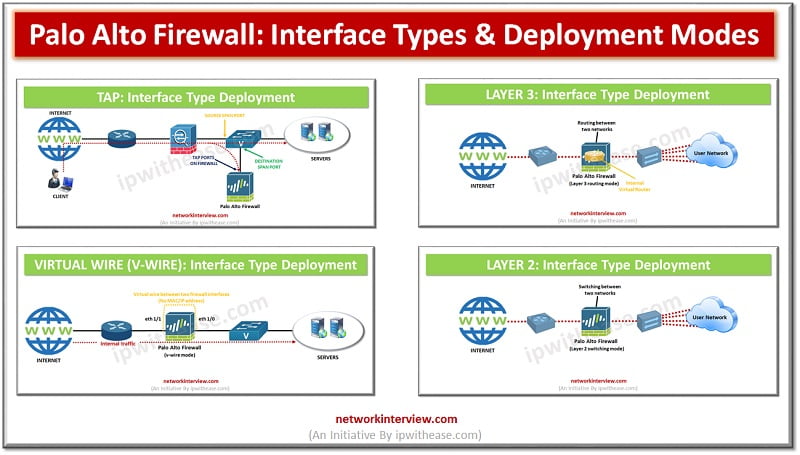
Introduction to Palo Alto Interface types/ Deployment Modes The entry and exit point of traffic in a firewall is enabled by the interface configurations of data ports. Palo Alto being a next-generation firewall, can operate in multiple deployments simultaneously as …
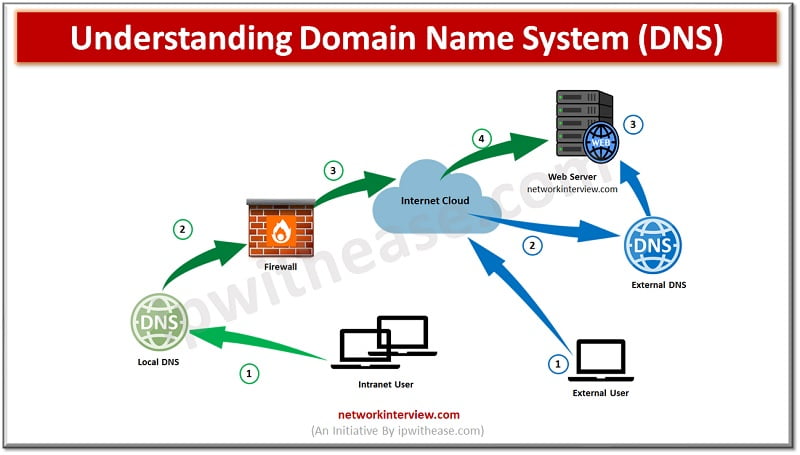
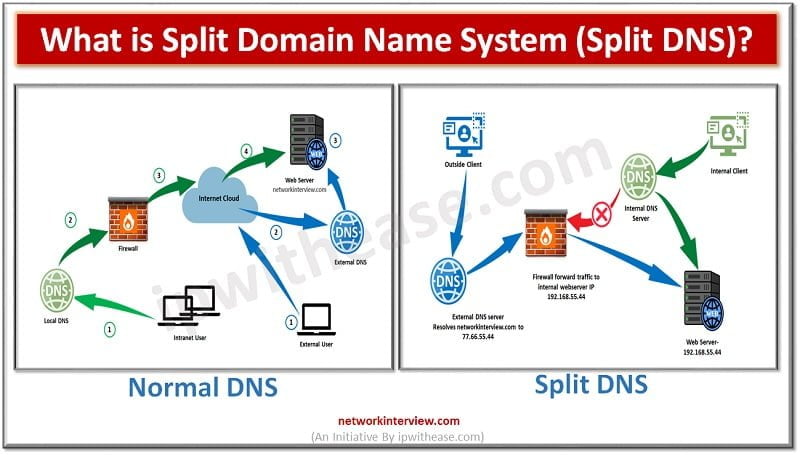
DNS Working Before understanding the Split Domain Name System, let’s discuss how normal DNS resolution works for Internet traffic. However, DNS works to resolve names to IPs. When an Internet client open a Web-browser and type www.networkinterview.com Internet Client will …
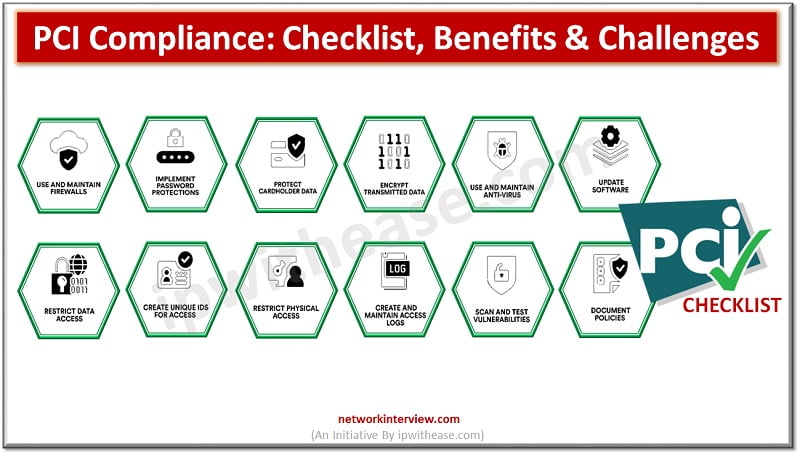
Whether you own a small business or manage a large enterprise, ensuring customer data security is a top priority. To that end, businesses must adhere to the Payment Card Industry Data Security Standard (PCI DSS), a set of security requirements …
