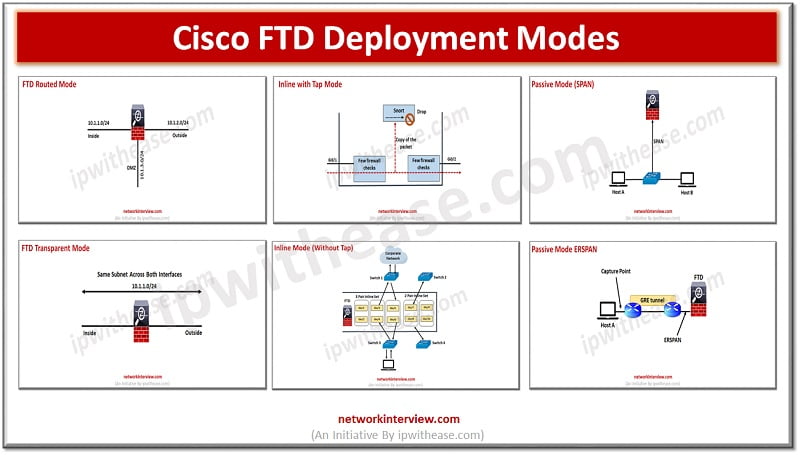
(FTD Deployment Modes: Routed, Transparent, Inline, Inline with tap, Passive SPAN, Passive ERSPAN) Cisco FTD design and deployment implementation involves setting up firewall, SSL inspection, NAT, IPS and active/standby HA. Deployment model determines placement of FirePower into the network as …
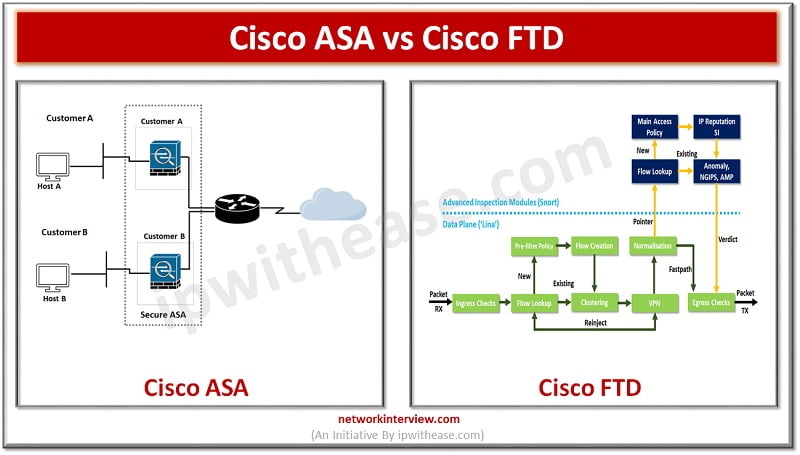
The Cisco Firepower Threat Defense (FTD) and Cisco Adaptive Security Appliance (ASA) are two types of security appliances that provide various features and capabilities to companies. These appliances were created with the intention of safeguarding businesses from cyber threats. Today …
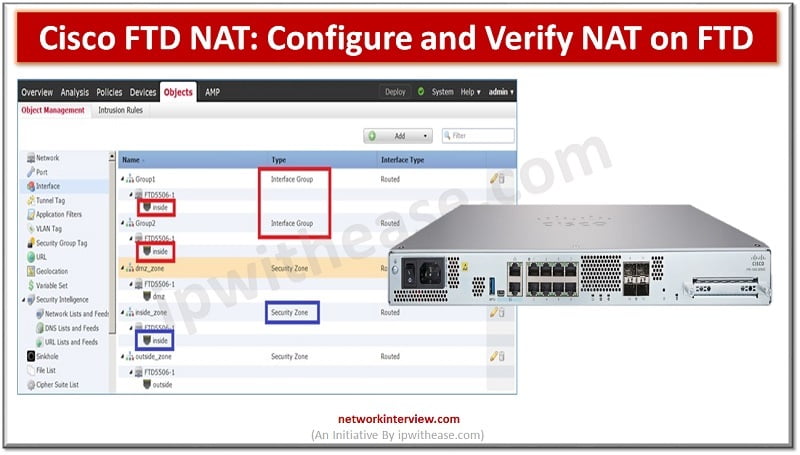
Cisco FTD NAT: Introduction An IP address is the basis of every communication over the network and Internet. Each computer device is assigned an IP address within an IP network which identifies the host as a unique entity. But due …
