Palo Alto vs Fortinet Firewall: Detailed Comparison
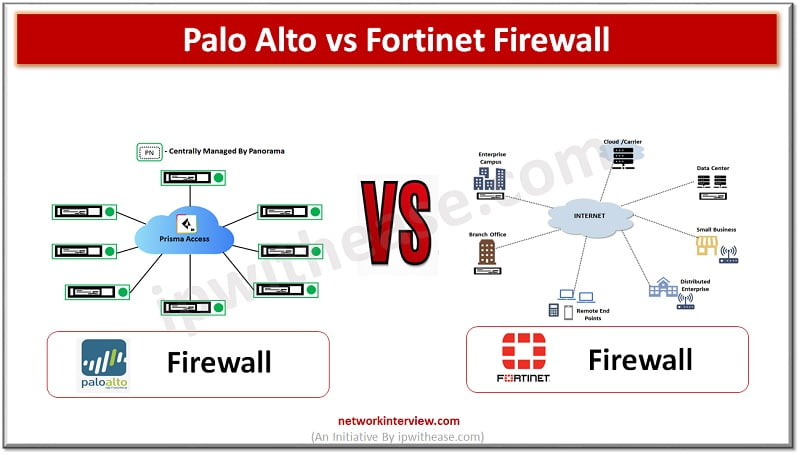
(Diagram depicting Palo Alto vs Fortinet Firewall)
Organizations need to keep pace with rapid increase in technology demands such as remote working, anywhere connectivity, lower latency , increased availability along with protection of infrastructure from a never ending list of threats and vulnerabilities. The firewalls are a crucial security product which provides capabilities to protect your networks and data residing within. Moving from stateful network firewalls to next generation firewalls is a game changer.
A traditional firewall approach based on filtering incoming and outgoing traffic based upon Internet protocol (IP) port and IP addresses is replaced by next generation firewalls which provide add-on features like application control, intrusion prevention (IPS), URL filtering and advanced threat protection capabilities like sandboxing.
Today we look more in detail about two most popular companies’ firewalls : Palo Alto vs Fortinet Firewall, key differences, features etc.
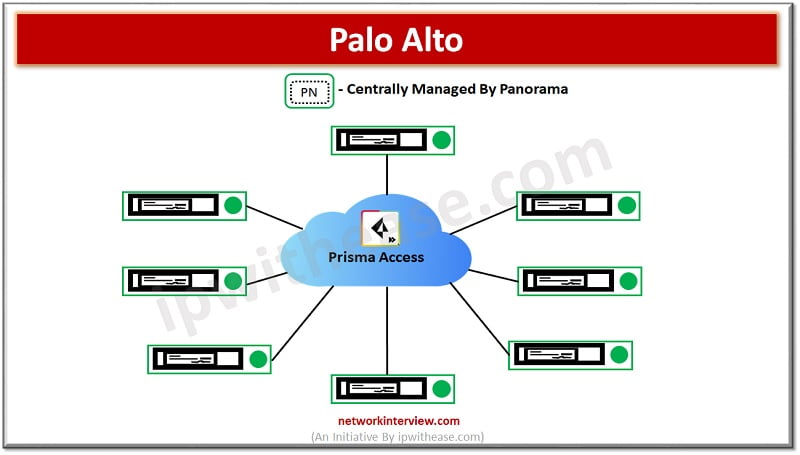
About Palo Alto Firewall
Palo Alto is a global cyber security company based out of Santa Clara, it’s one of the core security products in cloud-based security offering is Palo Alto used by 85000 customers across 150+ countries. It has both physical and VM series firewalls – the PA-220, PA-800, PA-3200 series and PA-5200 series are next generation hardware while PA-7050 and PA-7080 are chassis-based architecture.
Release of PAN OS 9.0 new K2 series firewalls were introduced which was a 5G ready firewall designed for service provider mobile network deployments having 5G and IoT security needs. The VM series firewalls can be deployed in on premises or cloud environments. They use a unified licensing system which is platform agnostic.