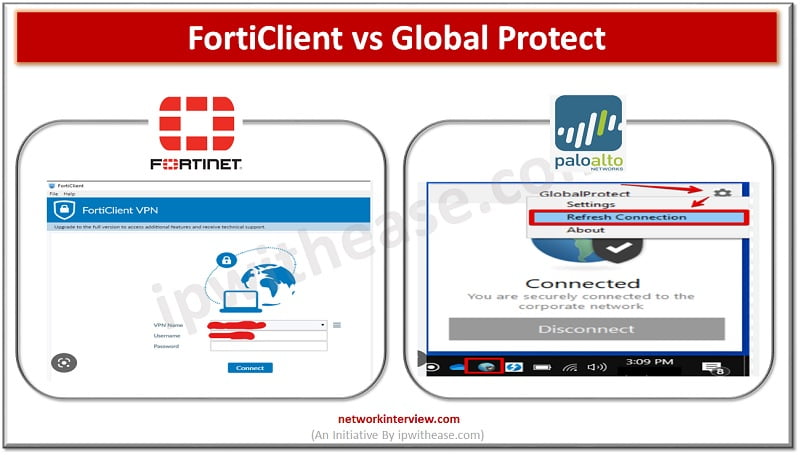
What is FortiClient? FortiClient is an app to provides UTM features like web filtering, giving web security and content-based filtering. FortiClient app is installed in the user’s system and tracks the traffic based on policy. The web application firewall offers malware …
Introduction to Firewall In todays digital scenario, where businesses demand agility and information are hosted on cloud infrastructure security of data is one of the primary concerns of business and protection of data from unwanted sources is the prime objective. …
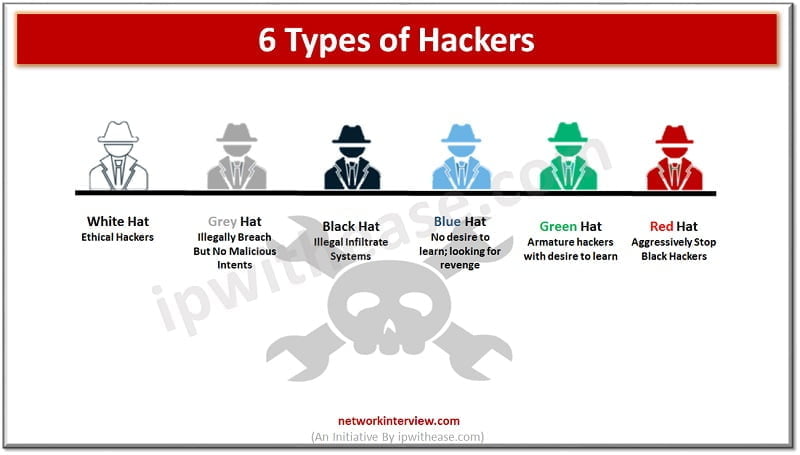
You must have heard the word ‘hacker’ multiple times in cybersecurity. The organizations have trained security staff to take care of