figure:1 As more and more systems are Internet facing due to high penetration of cloud and associates’ applications and services, the need for a very strong security system at perimeter or gateway to enterprises is becoming more and more crucial. …
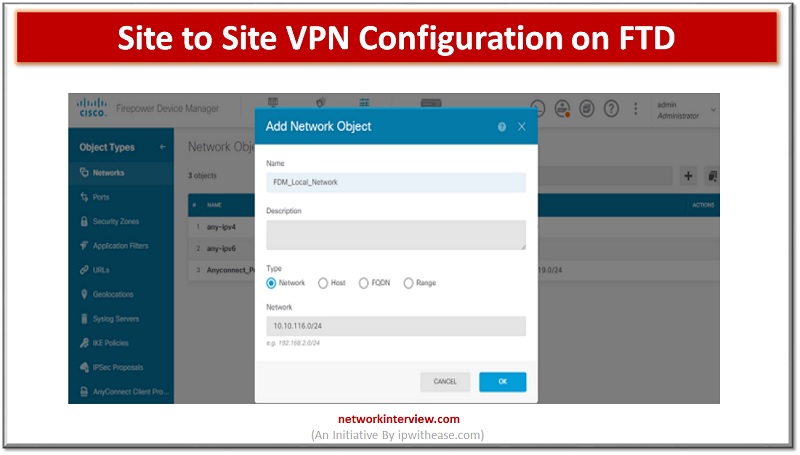
VPNs allow access to restricted sites with secure connection. In FirePower devices we can configure site to site VPN on FTD devices. The site to site VPN is configured for FTD devices using the FirePower Defence management console. In today’s …
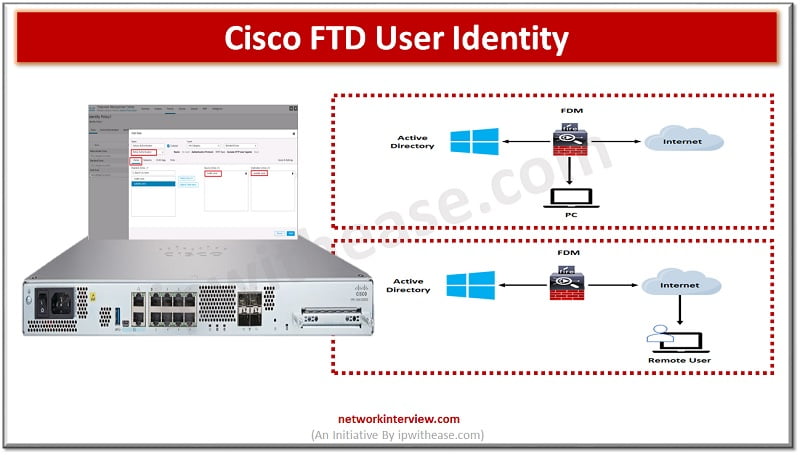
User identity information helps to identify the source of policy breaches, attacks or network vulnerabilities and trace them to specific users. Majority