Features of Palo Alto Firewall
- License bundles antivirus, antispyware, and vulnerability protection . Threat prevention allows to obtain content updates for malware protection
- Able to create a copy of decrypted traffic from firewall and send it to traffic collection tool for archiving and analysis
- Ability to control access to websites based on category of URLs
- Receive antivirus signatures updates which include signatures discovery by wildfire
- Special license for provision of extended VPN remote access connectivity which has multiple gateway usage, mobile apps, mobile security management, host information checks or internal gateway
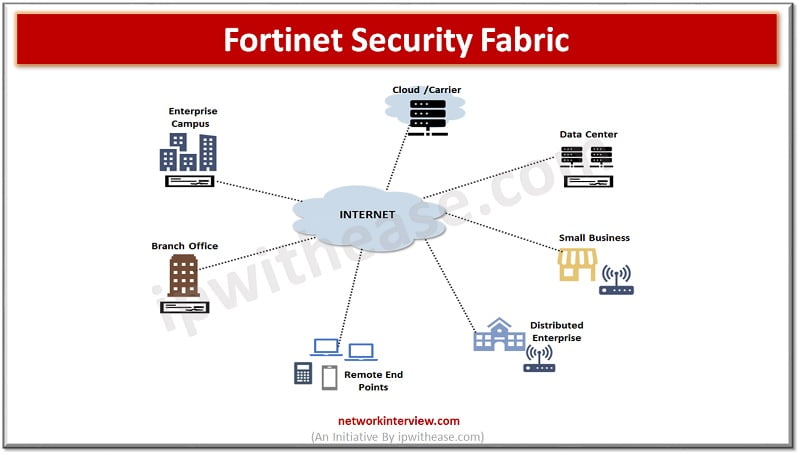
About Fortinet Firewall
Fortinet was founded in 2000 by brothers Ken Xie and Michael Xie as a cybersecurity company. The name of Fortinet firewall is derived from the phrase ‘Fortified networks’. FortiOS is an operating system for hardware which is the base of security fabric.
Majority of Fortinet models use specialized accelerated hardware known as security processing units which can offload resource intensive processing from main processing resources. Having specialized content processors which accelerate a wide range of essential security functions such as virus scanning, attack detection, encryption, and decryption.
Features of Fortinet Firewall
- Understand application layer protocols and applications
- Gives ability to block access to malicious, hacked, or inappropriate websites
- Protects against viruses, spyware, and content level threats
- Performs dynamic analysis to identify unknown malware with automatic response and detection in the cloud
- Provides protection against threats on mobile devices by using detection engines to prevent both new and evolving threats to gain access to network and also personal information
- Aggregates malicious source IP list
- Controls access to risky industrial protocols
- Protection0 against spam at network perimeter, controls email attacks and infections
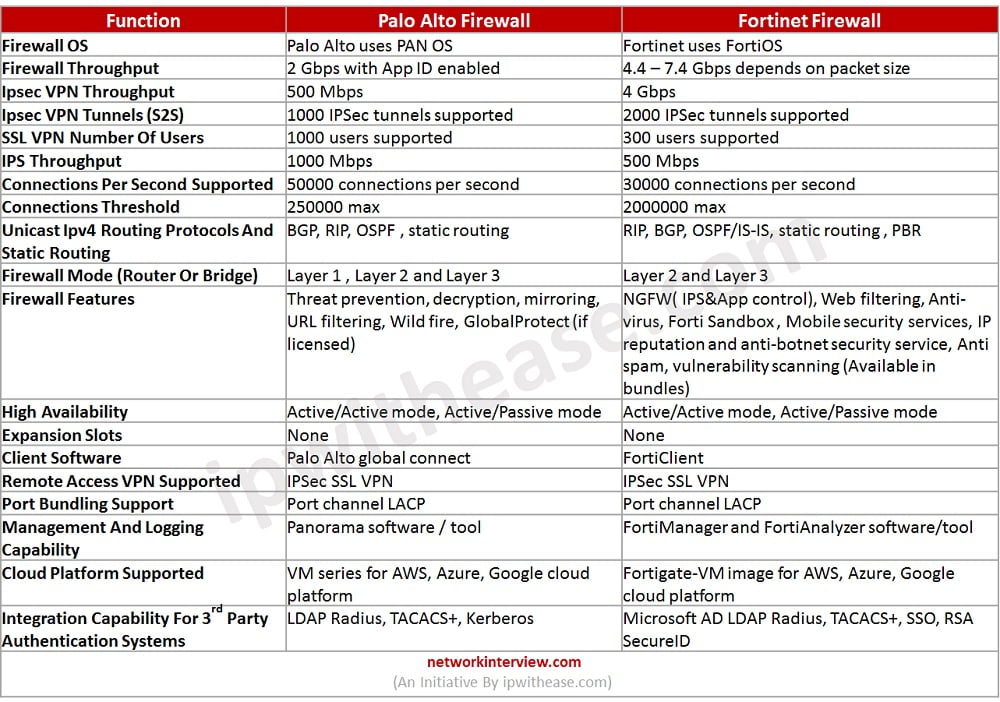
Comparison Table: Palo Alto vs Fortinet firewall
Below table summarizes the key points of differences between the two types of firewalls:
Download the comparison table: palo alto vs fortinet firewall
Continue Reading:
Palo Alto Firewall Architecture
Routing Configuration in FortiGate Firewall: Static, Dynamic & Policy Based
If you want to learn more about Palo Alto, then check our e-book on Palo Alto Interview Questions & Answers in easy to understand PDF Format explained with relevant Diagrams (where required) for better ease of understanding.
Tag:comparison, Fortigate, PaloAlto, Security