cybersecurity threats. Hacking is generally referred to as someone gaining access to your network and systems by unauthorized means. …
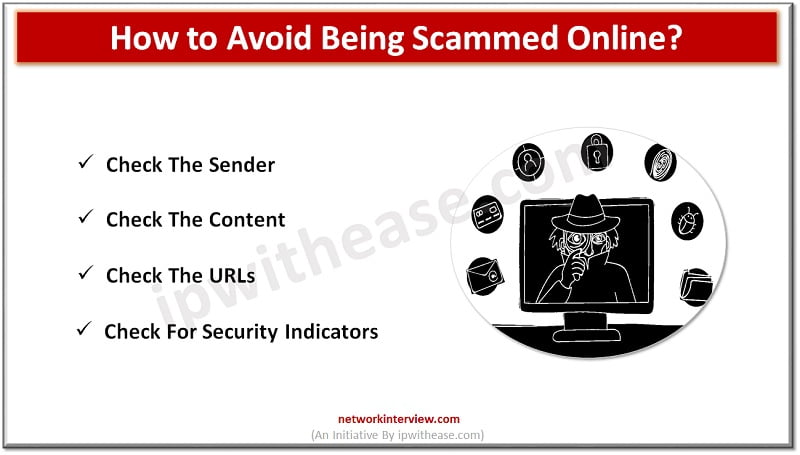
With the rise of technology and the internet, the world has become more connected than ever before. From online shopping to social media, we rely heavily on technology in our daily lives. While technology has made our lives easier, it …
Maintaining the security of your personal or business network and Internet connection is essential in today’s digital world. With the rise of sophisticated cyber threats, identity theft, and data breaches, protecting yourself from potential risks is becoming more critical than …
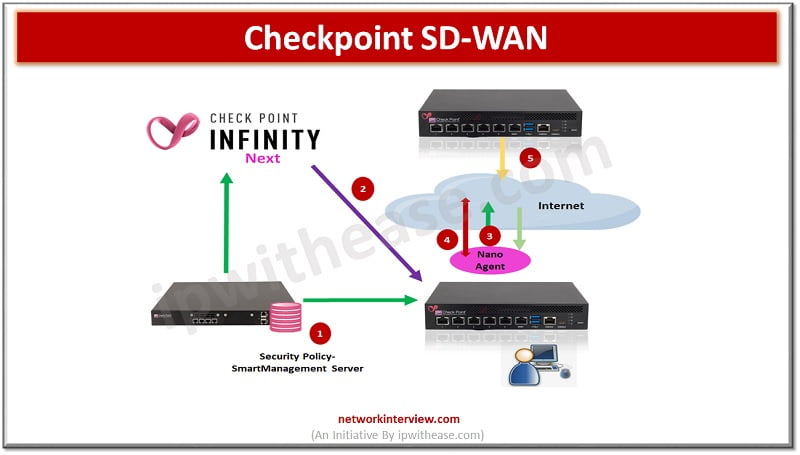
