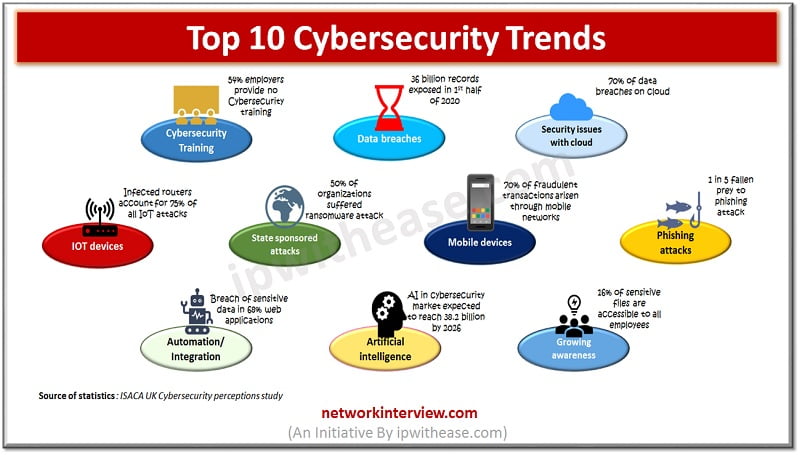
Top 10 Cybersecurity trends for 2026
Cybersecurity Trends
With more and more digital advancement and penetration of cloud organizations are very much concerned about the cybersecurity threats which are on high rise and have an upward trend. Emerging technologies such as cloud computing, Artificial intelligence (AI), Automation and Internet of things (IOT) are creating ample opportunities for businesses to unlock its true potential and value. But as the technology advancements are happening so do the Cybersecurity threat landscape is expanding at a rapid pace.
In this article we will look at some cybersecurity trends which made their place in top 10 and shaped the security landscape. These trends may raise from data breaches to, lack of sufficient skilled IT staff, data privacy concerns on cloud and so on.
Top 10 – Cybersecurity Trends
Data breaches
It continued to be the topmost cybersecurity concern and will continue to remain in this position due to its attractiveness to the black market. Data privacy and security of personal data is in top of the mind of organizations, with the more stringent privacy legislations such as European Union ‘General Data Protection Regulation (GDPR)’ regulation organizations are more concerned about the negative consequences of data breaches and its impact on their brand image apart from financial implications in terms of fines and penalties. Web applications are leading source of data breaches hence ensuring web applications security is a major concern for organizations.
Cybersecurity skills paucity
Two third of world organizations are reporting lack of skilled staff to handle cybersecurity related incidents. There is a need for an automation vulnerability management solution to maintain good security posture and even with smaller teams effectively securing websites and web applications.
Security issues with cloud
With inhouse IT infrastructure migrating to cloud a new outlook is required to look at new approach to Cybersecurity. Cloud based threats are growing and organizations are struggling to maintain control over sensitive data. Manual management of security is not a good practise for large web application infrastructures and leading to creation of misconfigured data buckets which are potential source of high risk.
Automation and Integration in Cybersecurity
The demand is to do more with less and automation and integration across multiple applications making it difficult to secure. Fast pace of the requirement leading to ignoring quality of development and time required to creating a secure web applications.
Growing awareness for Cybersecurity
The growing awareness for cybersecurity among organizations, big or small is catching up fast. Businesses now realize the importance of a good cybersecurity strategy and it is no longer considered a necessity and not an extravagance.
Information security trainings and awareness is become a regular stuff to improve cyber hygiene among the employees and maintain a strong security posture on all levels of the organization. Even in software development lifecycle at all stage’s security is integrated and its impact is assessed to build/develop secure applications with SecDevOps/DevSecOps processes.
Mobile devices major Cybersecurity risks contributors
With exponential growth of mobile devices, more and more data storage is happening on mobile devices. The impact of mobile malware is relatively low but number of data breaches related to mobile devices and misuse is on rise. Every device connecting to company network is another endpoint which needs to be secured via a web based secure application infrastructure.
State sponsored Cybersecurity attacks on rise
Persistent threats sponsored by nation state actors are on rise and now part of global security threat landscape. Unofficially supported cyber criminals by states launch DDoS attacks causing high profile data breaches, steal political and industrial secrets, spread misinformation, impact global opinion and events and quite honest voices.
As political influences grow maintenance of security to handle globally spread attackers and deploy advanced solutions to detect and eliminate known and emerging threats which can destabilize the political stature of the countries.
IOT devices risks
A wealth of security blunders has brought by booming IOT (Internet of Things) devices due to rapid need to deploy new products and technologies giving seldom thought to security. Hard coding of credentials, insecure wireless communications, unencrypted sensitive information, non-verified firmware updates and vulnerable web interfaces are some common practices which are overlooked leading to compromised IOT devices such as routers, switches, and NAS servers which provide access to data and communications and serve as weak entry points to hackers.
AI on both sides of Hurdle
Artificial intelligence (AI) on side with its machine learning capabilities helping businesses to perform functions in a more effective way at the other side cyber criminals are using AI to develop more sophisticated malware and attack strategies. The need of hour is for organizations to use advanced heuristic solutions instead of simply deploying vulnerability tools which can detect known vulnerabilities and attack signatures.
Phishing threats
These are the most effective means of stealing identities, credentials, distribution of malware, fraudulent payments, Cryptojacking and so on. Ransome ware attacks are on rise. Effective protection is required not just by enablement of Cybersecurity training for employees and business partner firms, but also in-depth security and vulnerability management is the need of the hour to prevent attackers from gaining access to confidential information used in phishing attacks. (Related: Whaling Phishing Attack)
Continue Reading:
Top 10 trends in Automation Testing Tools
Top 10 Networking technology trends
Tag:Security



