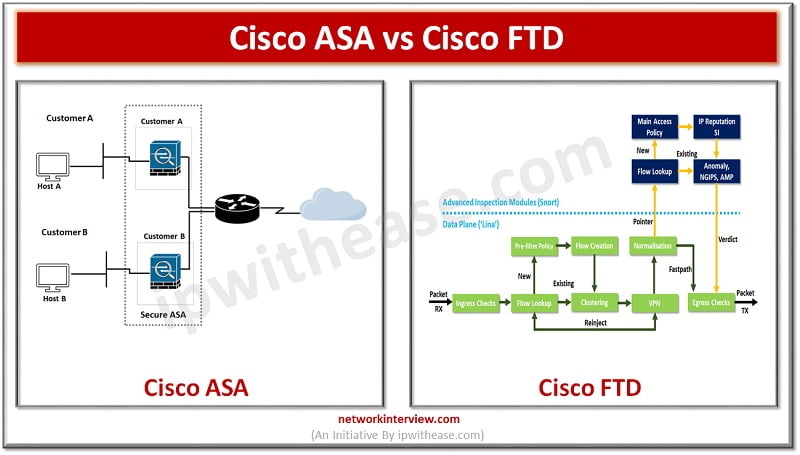
Cisco ASA vs Cisco FTD: What is the difference between Cisco ASA & Cisco FTD
The Cisco Firepower Threat Defense (FTD) and Cisco Adaptive Security Appliance (ASA) are two types of security appliances that provide various features and capabilities to companies. These appliances were created with the intention of safeguarding businesses from cyber threats.
Today we look more in detail about their features, use cases and comparison Cisco ASA vs Cisco FTD, i.e. how they are different from each other.
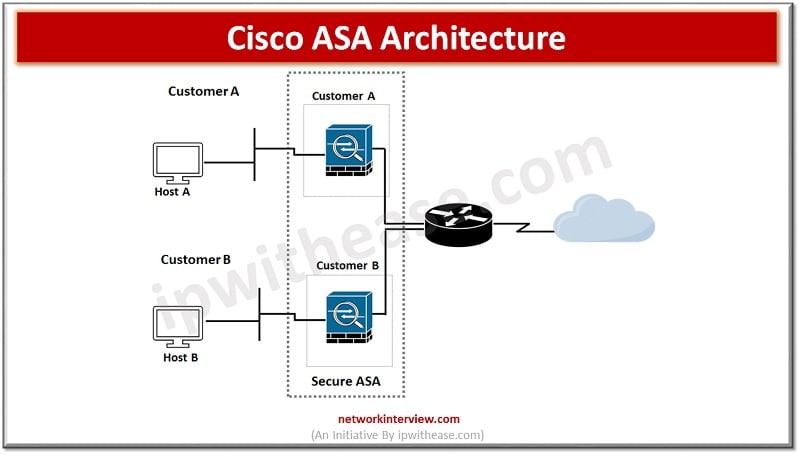
What is Cisco ASA?
Cisco ASA is a network security appliance which gives firewall, VPN, and Intrusion prevention functionality. It has extra layers of security feature by application of advanced threat protection and behaviour analysis. It can detect threats in real time and block them before they cause damage to the network. Well suite for small and large enterprises as well as wired and wireless networks both. It has high throughput and low latency.
Cisco ASA firewalls were designed to prevent all external traffic from entering into the network. ASA allows stateful inspection by saving session information so that when a valid response comes back, it can recognize and permit traffic. In addition, they provide network address translation or port address translation for network protection.
Features of Cisco ASA
- Cisco ASA provides stateful tracking of packet if it is generated from higher security level to low security level
- It can perform static routing, default routing and dynamic routing using EIGRP, OSPF and RIP protocols
- It can operate in routed mode where it acts like a layer 3 device and need to have 2 different IP addresses on its interface and in transparent mode where it operates at layer 2 and need only single IP address
- It supports AAA services using local database or using an external server like ACS
- VPN support is also given by Cisco ASA firewall like Point to Point, IPSec VPN and SSL based VPNs
- It new version supports IPv6 protocol routing (Static and dynamic)
- It provides high availability for pair of ASA firewalls
- Advanced Malware protection
- Modular policy framework supports policy definitions at traffic flow levels
Use cases of Cisco ASA
- VPN logging
- Startup and running configuration change
- TCP port scanning
- Permitted / denied blacklisted source management
- Permitted/ denied blacklisted destination management
What is Cisco FTD?