Note: This document is for those seekers who have prior knowledge of SD WAN and want to enhance SD WAN concept in Checkpoint perspective. This blog covers below topics of Checkpoint SD WAN: Quantum CheckpointSD-WAN concept Architecture Application basic traffic …
figure:1 As more and more systems are Internet facing due to high penetration of cloud and associates’ applications and services, the need for a very strong security system at perimeter or gateway to enterprises is becoming more and more crucial. …
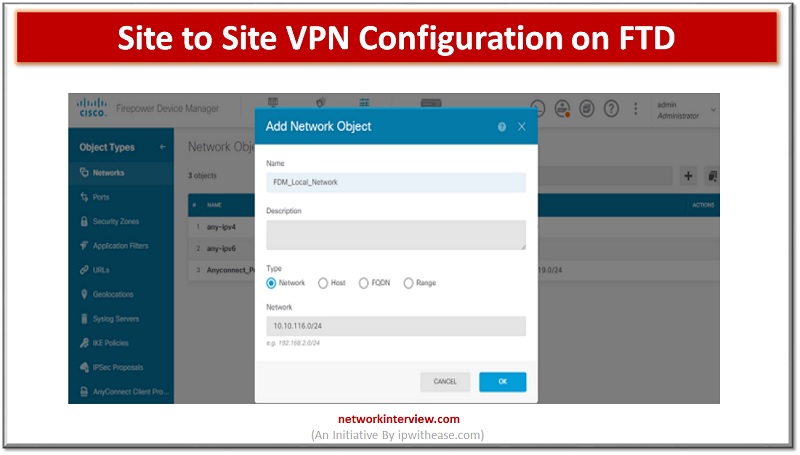
VPNs allow access to restricted sites with secure connection. In FirePower devices we can configure site to site VPN on FTD devices. The site to site VPN is configured for FTD devices using the FirePower Defence management console. In today’s …
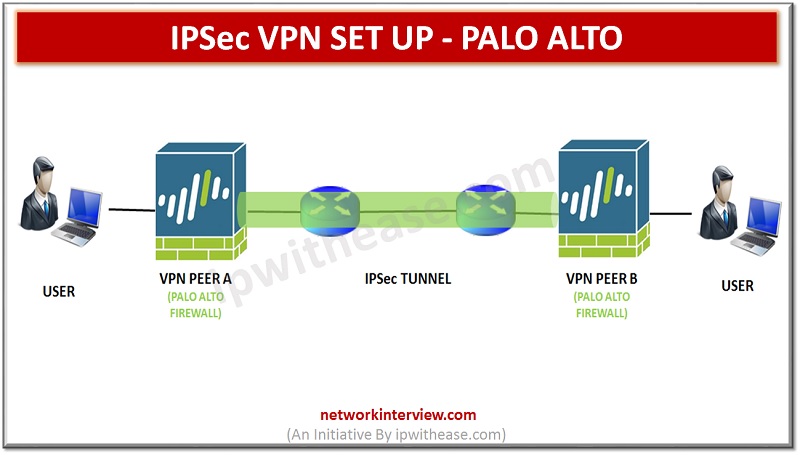
Site-to-Site VPN Overview A VPN connection that allows you to connect two Local Area Networks (LANs) securely is called a site-to-site VPN. Route based VPN can be configuring to connect Palo Alto Networks firewalls located at two sites or to …
