What is CSMA/CA?
CSMA/CA stands for Carrier Multiple Access/Collision avoidance. It is a technique using which the chances of collision are decreased. In most of the cases, the collision is avoided. It is used to transmit data using 802.11 standards.
The similar technique to this is the CSMA/CD. The only difference is that, in the CSMA CD, the collision is detected whereas here we will try to avoid the collision and send the data directly without any interruptions. In the CSMA/CD, the transmission is only handled if there is a collision detected whereas it takes no actions.
Whereas in the CSMA/CA, the protocol will first check the path prior to the collision and try to avoid any collisions before it occurs. This technique will consume more data as well as will use ore amount of network traffic. This is because the protocol will first check the path by sending dummy data before it actually sends the original data. Hence, more data and network traffic are consumed.
In short, the main aim of this technique is to ensure that the data is transmitted safely and the collision is avoided. There are proper steps taken to ensure that the data does not collide. There are three main types of techniques used for collision avoidance.
Techniques:
There are 3 techniques that we can use for collision avoidance:
- Interframe space
- Contention window
- Acknowledgments
Interframe Space (IFS)
In this technique, when the channel or the medium is found idle, sender does not directly transmit the data. Instead, it will wait for a fixed amount of time called interframe space. When the previously transmitted signal will reach the previous station, it will then send the next data. During the IFS, the sent data will reach either one of the stations. If the IFS time is over and the channel is still idle, the next data is sent. In this way, there are not collision faced.
Contention windows
Contention windows will decide the time amount into various this technique is similar to the p-persistent method. The only difference is that here the random outcome will define the time slots. A number of slots are not fixed, it will completely depend on the binary exponential strategy. After the time slot is completed, when the channel is found idle, the data is transferred. A time slot will double each time whenever the station is not able to detect any of idle channel.
When the channel is found busy, the process isn’t restarted instead it will restart the timer and follow entire process again.
Acknowledgment
Besides all the measures taken for not avoiding collisions, there are still some chances where the data might collude. In such cases, Acknowledgment is used. The receiver will send Acknowledgement saying that the data is received. Once the data is received, it is confirmed that the data is not destroyed.
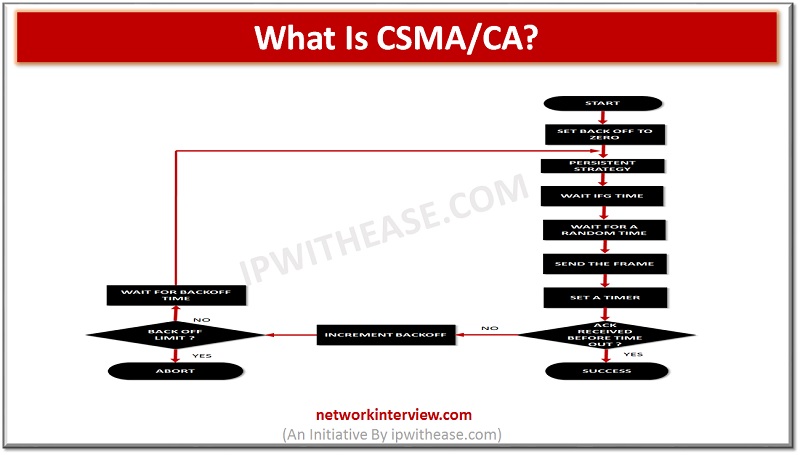
Working:
CDMA protocol working is simple. The main aim is to avoid the collision and send the data without any issues. Station will first of all check the line and see if it is idle or not. If the line is idle, it will wait for a certain amount of time. The IFS is the estimated time for the time required by the data to travel the channel.
Once, the timer is over, it will send the frame. In this way, there is last amount of chance of the collision and hence this technique is called collision avoidance technique.
If the line is found busy, the timer won’t continue instead it will restart the timer and wait for a certain amount of time again until the line is cleared.
Therefore, it is one of the best ways to send the data with least chances of a collision.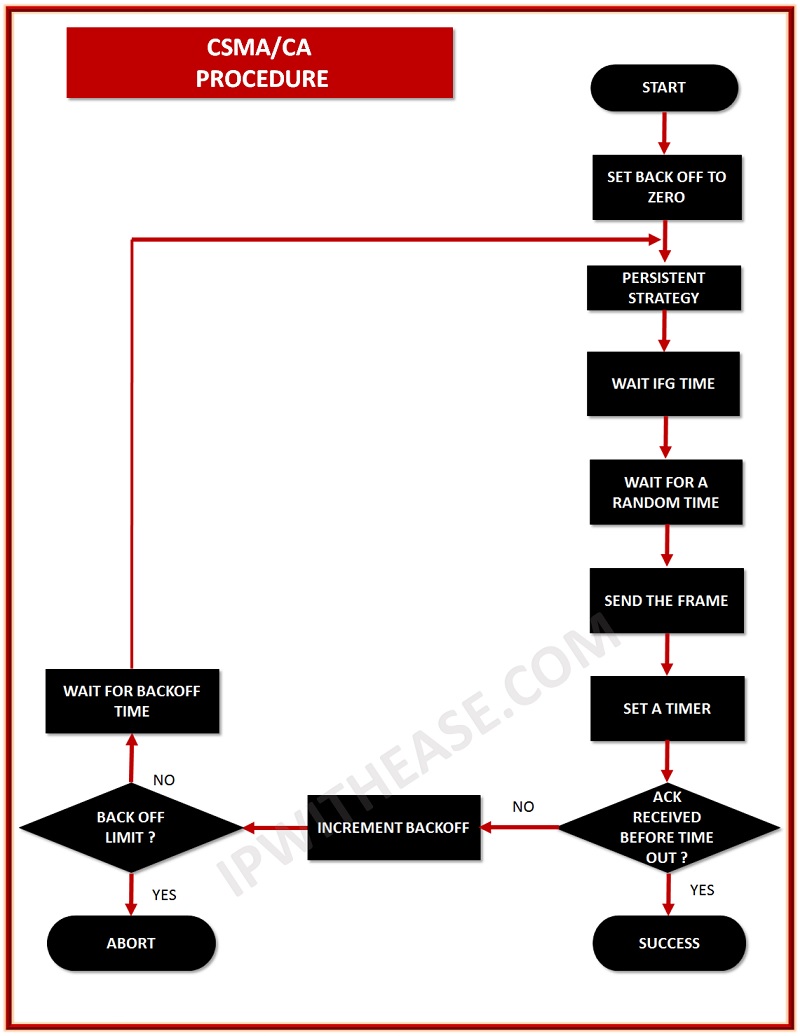
Advantages:
- There is least amount of collision and hence there are no to very fewer chances of data destruction.
- The three-technique will ensure the best level of safety and techniques to avoid the collision.
- Our data is safe and won’t corrupt while transiting data
Disadvantages:
- Time taken for data transfer is more as it will wait for a certain amount of time whenever any data is to be sent.
- The data consumption is more as there is dummy data sent to check if the frame is idle or not.
Tag:protocol



