Zero Trust Security: Why It’s Essential in 2026
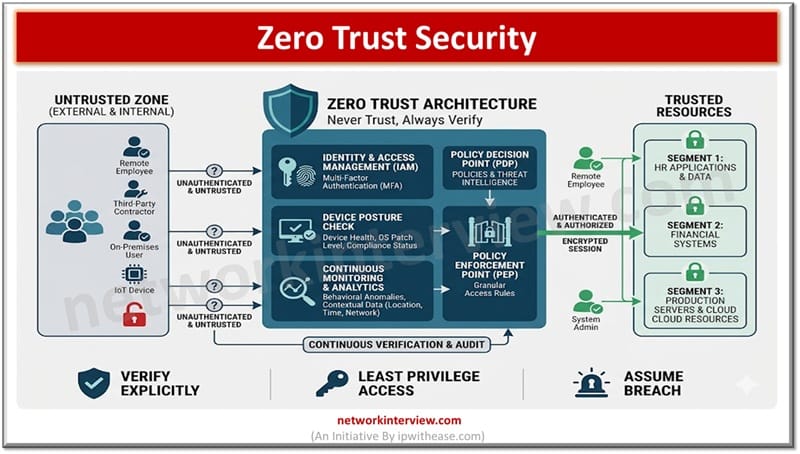
Zero trust architecture emerged as ‘No one to be trusted by default’ be inside or outside of the network. Every time a user needs to be authenticated and authorized before being granted access to any services and applications in the network.
In the traditional security model organizations focused on securing on-prem assets, firewalls, switches, routers and virtual private networks (VPNs) and all equipment resides at one place. As the corporate landscape expands and physical boundaries are diminishing very fast with hybrid digital footprint which could be on cloud, on-premises and hybrid.
The traditional approach of ‘Once trusted allow always’ no longer served the purpose and organizations moved onto ‘Verify at every step’.
In today’s article we understand about Zero trust security, and its importance in present times.
What is Zero Trust Security
Today’s network does not operate within fixed network boundaries but users are spanned across the globe and can connect from anywhere, applications are hosted on cloud, and data movement is free across ecosystems. The traditional network physical perimeter and security controls are not capable of handling, or defending such scalable networks. As organizations demand more agility, zero trust emerged as a strategy of ‘Never trust, Always Verify’.
Hybrid working, cloud based applications, adoption of SaaS created an ecosystem where trust can no longer be implicit and access / permissions need to be granted exclusively for a fix duration. Each implicit connection, unverified identity and credential, and unmanaged asset is a potential entry point for threat actors and post gaining access they can move laterally in the network.
Zero Trust Security and Its Need
Year 2025 global breach average cost rose to $4.8 million and identity-based attacks were contributors in 79% of breaches as per IBM X-Force threat intelligence report. With hybrid and multi-cloud architecture, remote working options and increased use of AI have extensively increased this number which for sure the year 2026 report will be going to present once it gets published. Zero trust security is inevitable as the only approach to protect the organization’s digital landscape.
As per Gartner approximately 60% of the organizations by 2026 will stop using 16 VPN and replace it with Zero trust network architecture (ZTNA) implementations.
- Organizations will move from perimeter based security to defense in depth and continuity and intelligent security paradigm.
- Zero-trust, adaptive access, and adaptive WAFs will emphasize and establish identity (asset and user) as a new boundary for security and risk based access.
- Zero trust security will be embedded as a crucial component in daily operations, visibility across applications, systems and users will be enhanced.
- Continuous authentication and authorization will be a new standard in which the system will examine behavior patterns to understand the intent rather than just tracking on credential based login.
- The internal networks are equally at risk due to development in the attack surface.
- The adoption of AI, cloud applications have given rise to shadow IT and Shadow AI.
Unified experiences are more important given users no longer experience juggling with VPNs, multiple credentials, MFA mechanisms and application gateways rather it would be a seamless single flow access journey. All the more context is more crucial so before allowing access to variables like device health, its location, time, previous behavior history everything will be reviewed and verified.
Secure access will be crucial when it comes to accessing customer platforms / applications. Regulatory industry driven businesses such as banking, healthcare, retail etc. will be focusing more on risk based access to safeguard customer data keeping in mind reducing the complexity arisen due to digital fraud cases.
Adaptive WAFs will take precedence in the year 2026 where in WAF will adapt to new rules in real time, identify deviations and learn from traffic patterns to be ready with application aware security.
Tag:Security