Overview In our previous article, we studied IPSec VPN Set Up. In this article we will run through CLI commands and GUI steps to configure an IPSec VPN, including the tunnel and route configuration on a Palo Alto Networks firewall. …
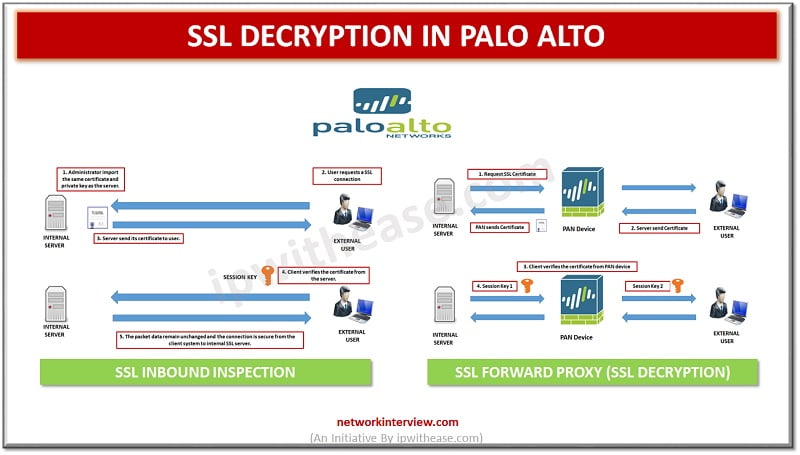
Before digging deep into Palo alto SSL Decryption, let’s first understand what is Decryption? What is Decryption? Palo Alto firewalls can be decrypt and inspect traffic to gain visibility of threats and to control protocols, certificate verification and failure handling. …
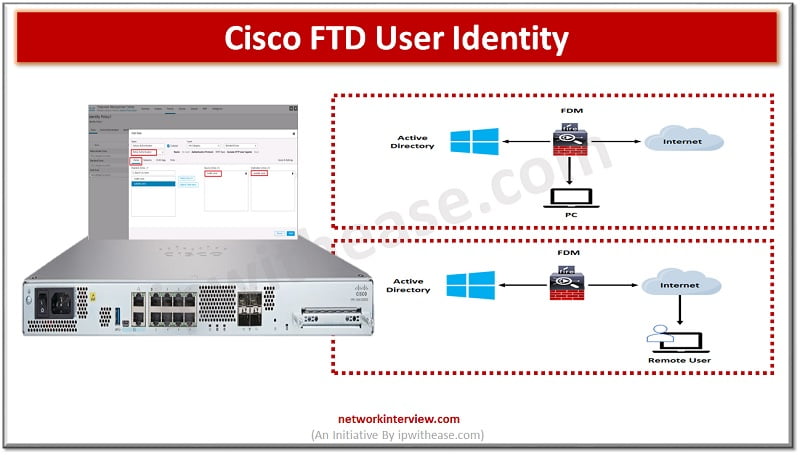
User identity information helps to identify the source of policy breaches, attacks or network vulnerabilities and trace them to specific users. Majority of traffic inspection products support filtering based on IP address. However, Cisco FTD identity policy feature gives the …
