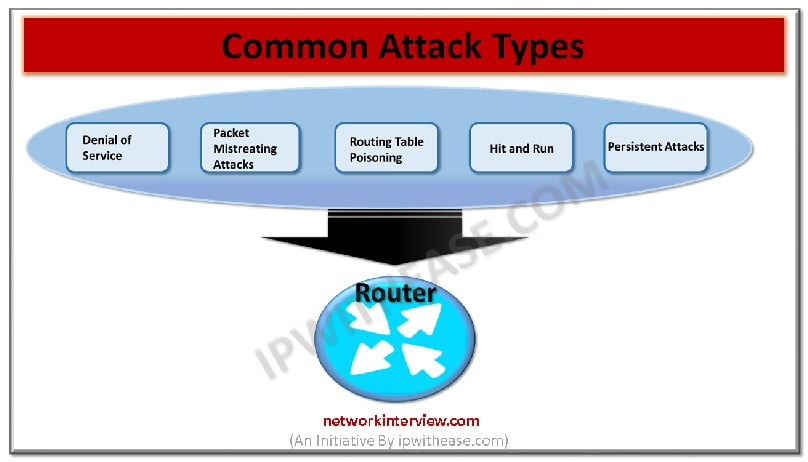
Common Types of Attacks on Routers
It is not possible to 100% prevent the router attacks. However, there are possibilities of few things that could be done for preventing the occurrence of most common attacks of routers on the network and the system. Widespread attacks are there posing threats to the large organizations. Some of these are simply carried out for stating something while the others are malicious in nature. Whatever the reason might be, the routing attacks are always harmful for networks since they lead to data damage and load harmful information packets in the routing table in one or the other manner.
Types of Attacks on Routers
Following are common router attacks:
- Denial of Service (DOS)
- Packet Mistreating Attacks (PMA)
- Routing Table Poisoning (RTP)
- Hit and Run (HAR)
- Persistent Attacks (PA)
Denial of Service attacks (DOS):
This type is most frequently used attack technique. Hackers use this technique for the purpose of disrupting a complete router and network. Series of requests is used by the attackers so that the routers networks are simply flooded with the requests of messages. Requests are send with the use of ICMP (Internet Control Message Protocol) packets. Over a short time span, multiple locations are used for sending these packets. A network might need to suffer from serious consequences due to DOS attack and the complete organization might need to suffer from standstill.
The business could be protected from DOS attack using the best method of correctly configuring the encryptions and firewall. A networking engineer services could also be used as an alternative for this purpose.
Packet mistreating attacks – Aimed at injecting the malicious code:
This router attack is the second most common one and is known as packet mistreating. This attack has similarity with DOS attacks since it also injects malicious code containing packets that are designed with the intention of confuse and disrupt the network and router.
The router is mistreated by data packets that results in mistreatment of harmful packages by the router within system. A method known as routing process is there in every router. When the harmful packages are introduced in routing process, the currently loaded packets on routing table could no longer be handled by router.
The vulnerability of router is exposed when it gets more confused since circulation of malicious data begins round the networking and it forms a loop. It further leads to major network congestion and any team of networking finds it very difficult to debug.
Related – Bridge vs Router
Routing table manipulation – Due to routing table poisoning:
Routing table performs the function of receiving or transferring information in every router. However, it is extremely vulnerable if proper encryption and protection is not there. When the routine of routing table changes drastically, it is because of routing table poisoning. For such aggressive attacks, the information packets are edited that rotate through routing table. Servers and networks need to suffer from highly harmful damage due to routing poisoning since the routing table is added with wrong data.
Hit and run attacks:
This attack is another most common form of routers attack and is generally referred as test attacks as well. It takes place when code is used for injecting the router with malicious data. In general, first attempt of the attacker goes in vain and therefore the system is attacked further. It is simple to spot the hit and run attacks since unusual activities are displayed by router on which attack is done and these activities are not the part of its usual routine. The systems could therefore secured by network professionals by acting on hack. But if left unnoticed, the hit and run attack might lead to serious results.
Persistent attacks on routers:
These attacks have much similarity with hit and run since packages of harmful data are injected by both of them in network and route that gives control to the hackers. However, unlike the hit and run attacks, the persistent attacks occur continuously till the goal is achieved by the attacker. The routing table is injected on continuous basis with harmful packets by attackers. This is the reason why persistent attack is also sometimes confused with routing table poisoning. Persistent attack on router has its overall aim to attack vulnerabilities of the networks and ultimately expose them such that the weaknesses are highlighted.
Tag:Security