Introduction to Sonicwall Firewall: Working, Features, Setup
Evolution of Firewalls: Sonicwall Firewall
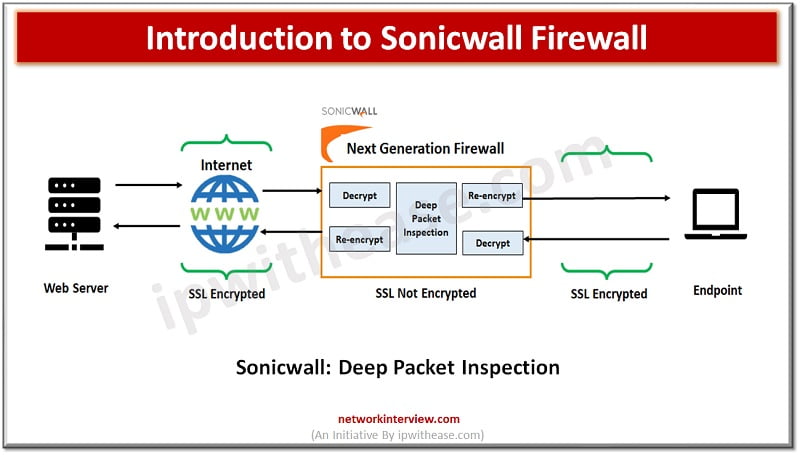
Firewall technologies have evolved at a very rapid pace since its inception and from initial packet filtering firewalls which use to inspect packet traffic and took decision to allow or reject packets, which is then replaced with stateful packet inspection files which were designed to protect network layer threats by analyzing ports and protocols. Then Next generation firewalls came which were deep packet inspection firewalls to scan the entire packet payload in order to provide advanced threat protection.
In today’s topic we will look at Sonicwall firewalls which are Next Generation firewalls (NGFW), their architecture and features.
What is a Sonicwall Firewall?
Sonic firewall which was earlier called by name ‘Interpol’ in the late 1990s rebranded as Sonic firewall a dedicated hardware appliance with firewall and VPN software intended for the small business segment. Sonic firewalls enable to identify and control all applications which are running in the network.
It identified applications based on their unique signatures instead of protocols or ports. It visualizes application traffic to determine usage patterns and develop granular policies for applications, users, or user groups and other parameters such as time of the day etc.
Working of Sonicwall Firewall
Sonicwall application recognition is based on their ‘DNA’ instead of less unique attributes such as source port, destination port, protocol type based on an extensive, automatically updated database of application signatures. SSL encrypted traffic-based controls analyze the encrypted traffic the same way as unencrypted traffic.
Sonicwall firewall controls to track and manage and enforce specific versions of applications being used. There is no need for a physical check on every system to determine the version of application but simply set a Sonicwall application intelligence and control policy to achieve this.
You can create a policy to prioritize bandwidth for live meeting applications, the deep packet inspection engine will search for application signature or name and increase the bandwidth on priority for live meeting application.
Peer-to-peer applications like BitTorrent, often utilized for downloading unauthorized copies of copyrighted content, not only take up bandwidth but also pose a significant risk for transmitting malware. New P2P applications are constantly being created and it makes it difficult to manually block any single P2P application. The Sonicwall application intelligence and regulated databases receive regular updates to incorporate newly emerging P2P applications.
Social networking sites such as Facebook, Instagram, and YouTube can be blocked or restricted only to specific users at the workplace.
Sonicwall capture enhances firewall threat prevention capabilities by detection and prevention of unknown and zero day attacks via cloud.
Data leakage can be prevented with outbound traffic routed through a firewall and it can detect and prevent ‘data-inmotion’.
Features of Sonicwall Firewall
- Single configuration for management of all threats
- Single UI interface to view and manage all threat events so there is no need to separately look at log entries on multiple devices such as firewalls, Antivirus, web content filtering, Intrusion prevention systems and data leakage prevention systems
- Improved control over applications by category, bandwidth management, user access, destination control etc.
- Gives a single view of network security
- Easy to manage and secure VPN systems for secure remote access
How to set up a Sonicwall firewall?
- Connect a system to Sonicwall LAN (X0) interface or a network switch connected to LAN interface. It will automatically receive an IP address from Sonicwall appliance.
- Open a web browser to https://192.168.168.168 to access firewall
- While accessing first time it gives option to use a setup wizard or go directly to management interface
- At sonic wall management interface login page, the default admin and password is: admin/password
- The default password is to be changed
- Select a timezone from ‘time zone’ drop down and click ok.
- At WAN network mode page select the option cable/mode-based connections for DHCP assigned IP addresses
- Select option Router-based connections for static IP address and netmask
- At LAN setting page accept the LAN settings default or enter IP address and netmask and click next
- At Sonic wall configuration summary page review the configuration and click Apply
- In SonicOS click Monitor and then current status | system status
- To register click on register links which takes you to license page
- Enter your MySonicwall username, password at this page and click on submit
Quick fact!
Market share: Sonic firewall (0.4%) in network security space.
Continue Reading:
Perimeter Firewall vs Internal Firewall: Detailed Comparison