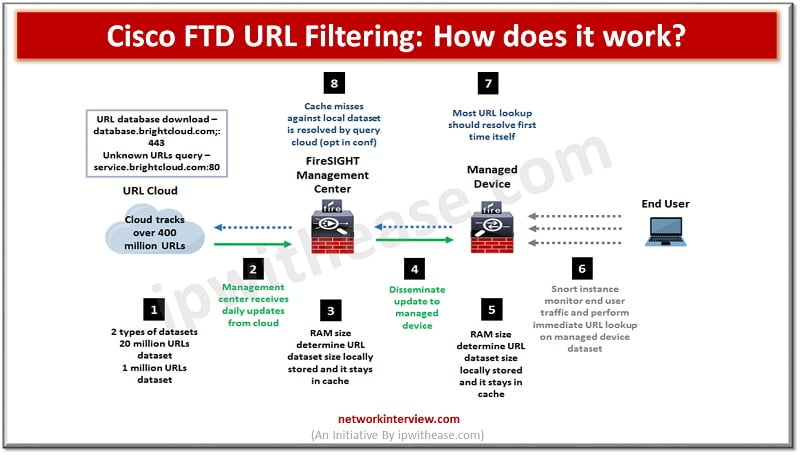
Pic: Showing How Cisco FTD URL Filtering works URL filtering or content filtering is one of the key features of firewalls. It helps to prevent access to harmful and malicious content which could cause data loss, system crash, virus or …
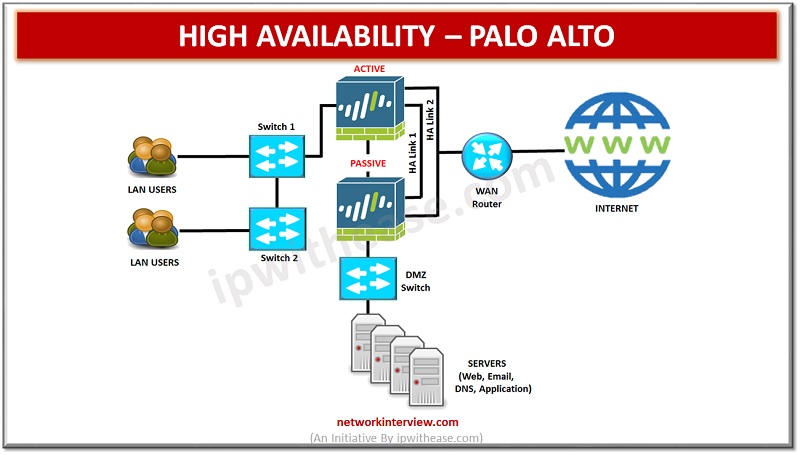
High availability (HA) refers to a system or component that is operational without interruption for long periods of time. High availability (HA) is measured as a percentage, with a 100% percent system indicating a service that experiences zero downtime. High …
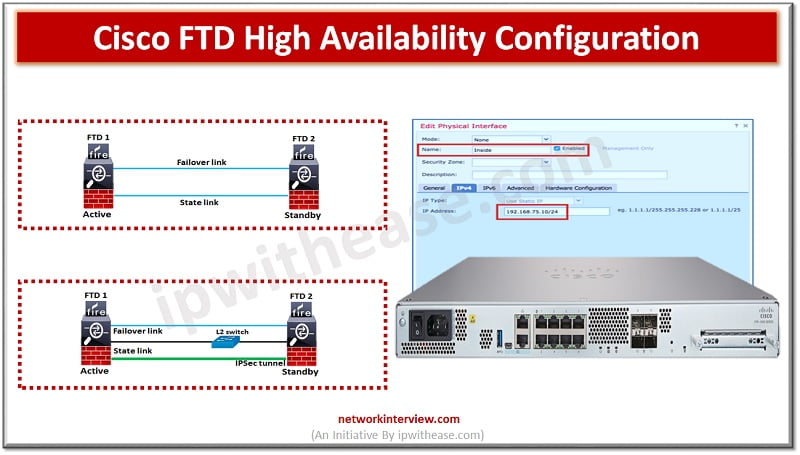
