How to Prevent Against MFA Fatigue Attacks?
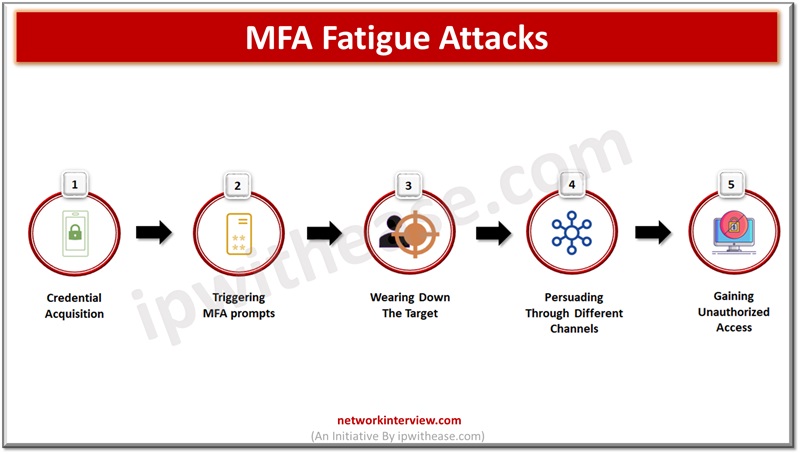
Leaked or stolen credentials are primary sources being used by cybercriminals in breach networks and steel company confidential and sensitive data. Normal authentication involving a username and password is an old technique and no longer provides protection against sophisticated attacks …