What is Micro Segmentation?
Network security is of paramount importance. Organizations invest the majority of their resources in security of their networks from external attacks using firewalls and intrusion prevention systems; however if a breach occurs in this system, intruders will have access to all information of entire data systems. Hackers who gain internal access to a system can access entire data systems and can initiate man in a middle attack and can access the payment and personal information of millions of users. Network isolation to contain such attacks is an effective strategy in such scenarios.
In this article we will learn more about Micro Segmentation technology , how it works and its advantages etc.
About Micro Segmentation
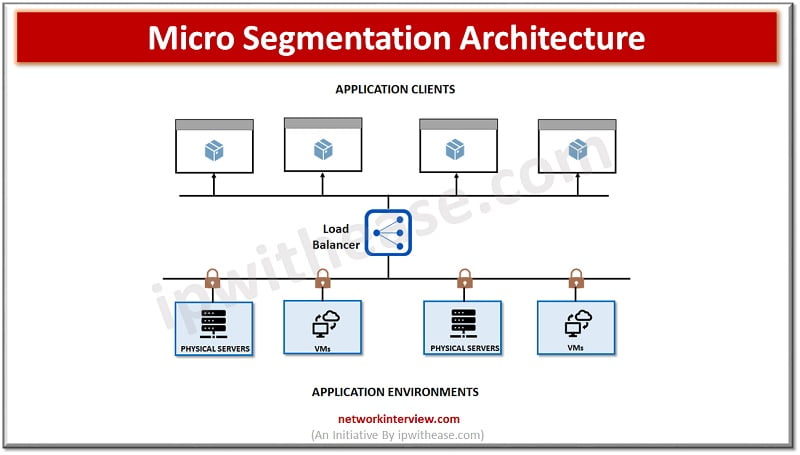
Micro Segmentation lets logical segregation of workloads and data centres by implementation of granular segmentation policies. Micro Segmentation is different from network segmentation, and is optimal for increasing security for server-to-server traffic which is there in the data center. As companies are using more and more data , the amount of internal server to server traffic is increasing and becoming more and more vital for day-to-day functioning of businesses. Security of this traffic is crucial.
Micro Segmentation Implementation
Implementation of Micro Segmentation vary depending on the situation. In organizations where security is of prime importance more zones of controls are implemented to provide additional protection. Such as in case of financial organizations or hospitals where regulated information gets created and requires heightened security. Users and devices both need to be segmented here to protect the network from external threats such as phishing emails.
Systems should be segmented based on their purposes – there could be networks dedicated only to IoT devices. Network segmented do happen based on the permissions or purposes of devices within them. Conducting a security risk assessment of network and devices help to prepare comprehensive strategy to perform segmentation.
Pros and Cons of Micro Segmentation
- Traffic security is enhanced as Micro Segmentation allows traffic between servers to be more secure via implementation of granular policies and logical division of networks
- Attack surface reduction is achieved with adoption of policies that close gaps which are created by data extensions over cloud
- Zero trust networks operates on principle of networks which never trust anything inside or outside of its confines and always verify every system attempting to connect to network
- Improved compliance is achieved by enhancing compliance with government regulations as network processing relevant data in secured and isolated environments
- Quality of security policies – management of security policies and access control lists across segments of data is a challenging task to manage and maintain
- Expense – can be expensive , depending on how granular management is required and number of policies implemented and security inspections conducted
- Performance degradation – additional gateway creation for Micro Segmentation would result in bottlenecks between segments which causes reduction in system performance
Conclusion
There are several vendors available in market which offer Micro segmentation such as AWS, Microsoft and VMware. Micro segmentation was designed to offer better security at granular level and applies security policies to traffic between all groups and offers a refined policy control implementation to restrict lateral movement of attacks on the network surface.
Technological advancements, increased use of applications, variety of devices such as mobiles along with increasing rate of cyber attacks are all contributing to the growth of Micro segmentation a market which is predicted to grow over 20% over next three years by Xtravit prediction.
Continue Reading:
Micro segmentation vs Network Segmentation
Microsegmentation vs Zero Trust
Tag:Security