USER ID – PALO ALTO NETWORKS
In this article, we will understand the terminologies related to USER ID and their role w.r.t login monitoring, role discovery and related nuances.
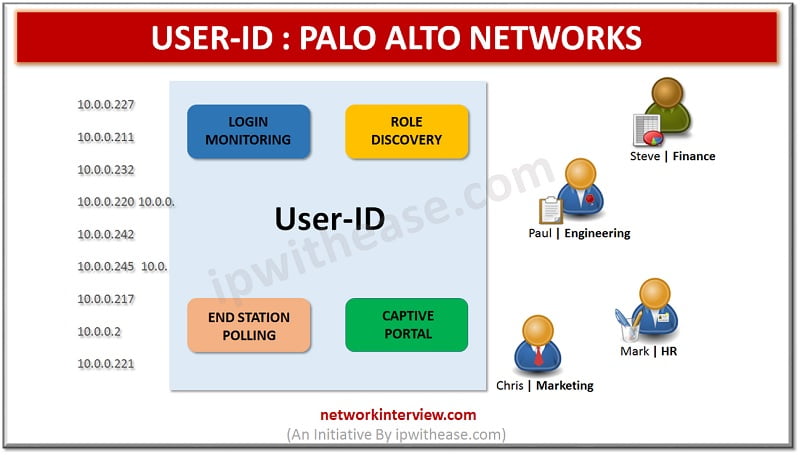
USER ID : PALO ALTO NETWORKS
User Identification is a very unique feature of Palo Alto firewall with a range of enterprise directory and terminal services to map application activity and policies to usernames and groups instead of just IP addresses. Configuring User-ID empowers the Application Command Center (ACC), App Scope, reports, and logs to comprise usernames in addition to user IP addresses.
The user identity, as opposed to an IP address, is an entire factor of an effective security key infrastructure. User-id mapping with IP address keeps track of who is using applications in your network, and who transmitted a threat or who is transferring files. This approach can strengthen security policies and reduce incident response times.
Connection Security
Connection Security uses the certificate profile to verify the identity of the User-ID agent by checking the server certificate implemented by the agent.
User Mapping
User-ID agent mapping is used to map IP address to username on the firewall. Mapping can be done with known IP address to known user name so that security rules can be enforced appropriately. User-identification defines the various techniques that are used to find the users and groups in the network and shows how user mapping and group mapping work together to enable user and group based security enforcement and visibility. User Mapping methods are as:
- Port Mapping
- Server Monitoring
- Syslog
- XFF Headers
- Authentication Policy and Captive Portal
- Global Protect
- XML API
- Client Probing
User ID Agents
User-ID Agent is used to collect logs of user mapping. To map usernames to IP addresses, User-ID agents monitor directory servers. User-ID agents send the user mappings logs to firewall. Log Collectors or Panorama and other appliances can then serve as redistribution points that forward the user mappings to other firewalls Log Collectors or Panorama. Configuration of user-ID agent in firewall (Device > User Identification > User-ID Agents) or Panorama (Panorama > User Identification) is used to collect user mappings logs, where you can configure its connections to the User-Identification agents or redistribution points.
Terminal Services Agents
In the firewall, the multiple users share the same IP address, this is where a Terminal Services (TS) agent identifies and maintain the record of individual users by assigning port ranges to each one. Terminal Services agent sends information to every connected firewall of the allocated port range so that the firewalls can enforce policy based on users and user groups. Firewall can collect username-to-port mapping information from up to 5,000 multi-user systems. The number of Terminal Services agents from which a firewall can collect the mapping information varies by firewall model.
Group Mapping
In order for Security policies profile reports to be based on users and user groups, the firewall fetches the list of groups and the corresponding list of members identified and maintained in the directory servers. Palo Alto firewall supports many vendors of LDAP directory servers such as –
- Microsoft Active Directory (AD)
- Novell eDirectory
- Sun ONE Directory Server.
LDAP server profile should be configured before group mapping configuration profile. LDAP server profile can be configured as (Device > Server Profiles > LDAP). To define policy rules based on user or group in firewall, first we need to create an LDAP server profile that defines how the firewall can connect and authenticates to the directory server. In some models, firewall does not support the directory server natively, and this can be mapped in group by XML API.
Captive Portal
Captive Portal is used to build a user-to-IP mapping on the Palo Alto firewall. Captive Portal is triggered depends on the policies for http and/or https traffic only and is triggered only for the IP addresses without existing user-to-IP mapping.
SSL/TLS Service Profile
To specify a firewall server certificate and the allowed protocols for securing redirect requests, select an SSL/TLS service profile under (Device > Certificate Management > SSL/TLS Service Profile). By selecting None, firewall uses its default certificate profile.
Authentication Profile
You can select an authentication profile (Device > Authentication Profile) to authenticate users when their traffic matches an Authentication policy rule (Policies > Authentication). Authentication profile applied in the Captive Portal Settings that reference one of the default authentication enforcement objects (Objects > Authentication).
Certificate Profile
You can select a Certificate Profile (Device > Certificate Management > Certificate Profile) to authenticate users when their traffic matches any Authentication policy rule (Policies > Authentication).
Conclusion
User-Identification technology is responsible for collecting user information from multiple sources including VPNs, WLAN controllers, captive portals, directory servers, proxies and more resources. User and group information must be directly integrated into the technology platforms that secure modern organizations with policies and profiles. It gathers information about user who is using the applications in the customer network, and who may have transmitted a threat or is transferring files, thereby strengthening security policies of organization and reducing incident response times.
Related – Palo Alto Security Profiles and Security Policies



