Content Filtering Model : Detailed Explanation
Overview
Content filtering is essential to exclude access to web pages or email deemed objectionable. Content filtering is used by corporations as part of their security framework setup. Content filtering service boosts network security by blocking entry to suspicious websites rather than just intercepting certain domain names. It can classify and assess web traffic to precisely identify threats with in a web page that shouldn’t be permitted into the internal network.
Blacklist websites for e.g. block the web or Internet Communications category, this blocks gmail.com and facebook.com because both websites are communication platforms. Content filtering performs at Application layer of OSI model and actually examines content of data. Blocked website categories are as follows:
- URL category list
- Web search filtering
- Restricted YouTube content
- Blocked URL patterns
- Whitelisted URL patterns
Features of Content Filtering
- Content Filtering protects users from malware, adware, spyware, and phishing.
- Content Filtering protects critical network infrastructure from web-based threats.
- Content Filtering is ideal for small and medium-sized businesses, enterprise branch offices, and schools.
- All other security features, such as VPN, firewall, and intrusion prevention, can be configured with Content Filtering.
- A firewall is designed to filter content and provides protection from malicious Websites.
- Content Filtering uses Cisco Umbrella for network security that provides the defense against threats on the Internet. It acts as a gateway between the Internet and your systems and data to block malware, botnets, and phishing over any port, protocol, or application.
- No Standard memory required to implement filtering.
Related – VPN Top 100 Interview Questions
Filtering using ACL
Cisco IOS supports URL filtering. Drawback of using extended ACLs or may be CBAC inspection with Java blocking is that your router filters traffic only supported what is in either the ACL or the inspection statement. In case to prevent users from accessing pornography, gambling, and peer-to-peer file-sharing sites, you would have to know about the IP address of every web page (not just every website). Unfortunately, you cannot screen web pages with normal extended ACLs? Since it can only work till Layer 4 and lower information. Even if you decide to block all pages from these web servers, you easily would have tens of thousands of ACL entries to create and maintain. ACLs typically are not used to implement these kinds of policies. Instead, a content-filtering server is used. Cisco supports filtering with product like CISCO Umbrella to perform this filtering process. Actually, the content-filtering servers contain the access policies and your Cisco router uses these external policies to enforce URL access.
Operation of URL Filtering with Content Filtering Server
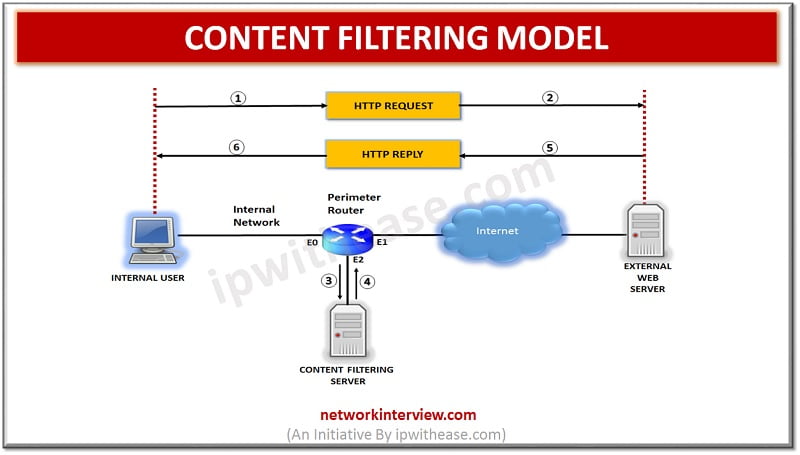
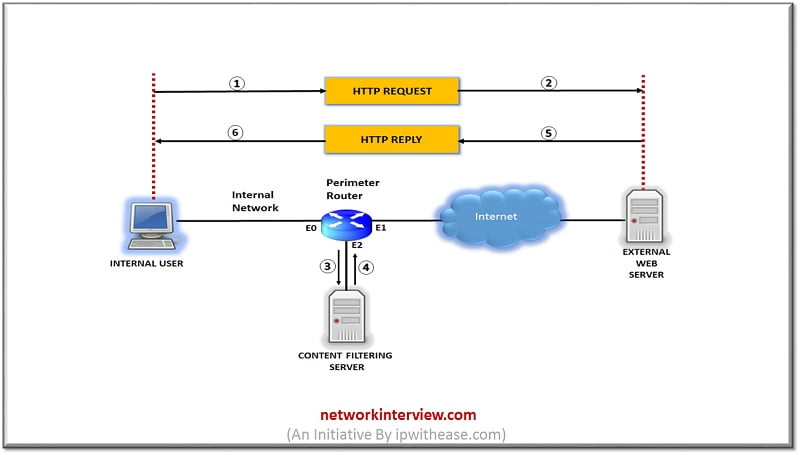
To help you understand how URL filtering works, take a glance at an easy example.
URL Filtering Process
In this example, an internal user sends an HTTP request to download information from an external web server. Here are the steps:-
- The user sends the request, and the router examines it.
- The router forwards the request to the external server.
- The router also sends a copy of packet to the content-filtering server to determine whether the access is allowed. Basically, Steps 2 and 3 are occurring almost simultaneously.
- When the content-filtering server receives the lookup request, it processes its internal database policies to determine the action that the router should take. It then sends the policy action to the router.
- The response from the content-filtering server arrives before the external web server has a chance to return the content that the user was asking for the router can buffer the returning external web data.
- Deny and permit action decided by as per policy of Content filtering server.
Router permits outgoing traffic towards external web server generated from user instead of first verifying the content. When reply from external web server reaches the router, then it takes action as per policy created on content filtering server.
It is notable that URL filtering places a very high burden on our router’s processing. Therefore, we should be careful about implementing this on router. This will kill router.
Related – URL Filtering vs Content Filtering
Advantages of URL Filtering
- CISCO Umbrella provides 80 categories to filter content based on types of access, such as sports, pornography, gaming, politics, gambling, religion, and other groupings of information.
- We can keep a detailed log on CISCO Umbrella content server of who is accessing what resources.
- We can define policies on a per-host or a per-user basis, providing more control over access policies.
- We can advertise multiple content filtering servers on our router to provide redundancy.
- To speed up lookup requests, the router supports an IP cache table that contains a list of IP addresses of web servers that are allowed access by all internal users.
- The Cisco IOS can buffer up to 200 simultaneous HTTP requests.
Conclusion
Content filtering provides protection from Internet based threats and corporate network security and recognizes the organization policies of blacklisting specific categories.
Continue Reading:
URL Filtering vs Content Filtering
Tag:comparison