of traffic inspection products support filtering based on IP address. However, Cisco FTD identity policy feature gives the …
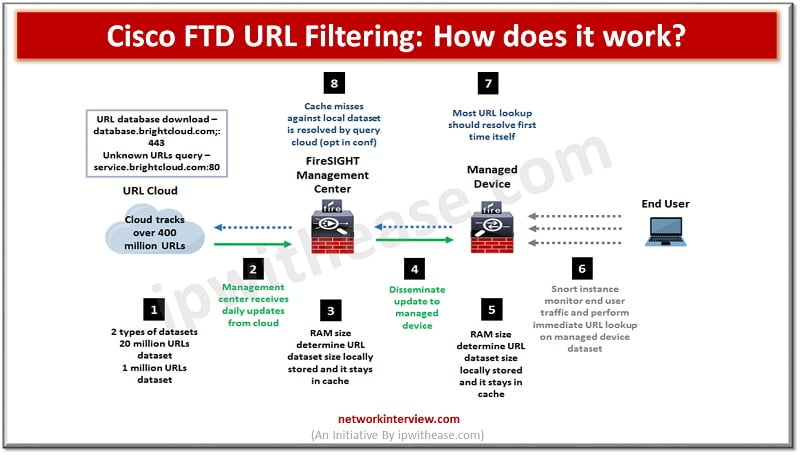
Pic: Showing How Cisco FTD URL Filtering works URL filtering or content filtering is one of the key features of firewalls. It helps to prevent access to harmful and malicious content which could cause data loss, system crash, virus or …
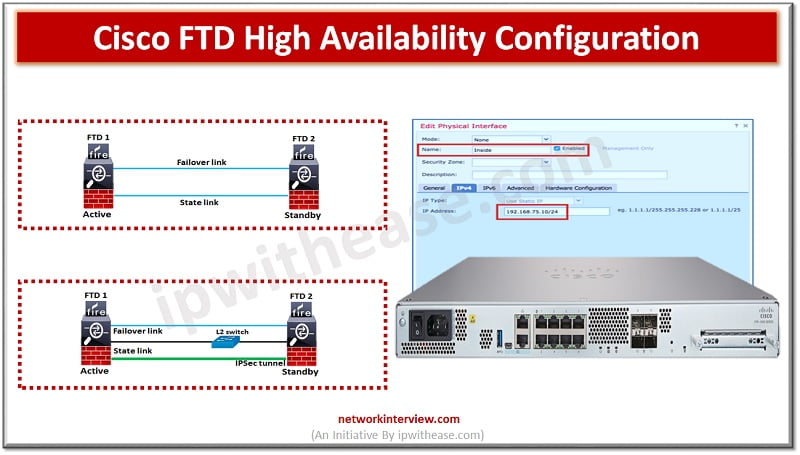
To ensure uptime and continuous availability in the event of disaster is a required key feature for any production environments be it servers, networks and other computing equipment. All Cisco devices majority support high availability (HA) also known as failover. …
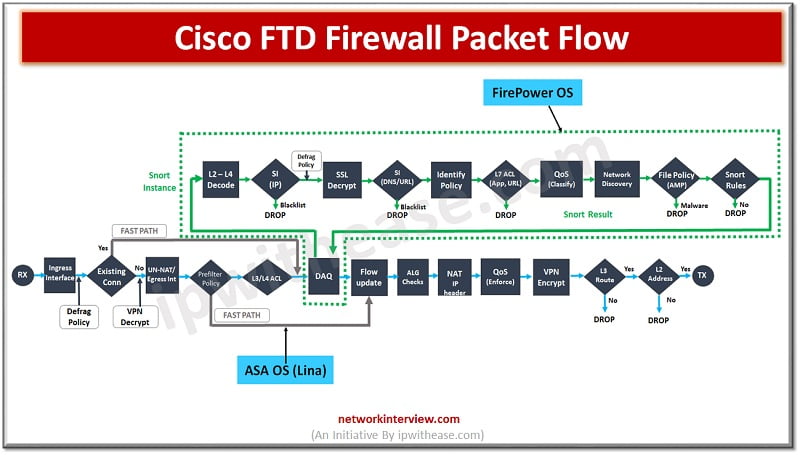
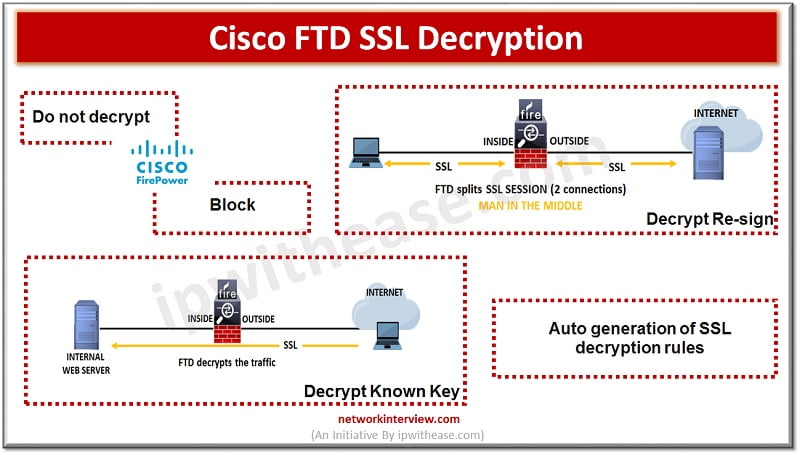