Cisco FTD is a high end firewall appliance which is used to protect networks from intrusion attacks. It offers an extra layer of security to data centers and enterprises. Cisco FTD enables service level agreements (SLAs) to support real time in service monitoring, analysis and control of the network for optimization of performance on mobile applications.
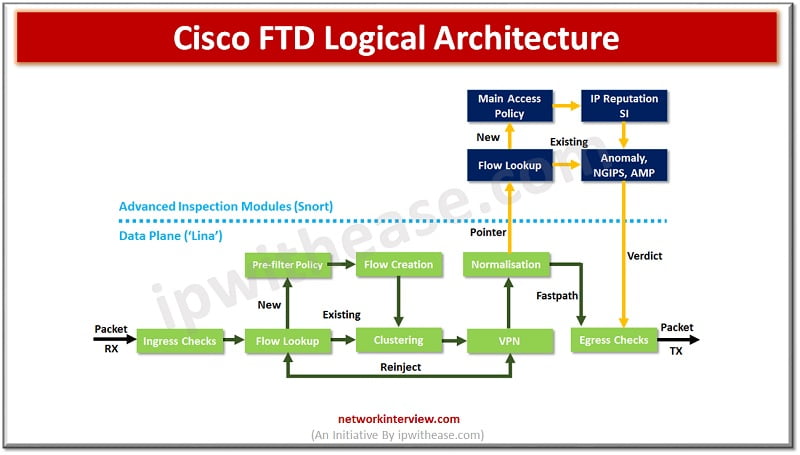
Features of Cisco FTD
- Continuous visibility across attack landscape
- Maintains data integrity and confidentiality of enterprise network with out of band segmentation
- Includes advanced threat prevention from malware, ransomware, phishing attacks, and other exploits.
- Architecture to support multi-tenant deployments
- Network protection from insider attack using Cisco Identity services engine (ISE).
Use cases of Cisco FTD
- Logging security events
- Intrusion detection and prevention
- URL filtering
- Malware protection
Comparison: Cisco ASA and Cisco FTD
Below table summarizes the differences between the two types of Network Security Appliances:
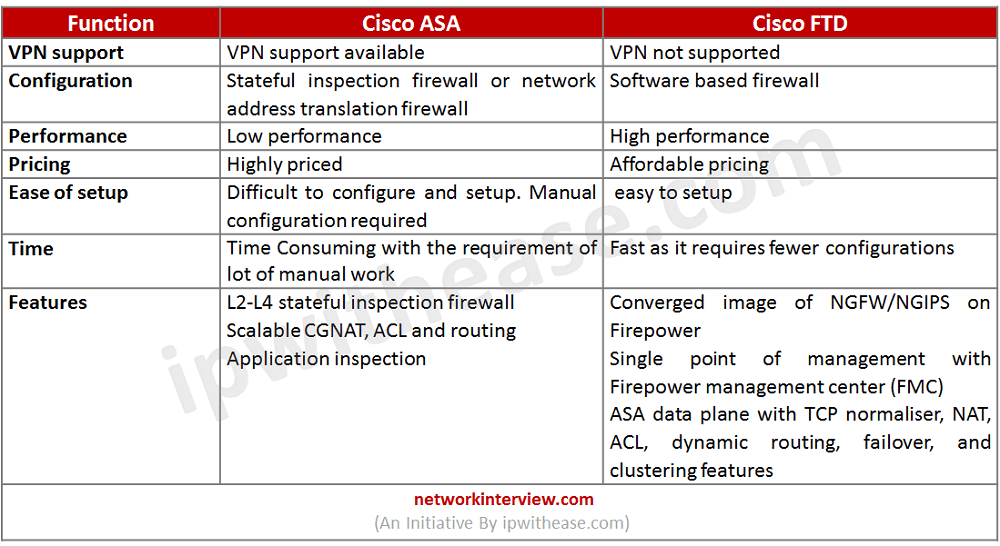
Download the comparison table: Cisco ASA vs Cisco FTD
Final Words
The primary dissimilarity between Cisco FTD and ASA is that while ASA allows users to access VPN, IDS, IPS, anti-malware, and anti-virus facilities, these amenities are absent in Cisco FTD. However, when it comes to performance, FTD is capable of replacing ASA with ease.
Continue Reading:
Cisco PIX vs Cisco ASA Firewall
Intro to Cisco FTD Firewall (Firepower Threat Defense)
Are you preparing for your next interview?
Please check our e-store for e-book on Cisco ASA Interview Q&A. All the e-books are in easy to understand PDF Format, explained with relevant Diagrams (where required) for better ease of understanding.
Tag:Cisco ASA, Cisco FTD, comparison, Security