To ensure uptime and continuous availability in the event of disaster is a required key feature for any production environments be it servers, networks and other computing equipment. All Cisco devices majority support high availability (HA) also known as failover. …
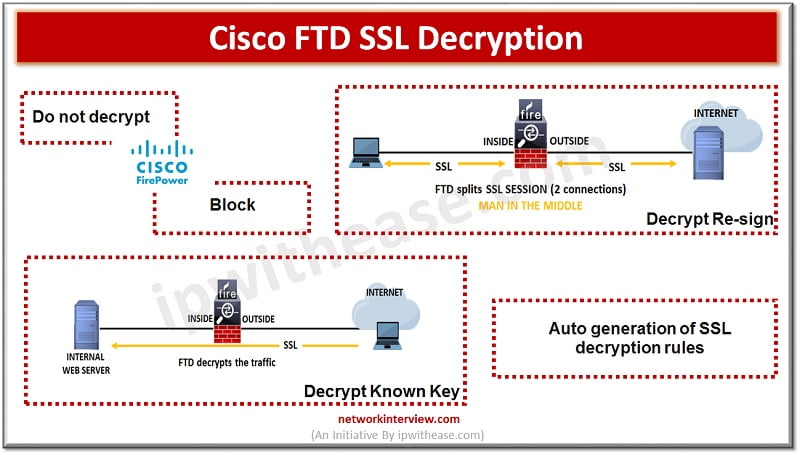
Some protocols like HTTPS use Secure socket layer (SSL), transport layer protocol (TLS) to encrypt traffic for secure transmissions. As the system cant inspect encrypted connections we first must decrypt to apply access roles which consider higher layer traffic characteristics …
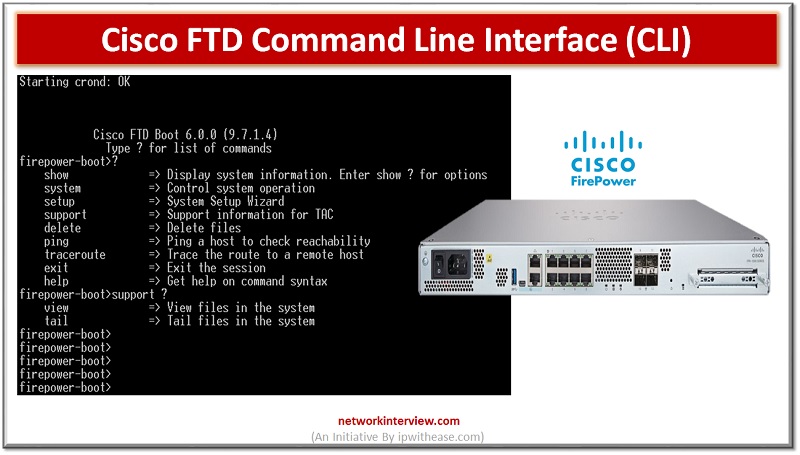
Majority of Cisco devices provide command line interface (CLI) as we call it to configure, manage and troubleshoot devices. Use of CLI allows users to execute Cisco IOS commands directly and simply as well as via remote access. In today’s …
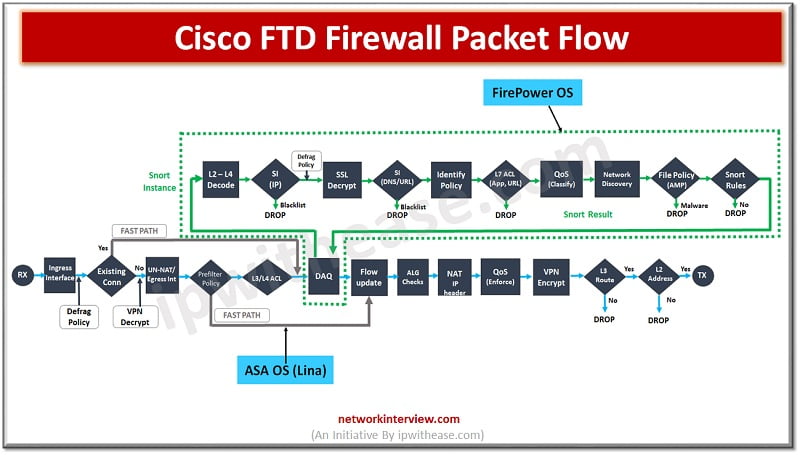
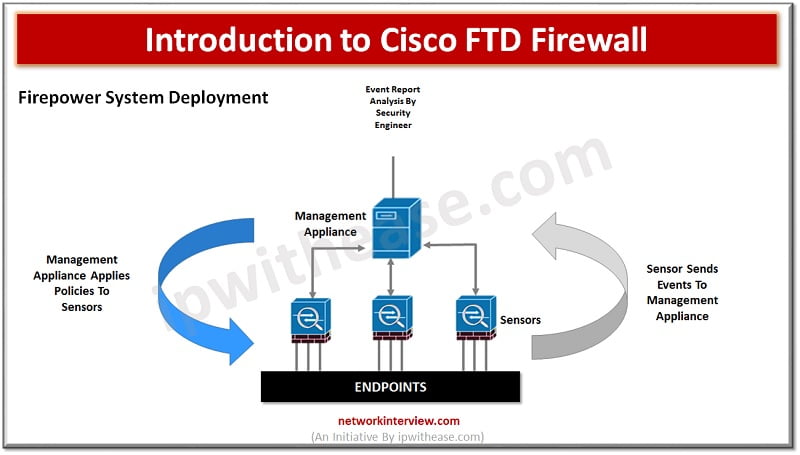