Some protocols like HTTPS use Secure socket layer (SSL), transport layer protocol (TLS) to encrypt traffic for secure transmissions. As the system cant inspect encrypted connections we first must decrypt to apply access roles which consider higher layer traffic characteristics …
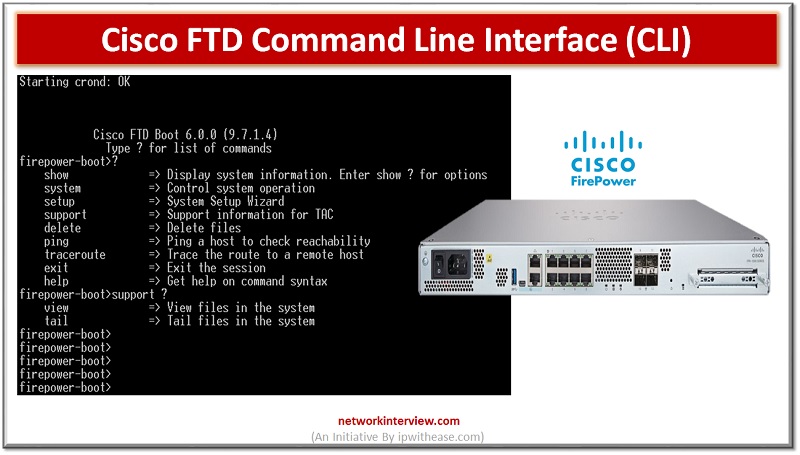
Majority of Cisco devices provide command line interface (CLI) as we call it to configure, manage and troubleshoot devices. Use of CLI allows users to execute Cisco IOS commands directly and simply as well as via remote access. In today’s …
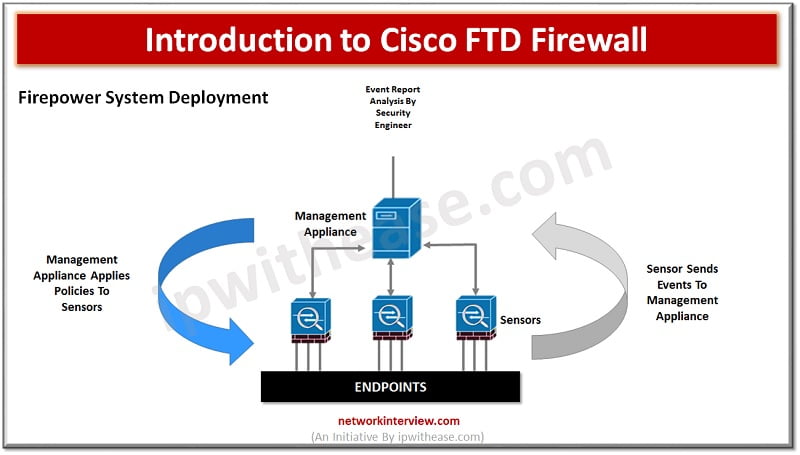
In the evaluation of next generation firewalls (NGFW), the next leap made by Cisco FTD is (Unified Firepower threat defence) software which includes not just NGFW but also Next generation Intrusion prevention systems (NGIP), Advanced Malware protection (AMP) and many …