In the evaluation of next generation firewalls (NGFW), the next leap made by Cisco FTD is (Unified Firepower threat defence) software which includes not just NGFW but also Next generation Intrusion prevention systems (NGIP), Advanced Malware protection (AMP) and many …
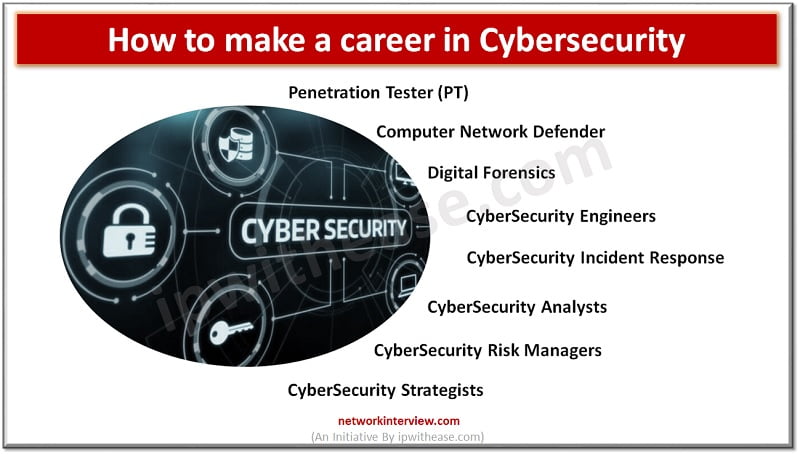
Career in Cybersecurity In this digital world, data is everywhere. This ensures that there are ample opportunities for people who have a passion for ethical hacking, known as “ethical hackers” to find jobs with companies that need their services. A …
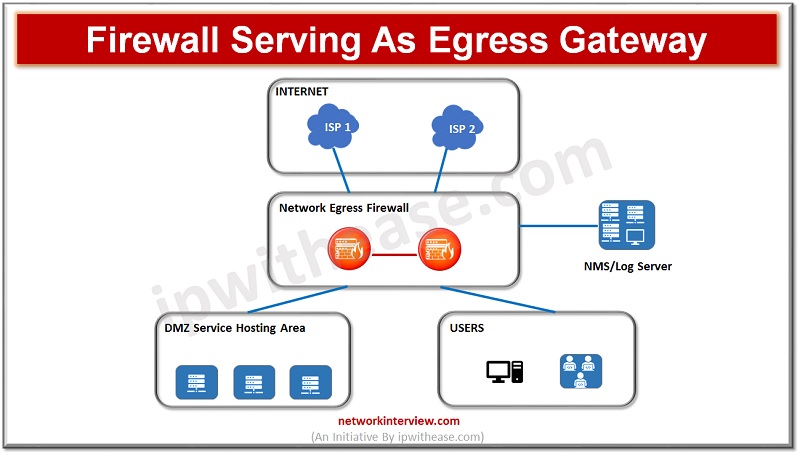
(Diagram depicting firewall acting as Egress Gateway) As enterprises are moving onto cloud their critical business applications, infrastructure services and use of hybrid clouds have evolved, secure networking is the demand of time along with performance and scalability of networks …